

| PAM Record Type | Supported Account Types |
|---|---|
| PAM User | Local Windows accounts, Domain accounts, Active Directory users, IAM users, database accounts, SaaS accounts, Linux accounts, SSH Private Keys |
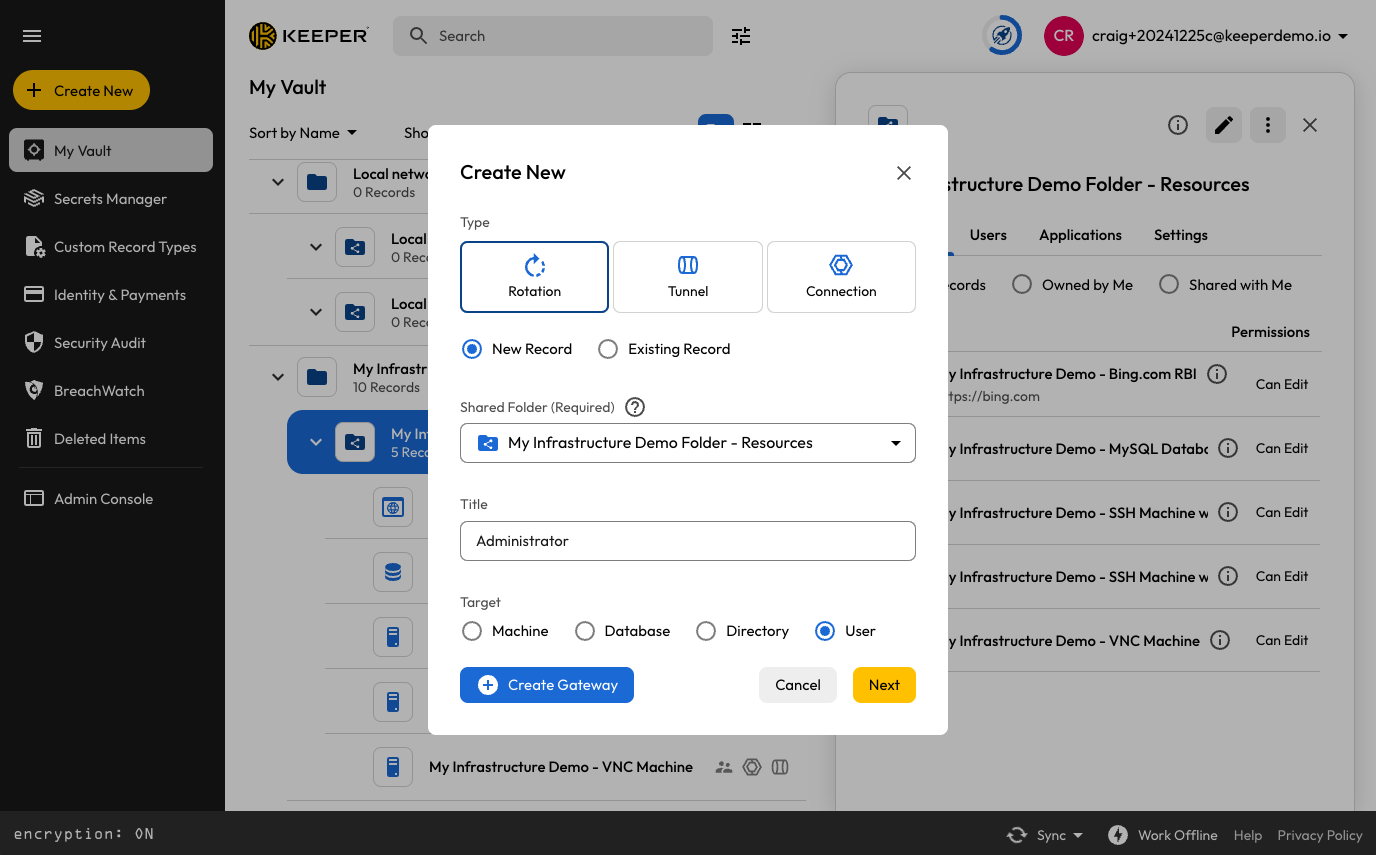
Creating a PAM User
| Field | Description | Notes |
|---|---|---|
| Login | Username; exact context and format depends on the associated resource. See Note (1) below. | Required Examples: usernameusername@domainDOMAIN\username |
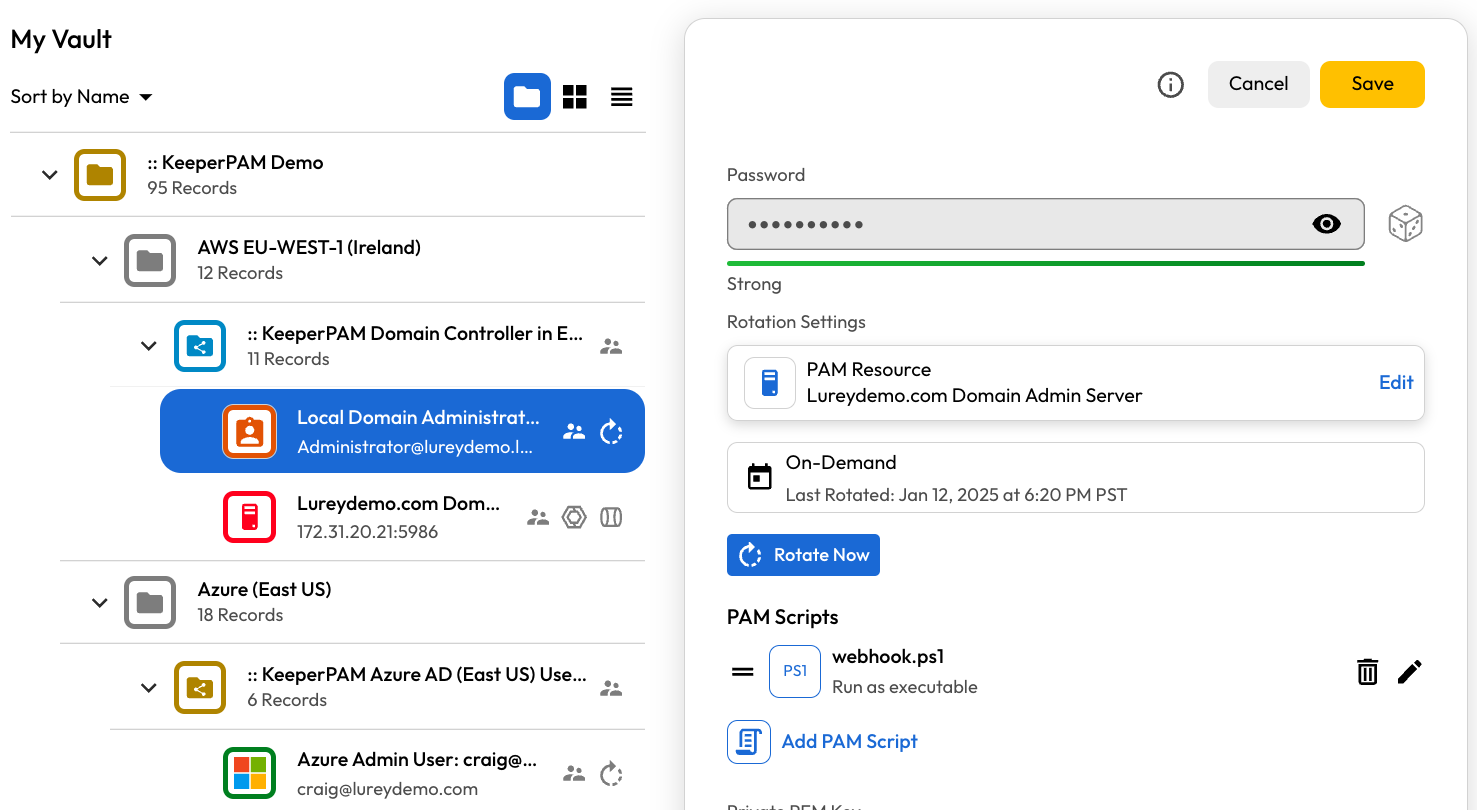
| Password | Password of the user | Can be rotated |
| Private PEM Key | PEM-encoded SSH Private Key associated with user. | Can be rotated |
| Private Key Passphrase | Used to decrypt the SSH Private Key for use in connections. | Optional passphrase that encrypts the SSH key. Recommended to avoid using symbols that require shell escaping. |
| Public Key | SSH public key, including CA-signed SSH certificates | Used for certificate-based authentication. See this page for example usage. |
| Distinguished Name | Distinguished name; used if associated with a PAM Directory | Required only when the User is managed by a directory If left blank, defaults are attempted depending on the provider type |
| Managed User | Flag for accounts that are managed by the AWS or Azure IAM systems | Set by Keeper Discovery to indicate that the password cannot be rotated. For example, AWS token-based auth. |
| Connect Database | Used in certain scenarios if a database name is needed | Edge cases, e.g. using LDAP to connect to a MySQL database |
PAM User record editing
| Field | Description | Required |
|---|---|---|
| Rotation Type | Specifies which type of rotation is being performed (and which protocol is utilized). | Required "General", "IAM User", "SaaS Account" or "Run PAM Scripts Only". See below for details. |
| PAM Resource | For General rotation type, specifies the PAM Resource record which can provide the necessary privilege. For IAM User rotation type, specifies the PAM Configuration utilizing cloud APIs. | Required only for "General" and "IAM User" rotation types |
| Rotation Schedule | Rotation can be performed on-demand or on a specific schedule. | For advanced scheduling, see the cron spec. |
| Password Complexity | Applies to password-based rotations, not PEM keys. | Select "Show More" to control special characters and symbols. |

Custom Schedule
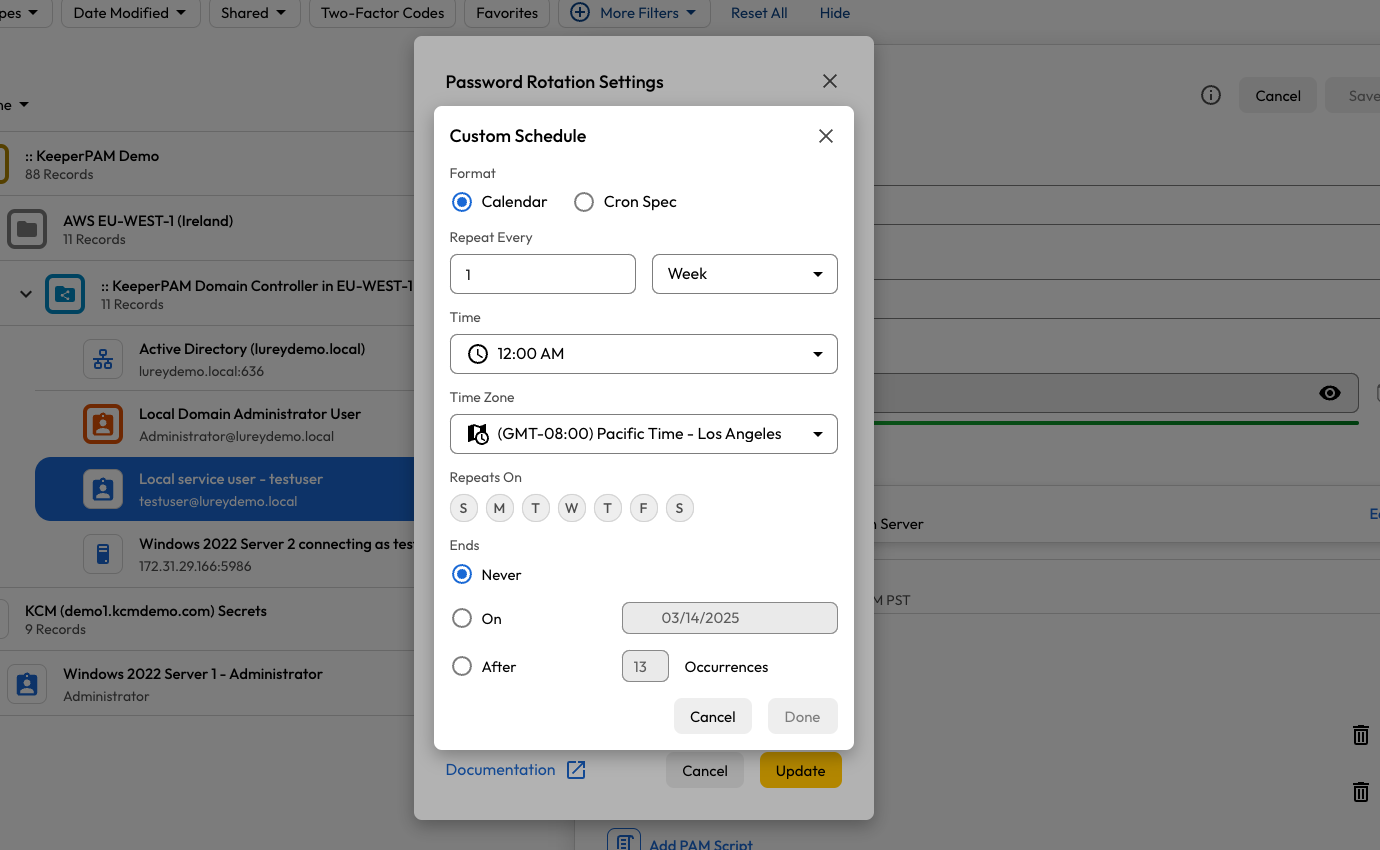
Calendar Settings
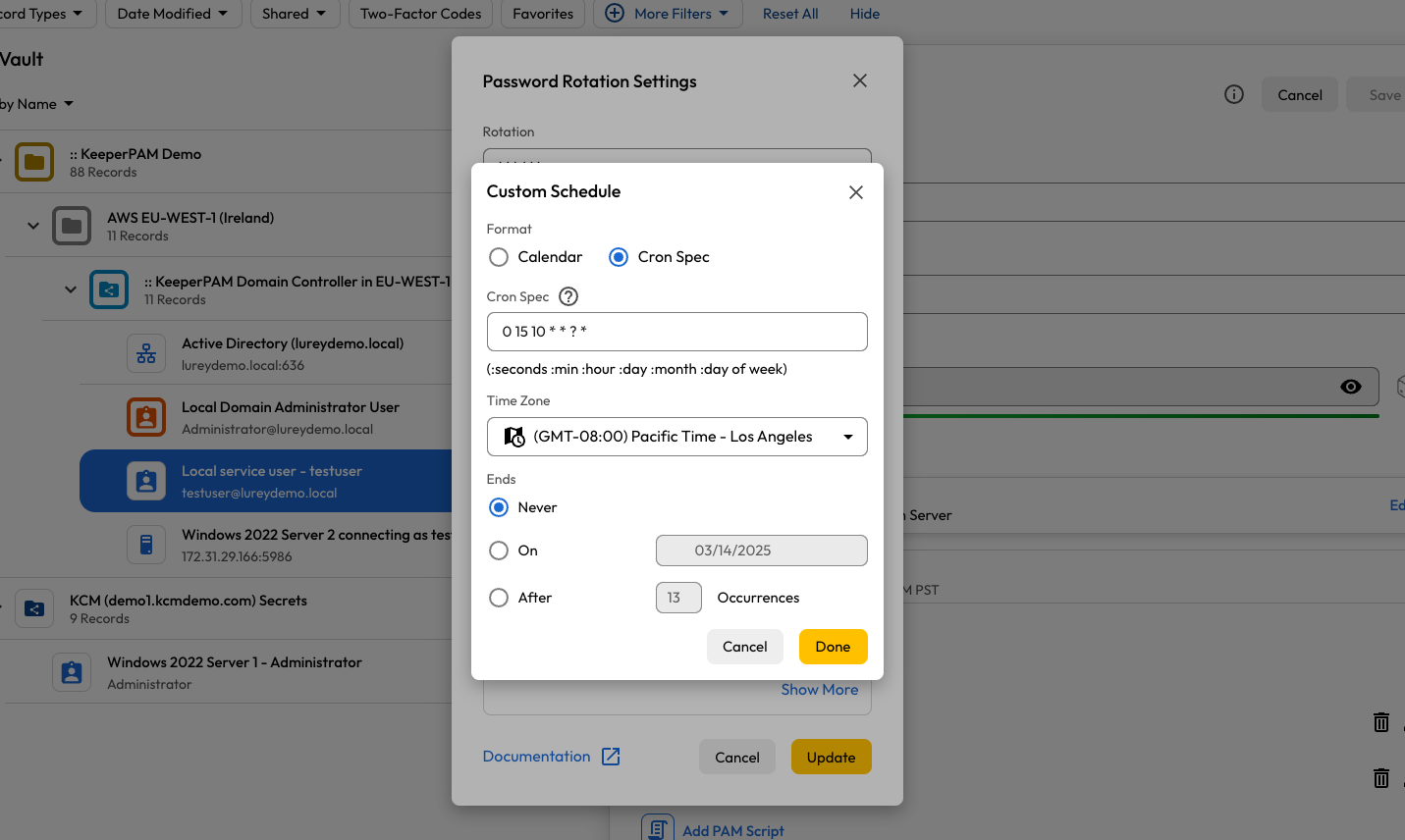
Cron Spec

Rotation Resource
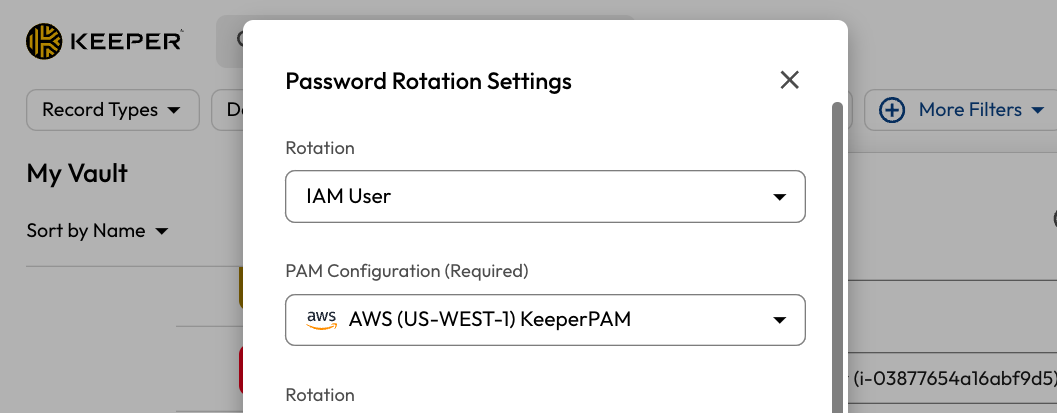
IAM User rotation type
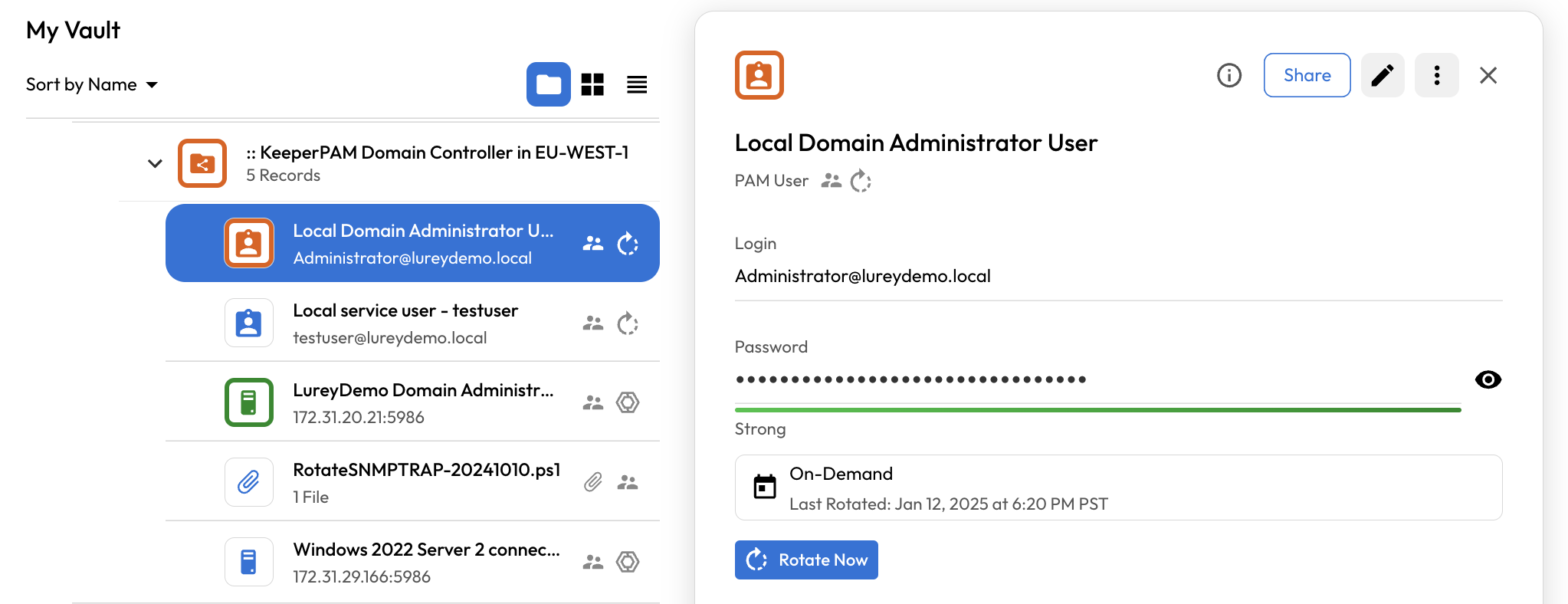
Windows Domain Admin User
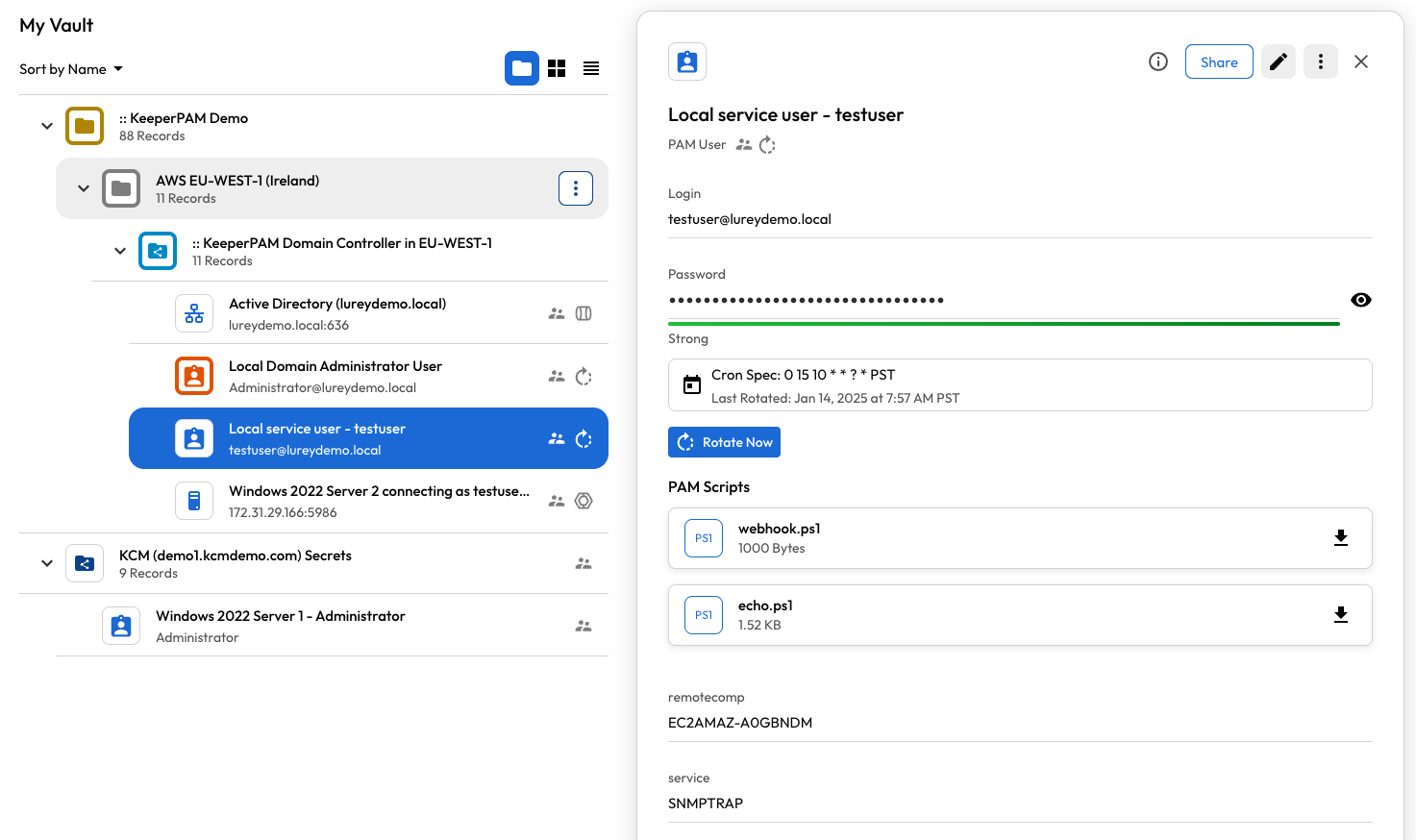
Windows Domain User with post-rotation scripts

AWS IAM User
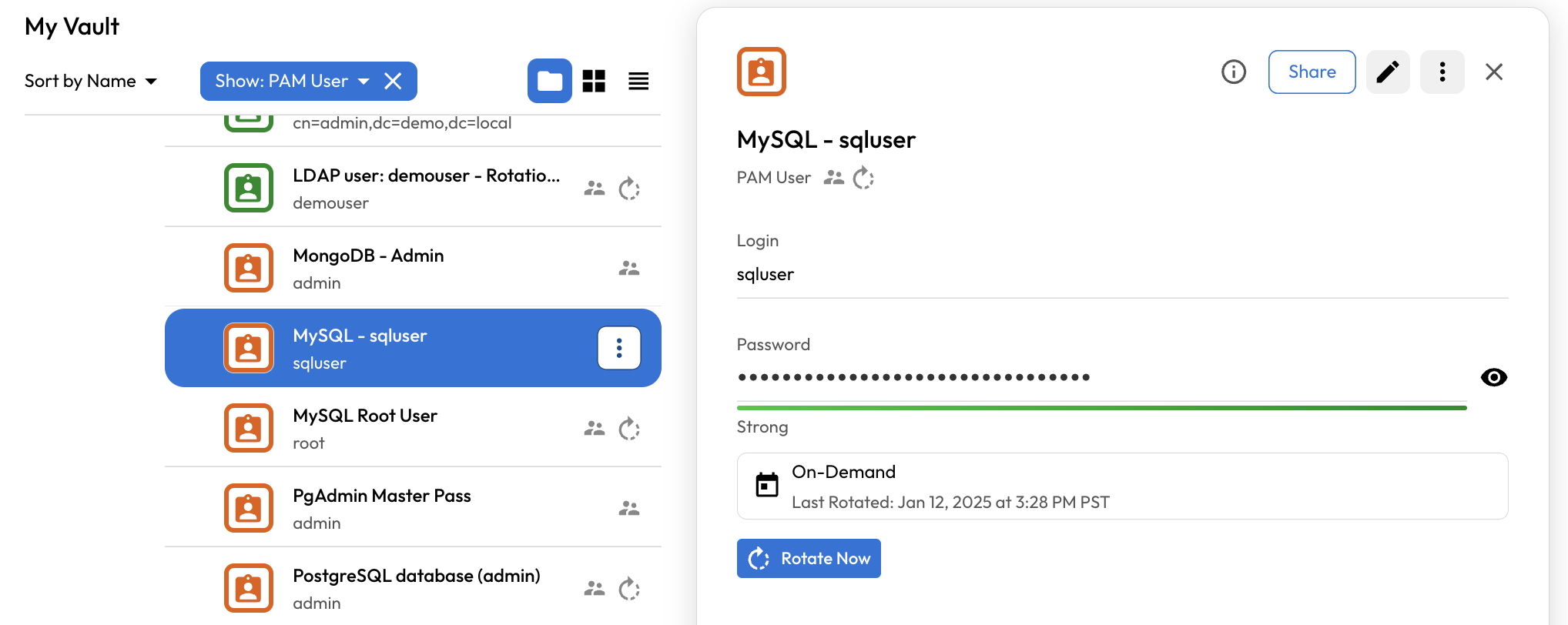
Database user
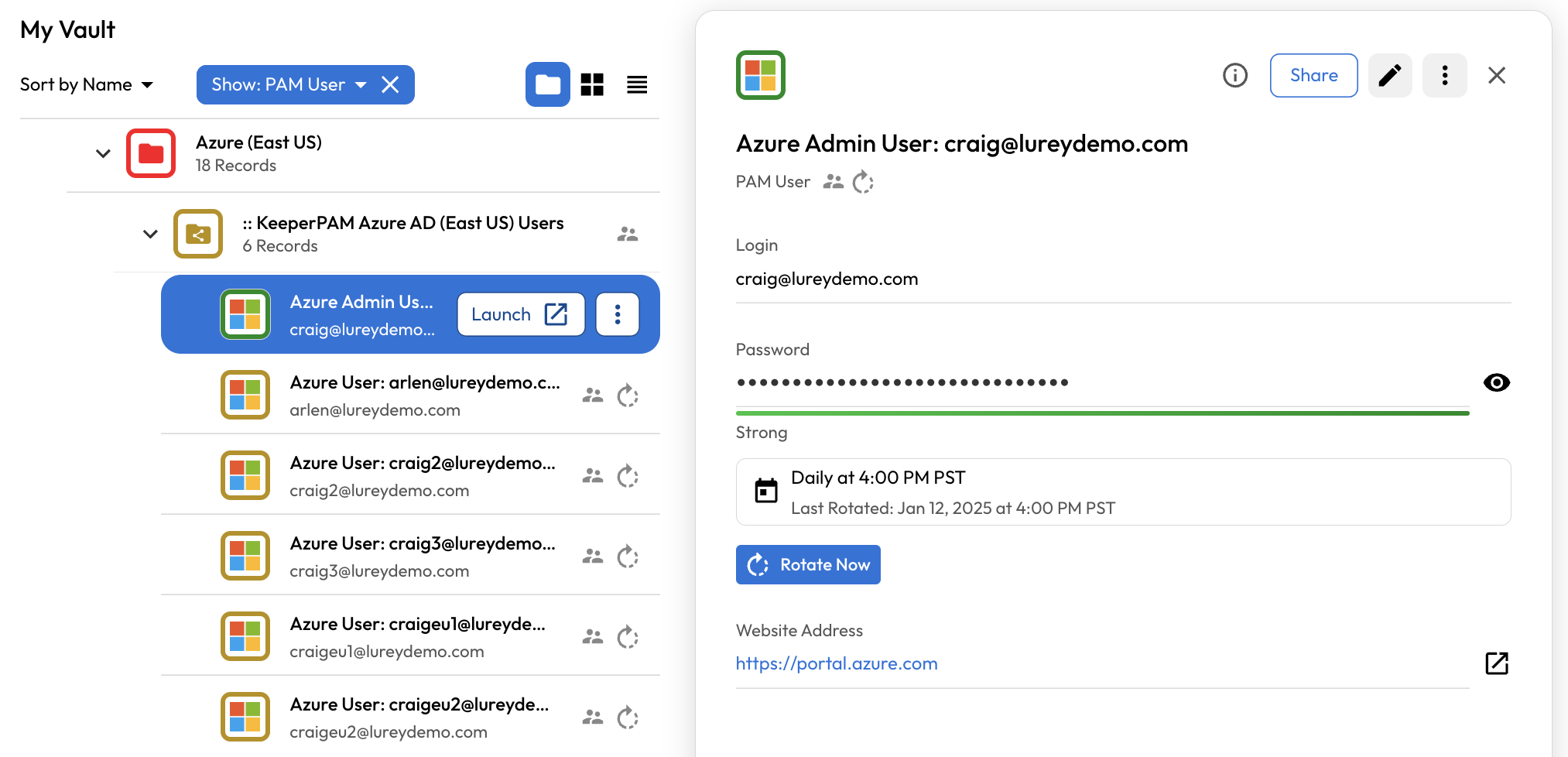
Azure AD User