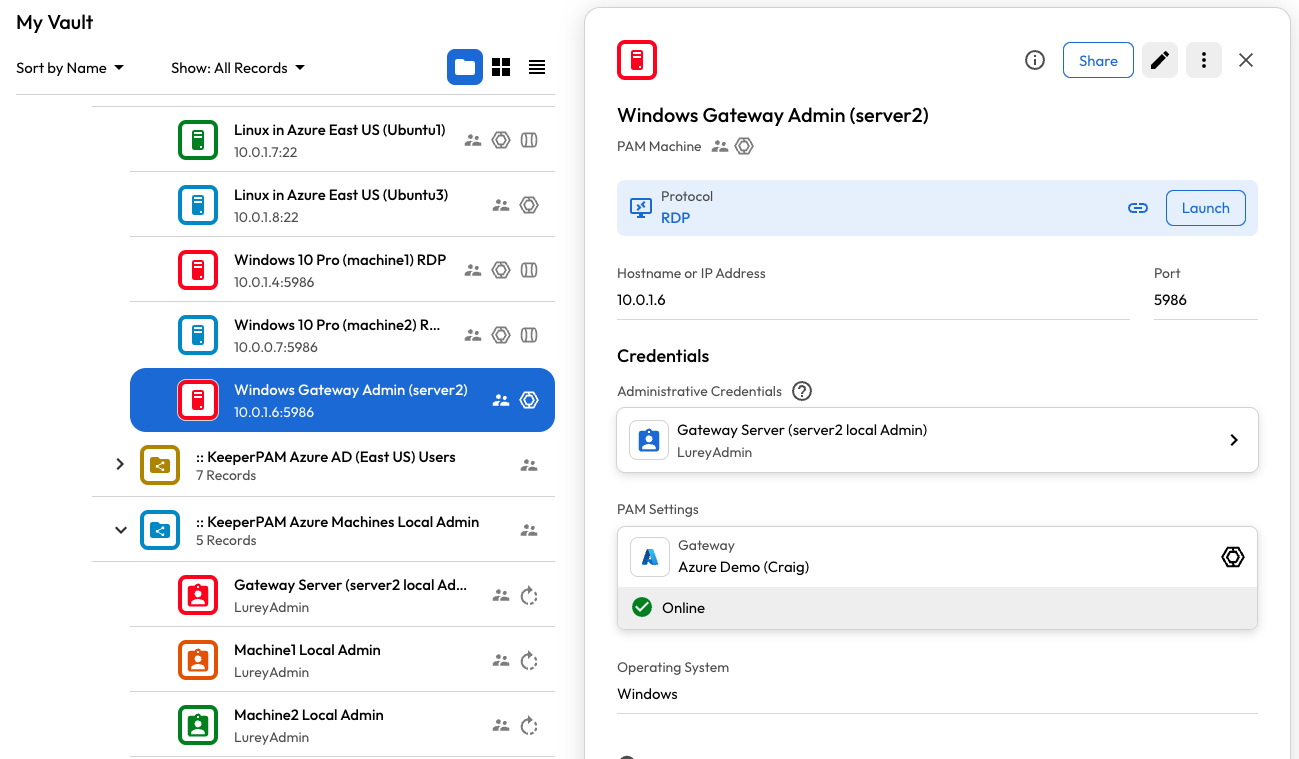
Example of Azure Windows VM
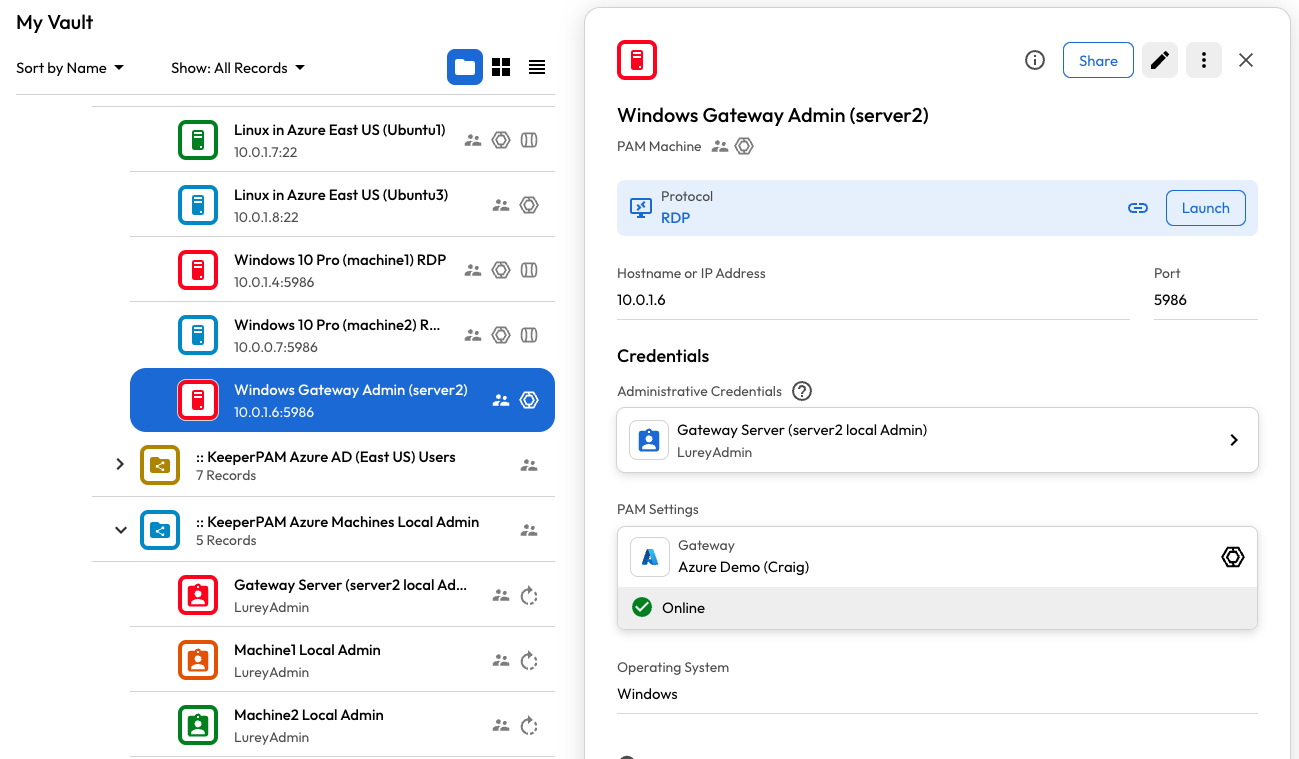
Example of Azure Windows VM
| Field | Description | Value |
|---|---|---|
| Title (Required) | Title of the PAM Machine Record | Windows VM |
| Hostname or IP Address (Required) | Address or RDP endpoint or Server name of the Machine Resource | 10.0.1.4 |
| Port (Required) | Port to connect to the Azure VM for rotation. 22 for SSH, 5986 for WinRM | 5986 |
| Operating System | The target's Operating System | Set to: Windows |
| Instance Name | Azure or AWS Instance Name | Required if AWS/Azure Machinewebserver-prod-01 |
| Instance ID | Azure or AWS Instance ID | Required if AWS/Azure Machine |
| Provider Group | Azure or AWS Provider Group | Required if a managed Azure Machine |
| Provider Region | Azure or AWS Provider Region | Required if a managed AWS Machine |
| Field | Description | Required |
|---|---|---|
| PAM Configuration | Associated PAM Configuration record which defines the environment | Required - This is the PAM configuration you created in the prerequisites |
| Administrative Credential Record | Linked PAM User credential used for connection and administrative operations | Required Visit this section for more details |
| Protocol | Native protocol used for connecting from the Gateway to the target | Required - for this example: "RDP" |
| Session Recording | Options for recording sessions and typescripts | See session recording |
| Connection Parameters | Connection-specific protocol settings which can vary based on the protocol type | See this section for RDP protocol settings We recommend specifying the Connection Port at a minimum. E.g. "3389" for RDP. |