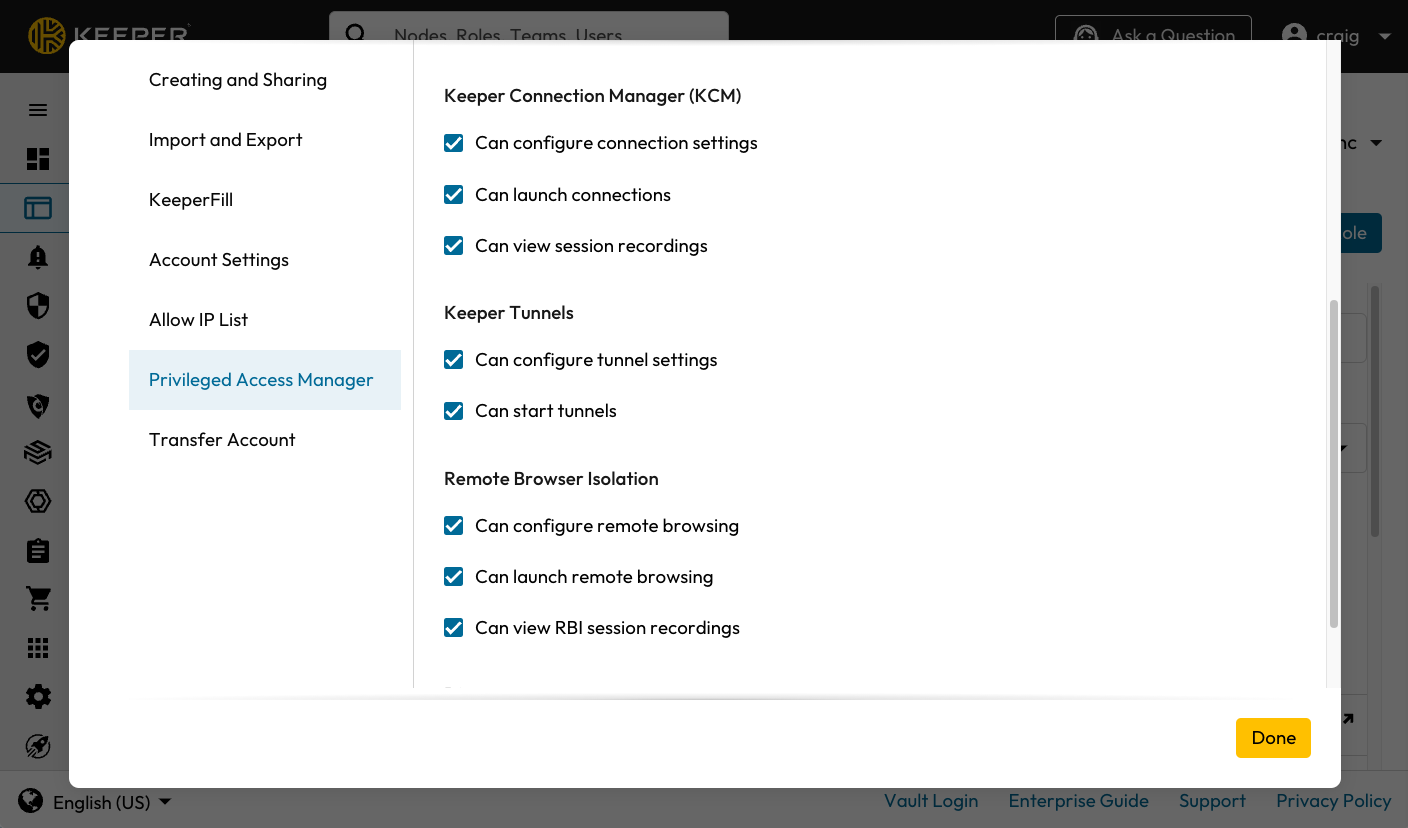
Enforcement Policies for Tunnels
| Enforcement Policy | Commander Enforcement Policy | Definition |
|---|---|---|
| Can configure tunnel settings | | Allow users to configure Tunnel settings on PAM Machine, PAM Directory, PAM Database and PAM Configuration Records Types |
| Can start tunnels | | Allow users to start tunnels on PAM Machine, PAM Directory and PAM Database Record Types |
| PAM Record Type | Target Endpoint type |
|---|---|
| PAM Machine | Windows/MacOS/Linux Machines, EC2 Instances, Azure VMs |
| PAM Database | MySQL, PostgreSQL, SQL Server, MongoDB, MariaDB, Oracle |
| PAM Directory | Active Directory, OpenLDAP |
Tunnel Settings in a KeeperPAM Record
| Field | Definition |
|---|---|
| PAM Configuration | Required This is the PAM Configuration that contains the details of your target infrastructure and provides access to the target configured on the PAM Record |
| Enable Tunnel | Required When checked, enable tunnels for this record |
| Generate Local Port | When checked, Keeper will decide which local port to use based on available open ports. |
| Reuse Last Port | When checked, the last used tunnel port will be reused. This ensures that the port number doesn't change every time. |
| Remote Tunnel Port | Required The port which is used to connect from the Keeper Gateway to the target infrastructure. If not specified, the gateway will use the "rotation port" specified in the Keeper record view. |
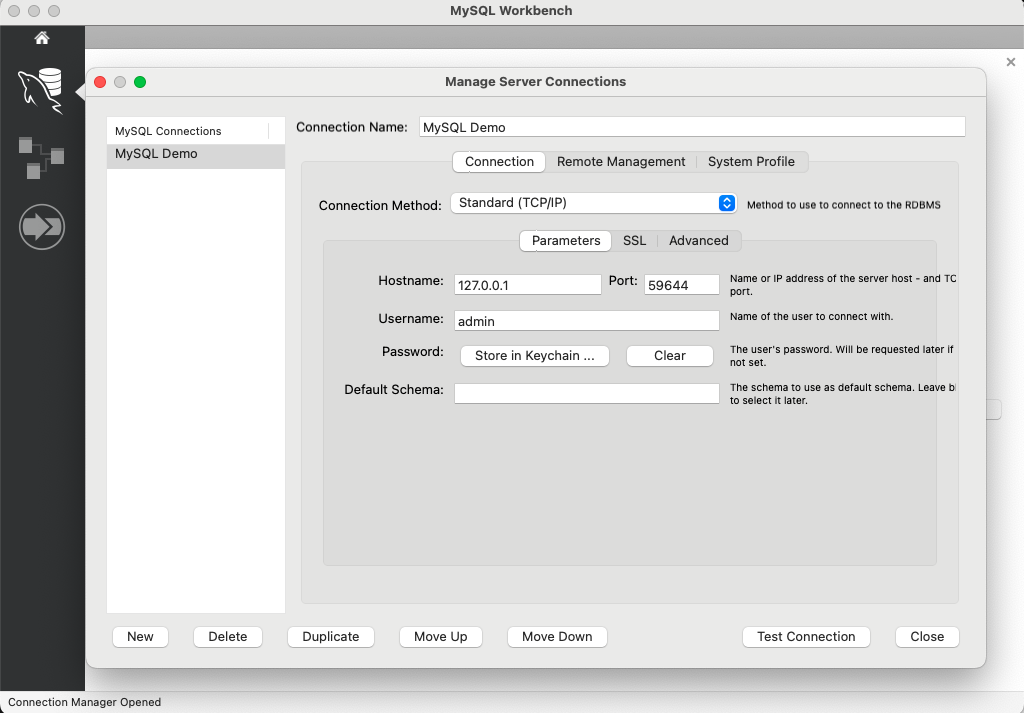
MySQL Workbench with a Local Tunnel