

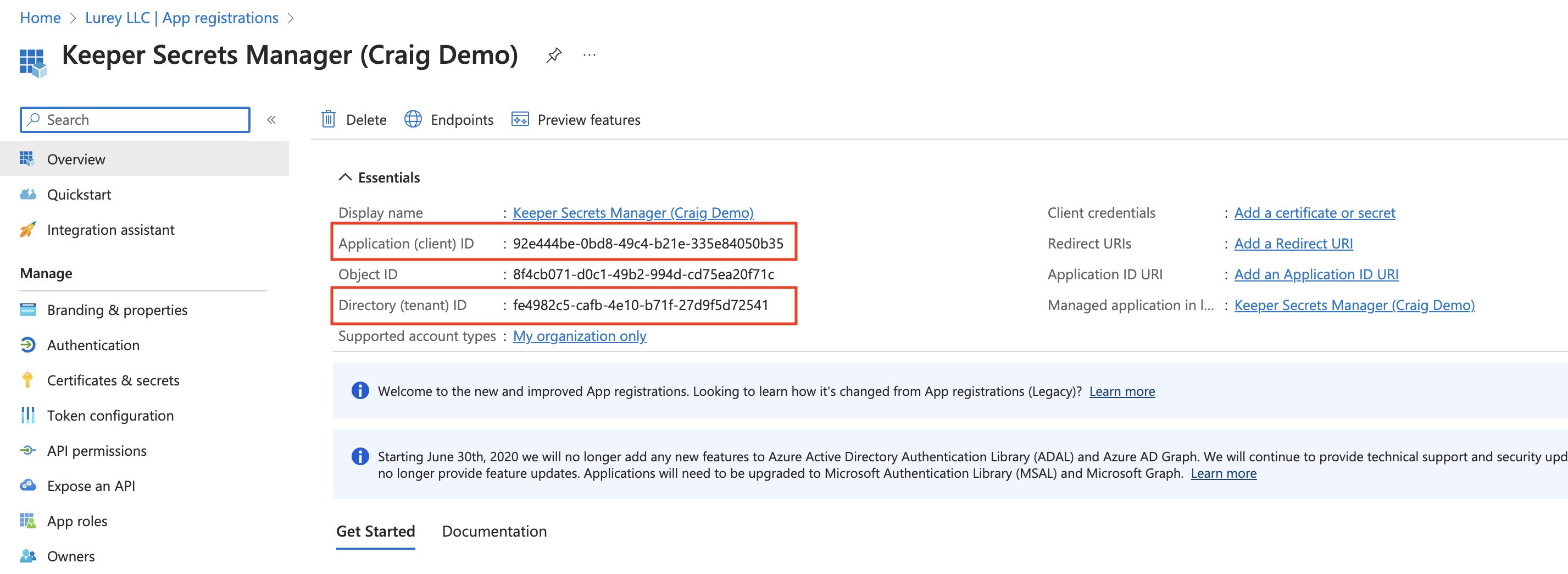
Create Application
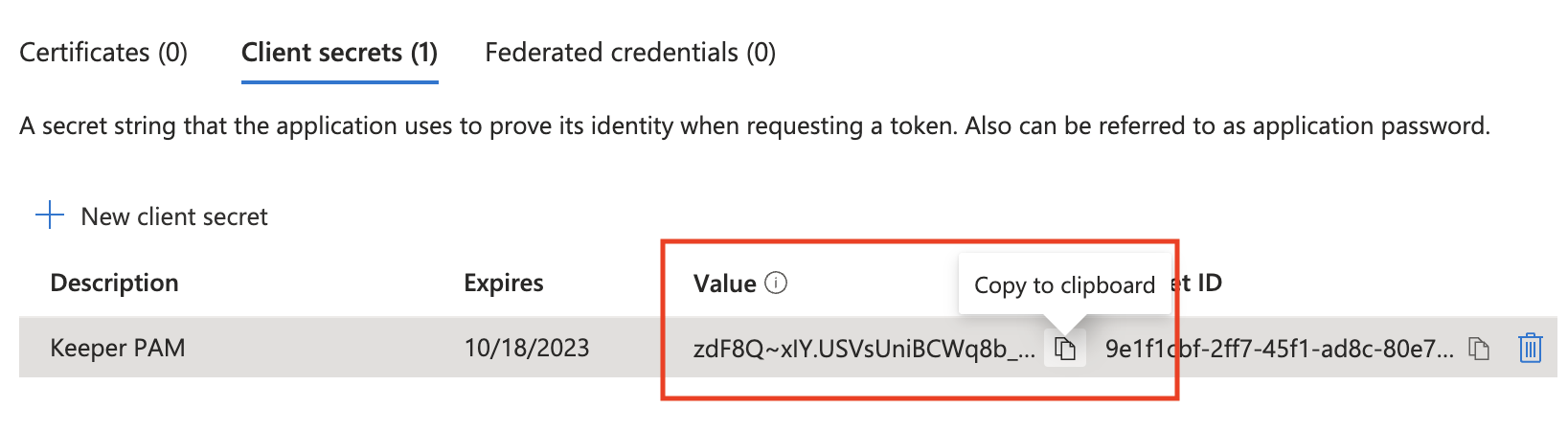
Client Secret

Assign Administrator Role to Keeper Application
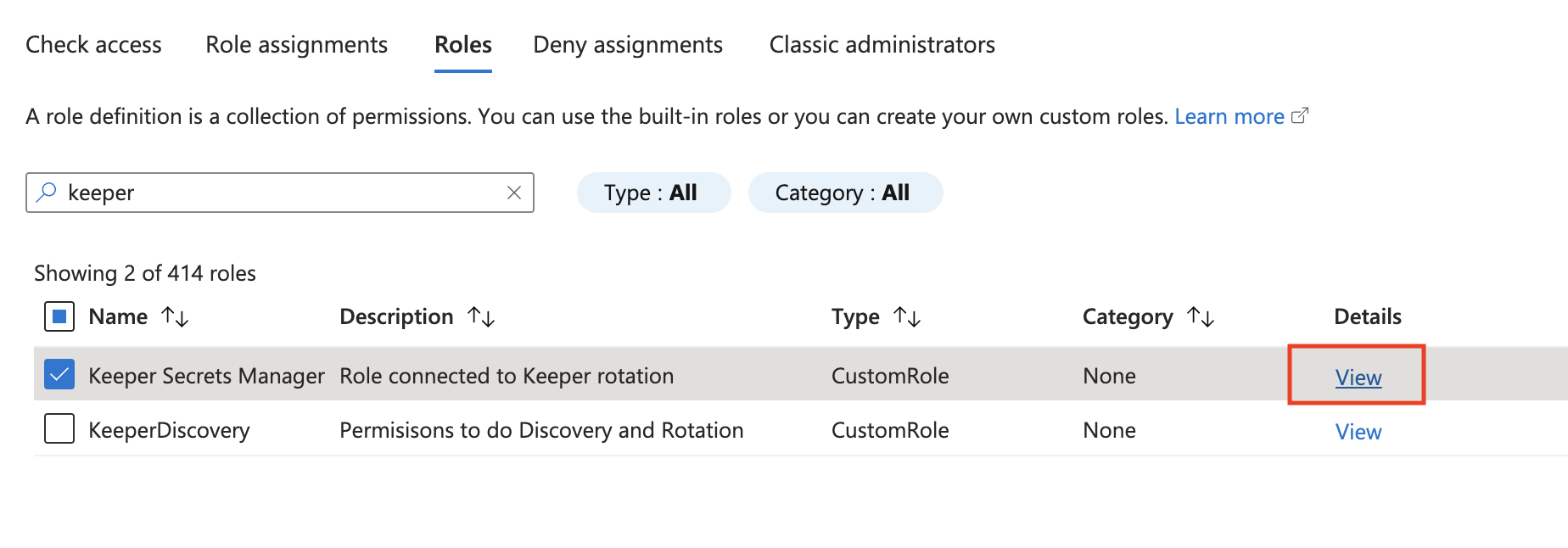
Role
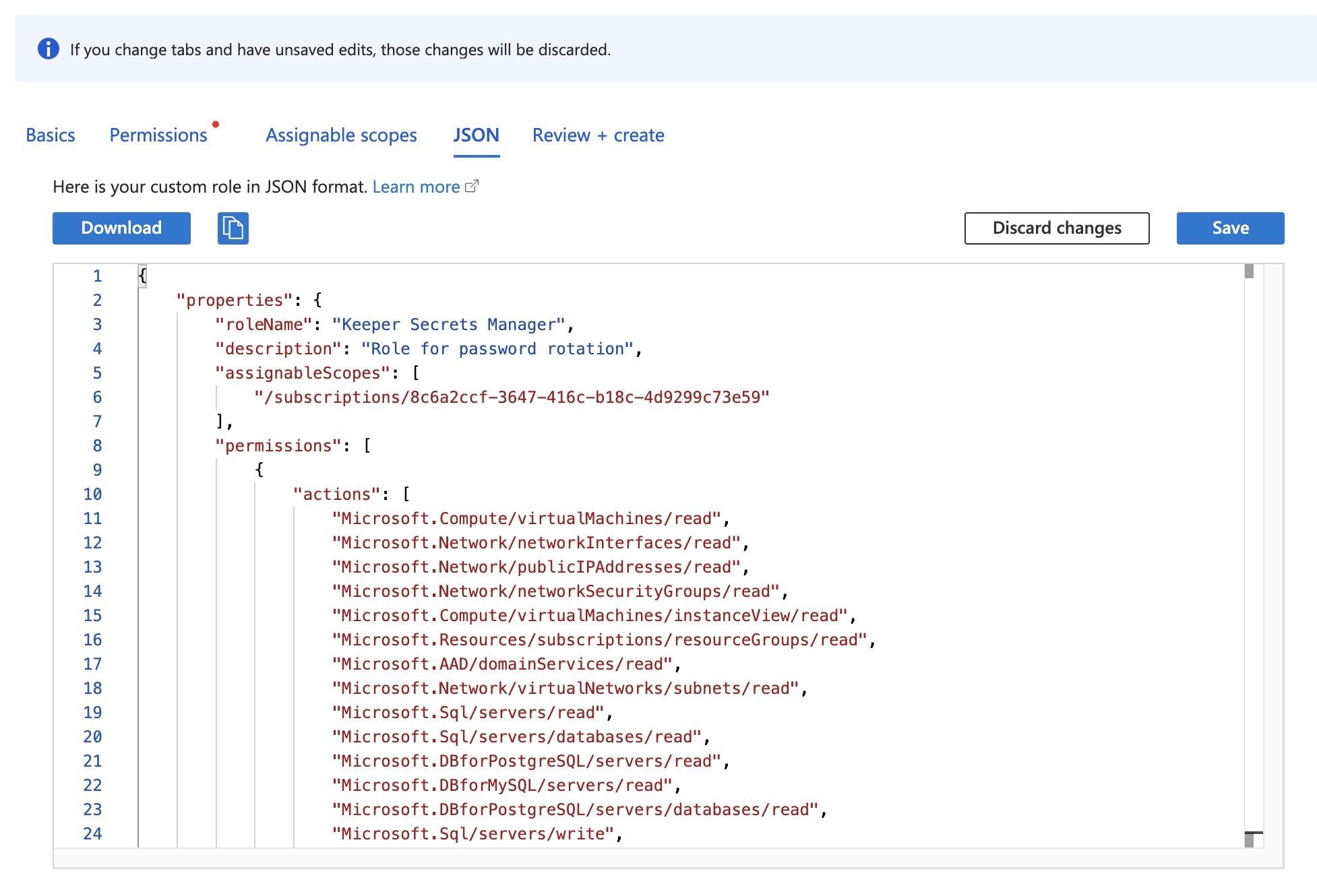
Create Azure Custom Role

Assign Role to Keeper Secrets Manager application member
| Field | Description |
|---|---|
| Rotation | If enabled, allow rotations on privileged user users managed by this PAM configuration |
| Connections | If enabled, allow connections on resources managed by this PAM configuration |
| Remote Browser Isolation (RBI) | If enabled, allow RBI sessions on resources managed by this PAM configuration |
| Tunneling | If enabled, allow tunnels on resources managed by this PAM configuration |
| Graphical Session Recording | If enabled, visual playback sessions will be recorded for all connections and RBI sessions |
| Text Session Recording (TypeScript) | If enabled, text input and output logs will be logged for all connections and RBI sessions |