

| Property Name | Default Value | Description |
|---|---|---|
aws-discovery-ksm-config | false | Enable the use of Cloud Connect credentials from KSM connected vaults |

Create a new record to attach your pem file to
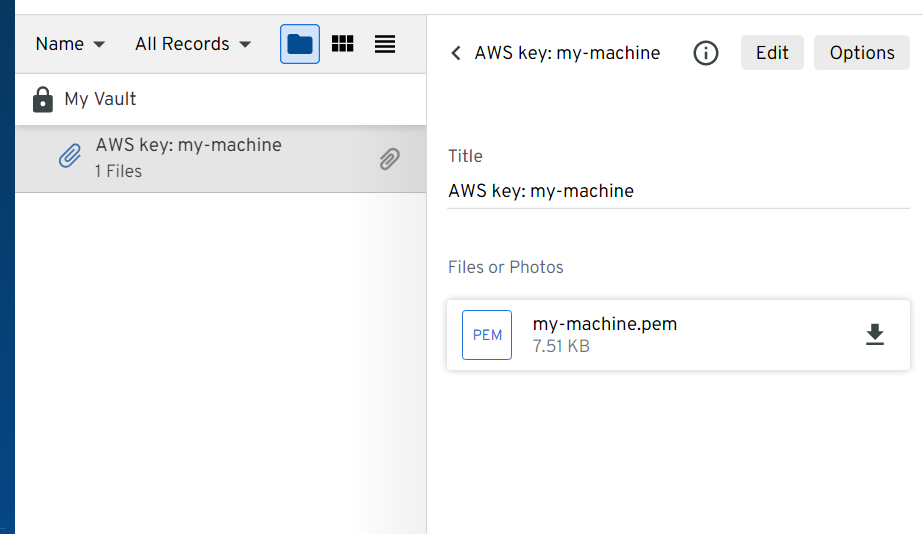
Attach your pem file to the new record
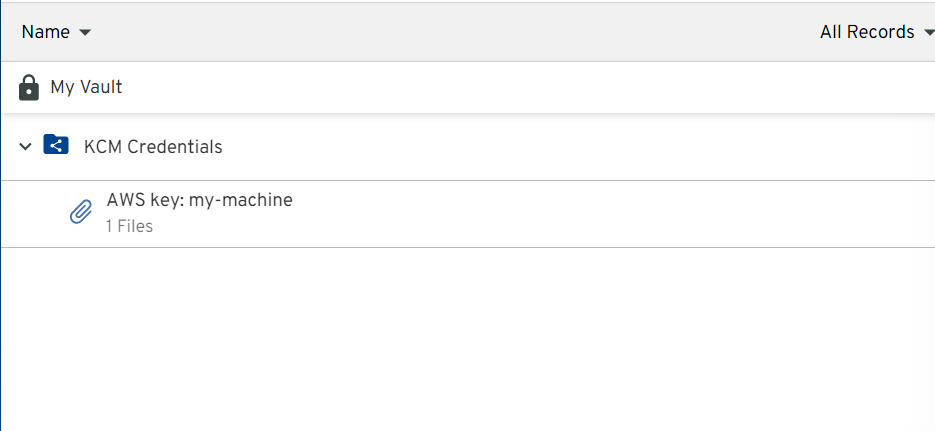
Move the new record to a shared folder attached to Secrets Manager
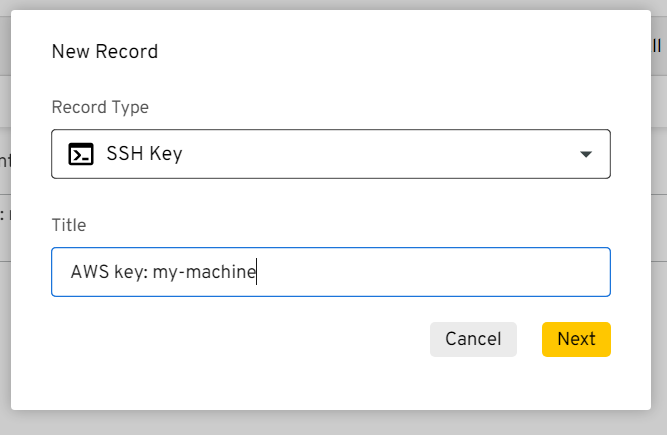
Create a new record with a private key field (standard SSH type works)
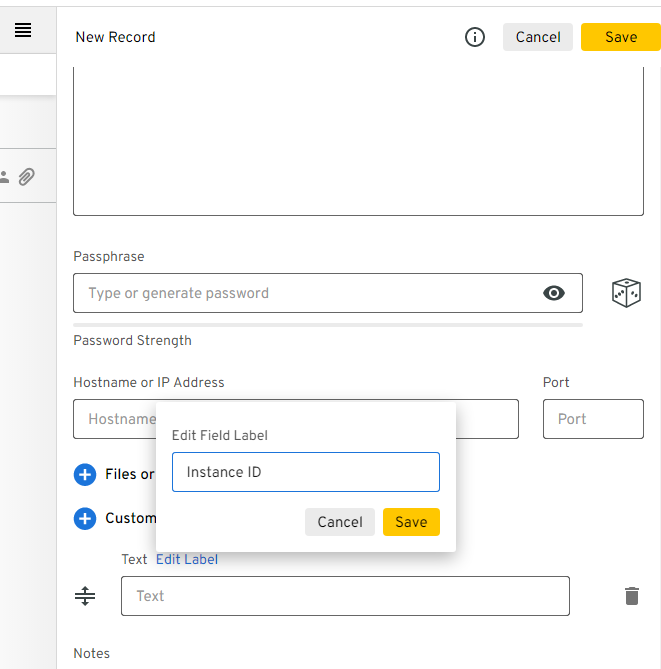
Add a custom text field labeled "ID Instance"
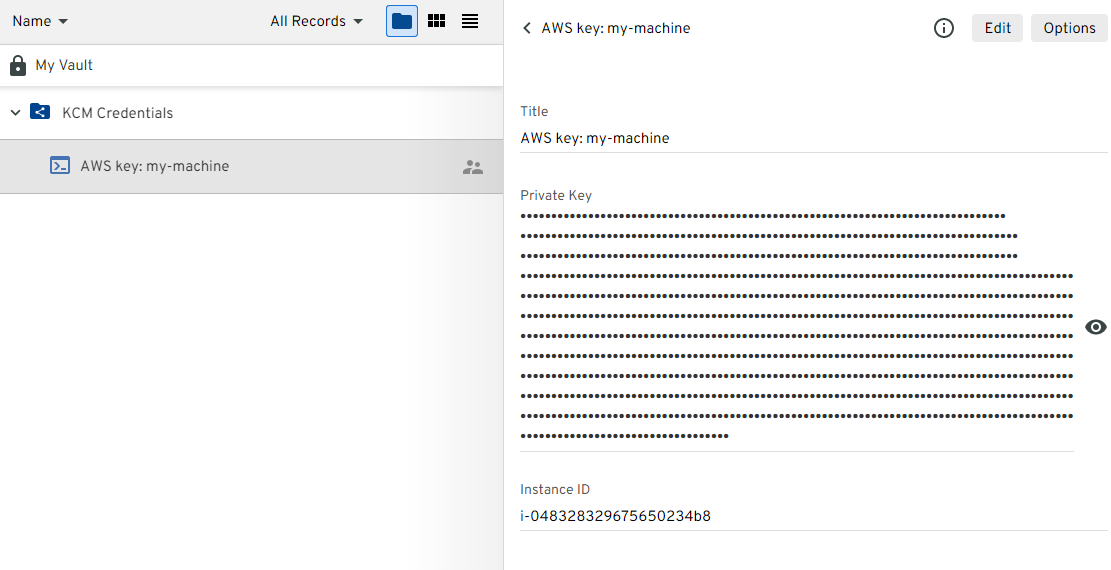
Fill in the record details and place the record in a Secrets Manager accessible shared folder