


Create a New Google Cloud Project
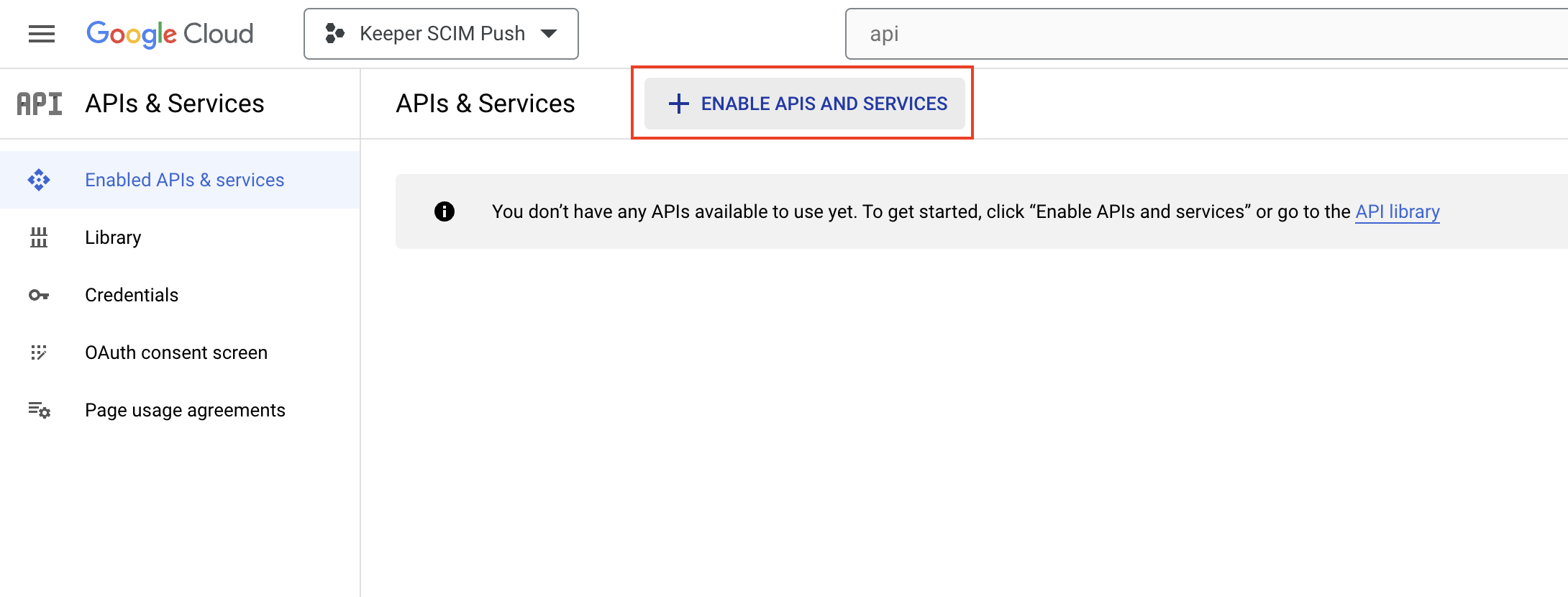
Enable APIs and Services
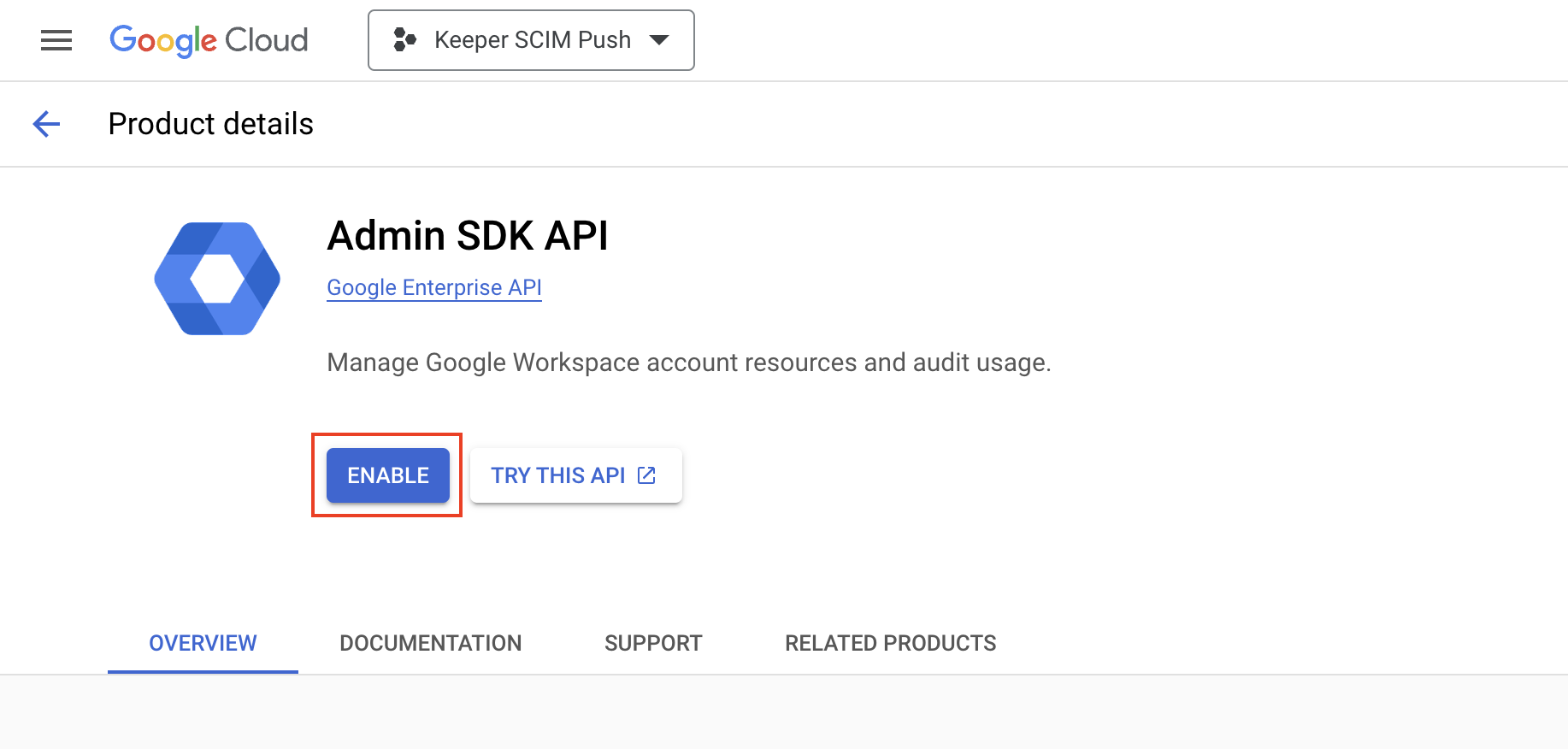
Enable Admin SDK API
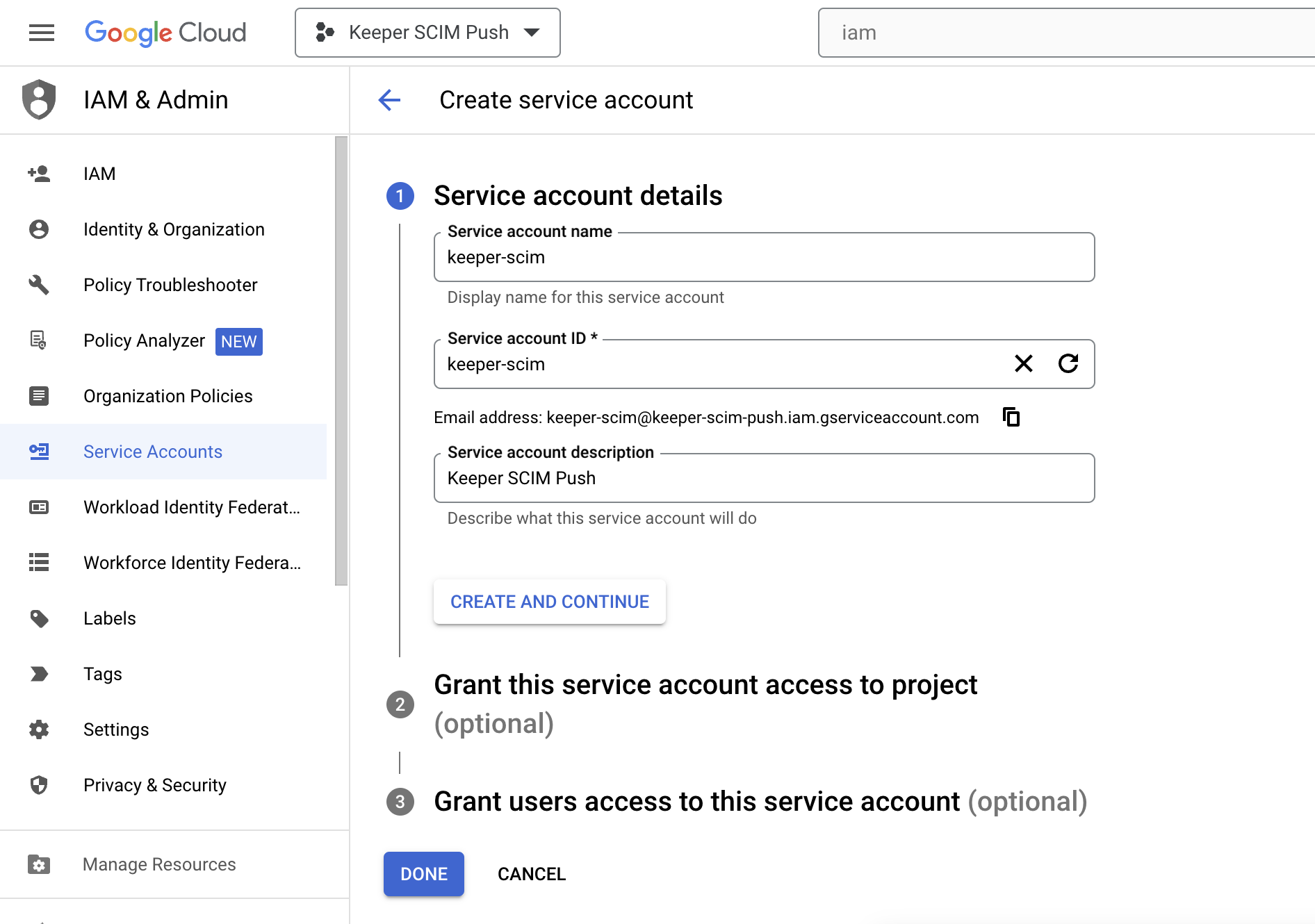
Create Service Account
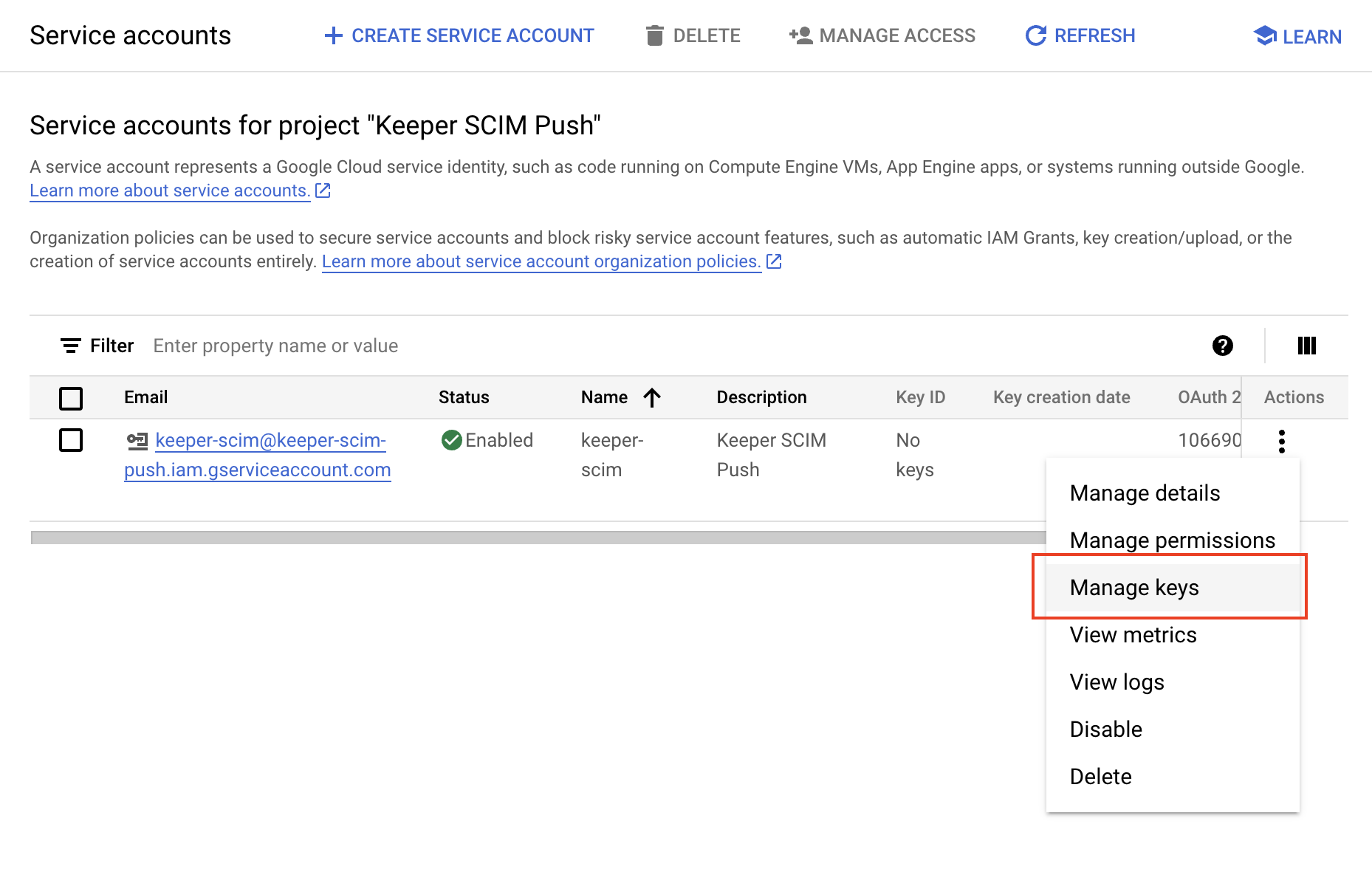
Create Keys and credentials.json
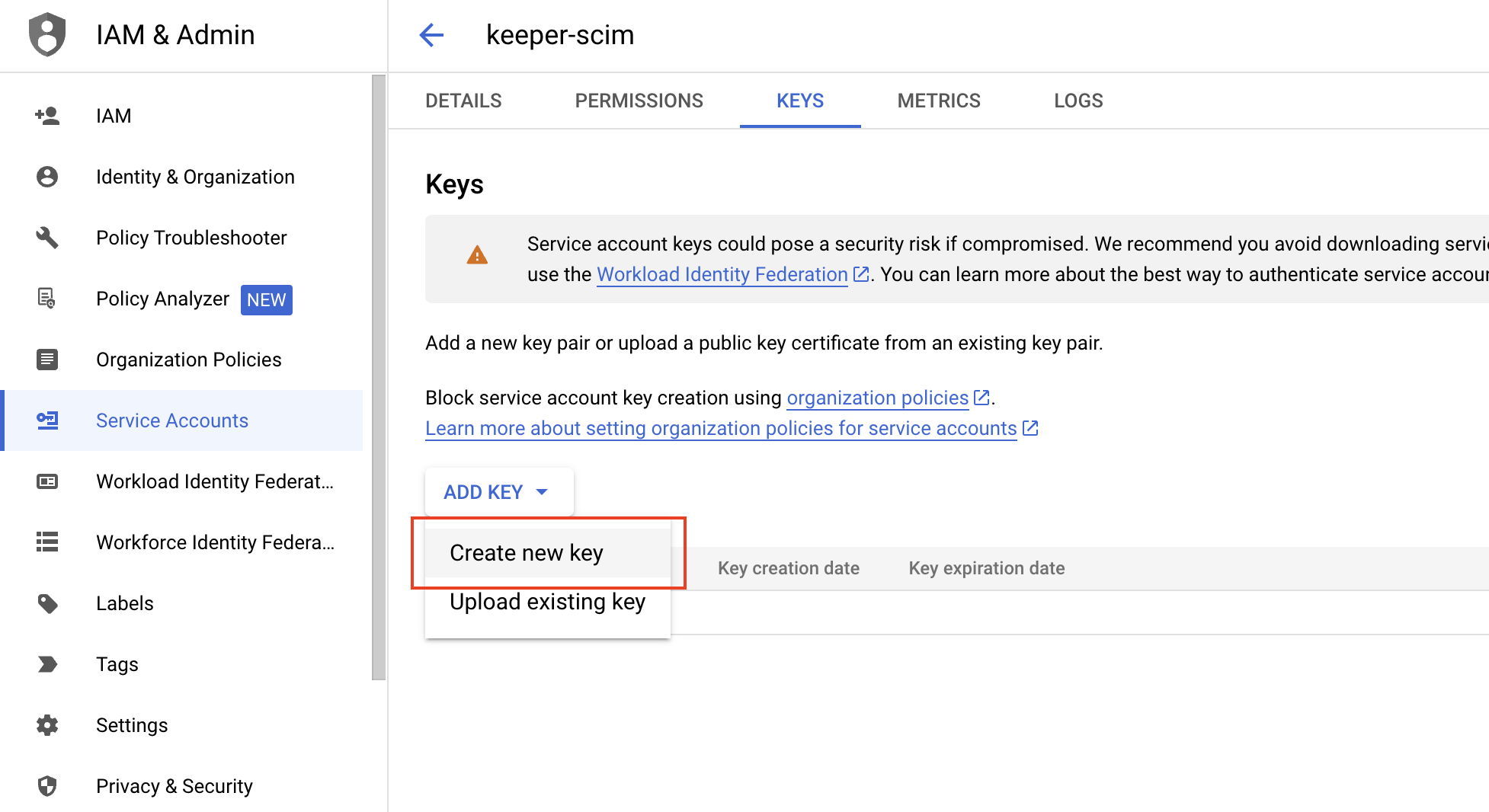
Create new key
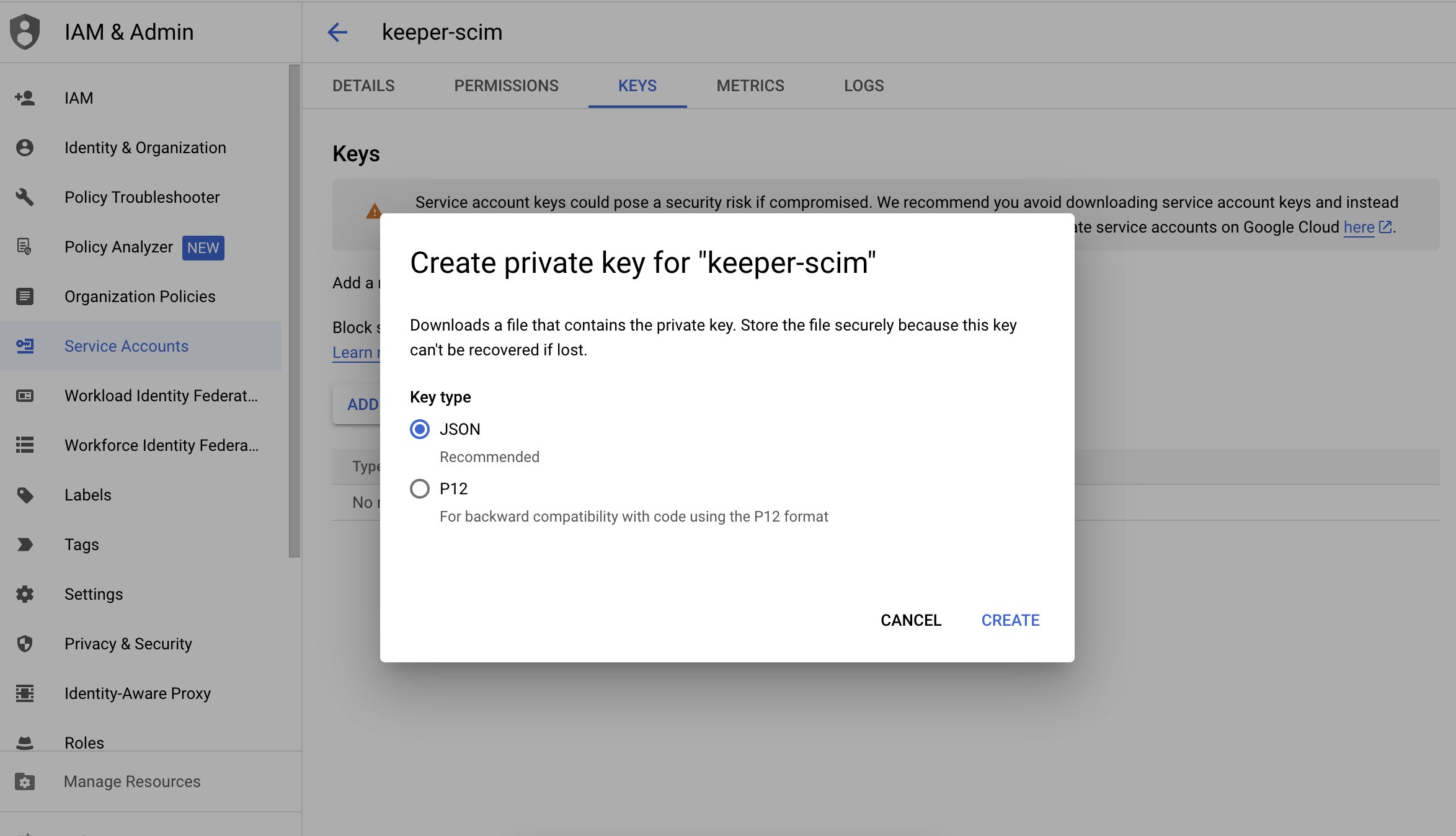
Select JSON format
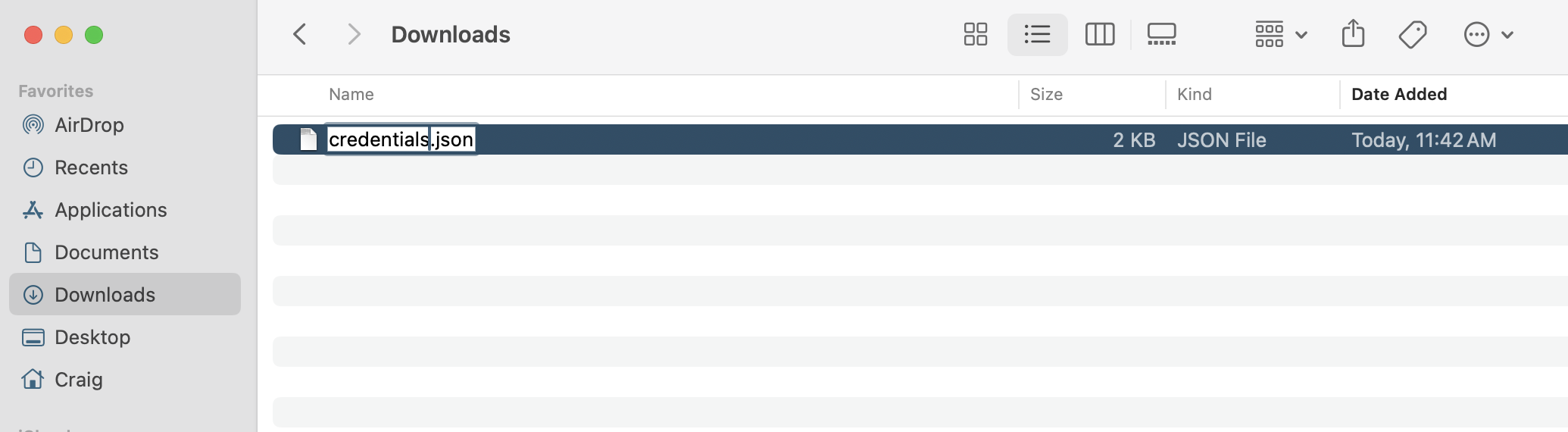
Save as credentials.json
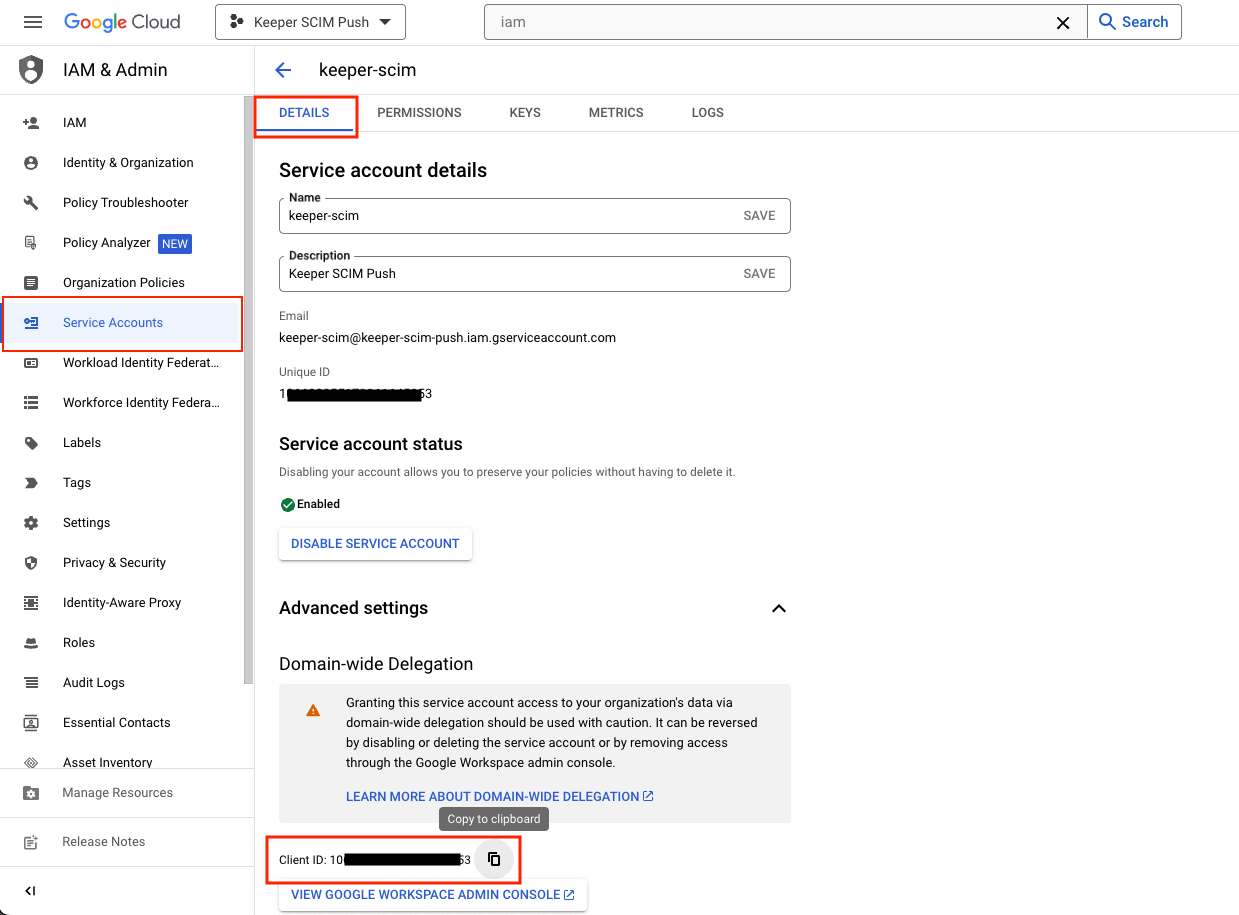
Copy the Client ID
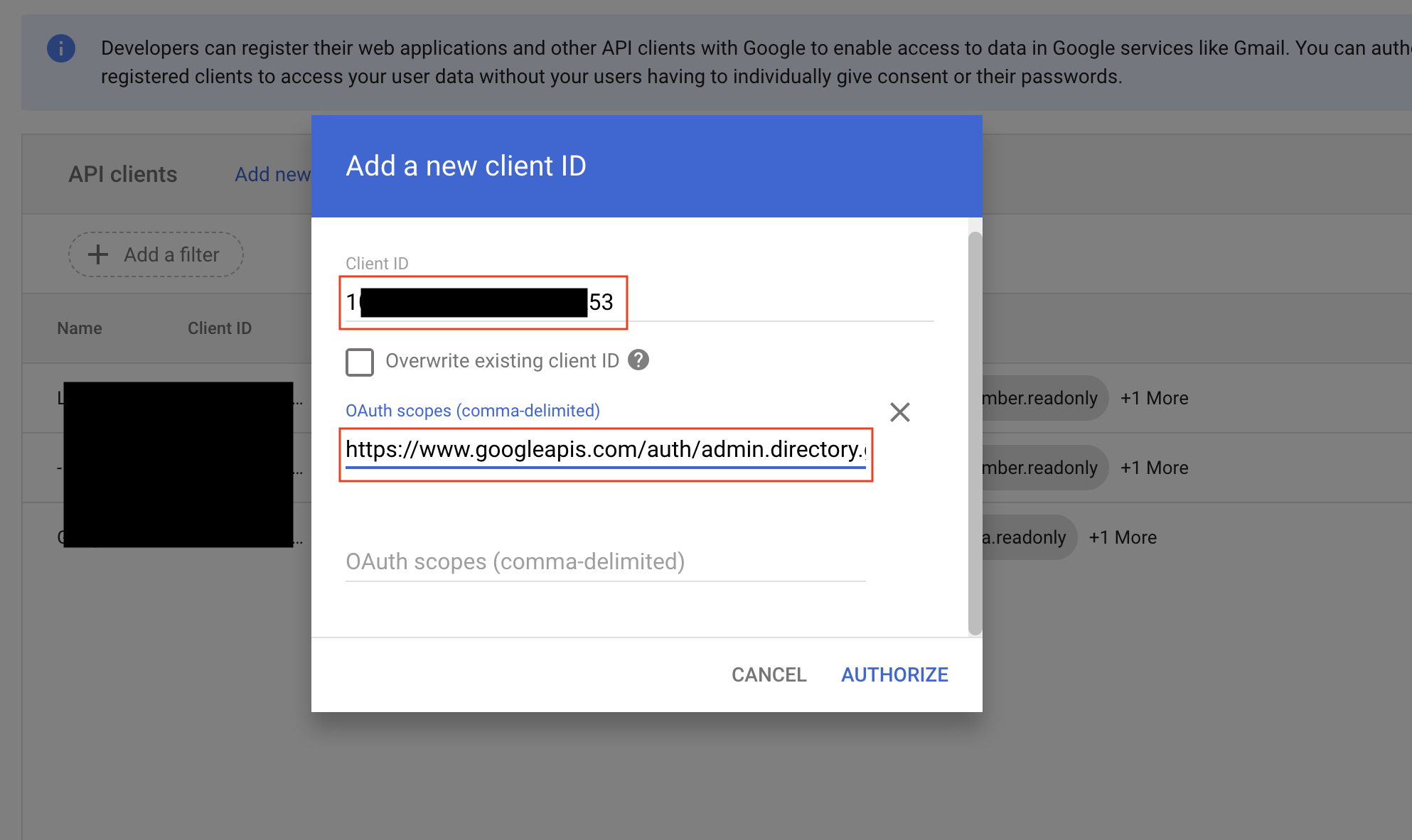
Add a new client ID
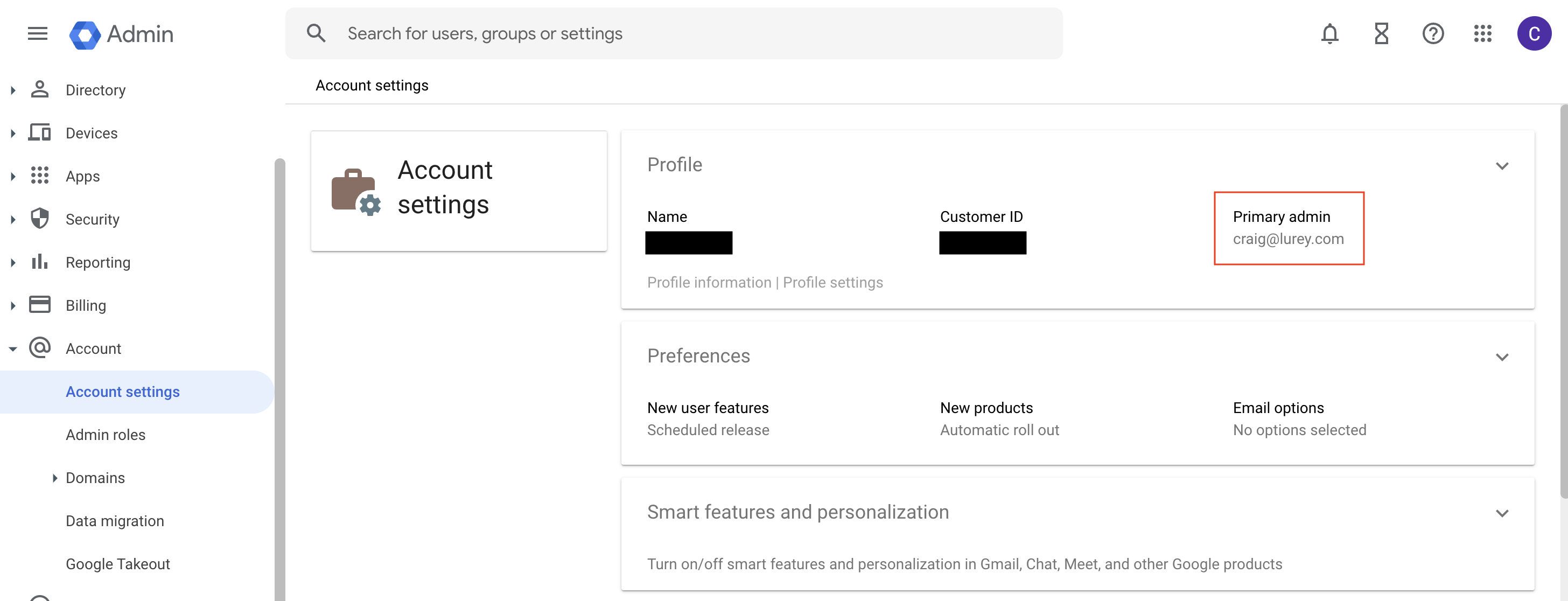
Get the primary admin email
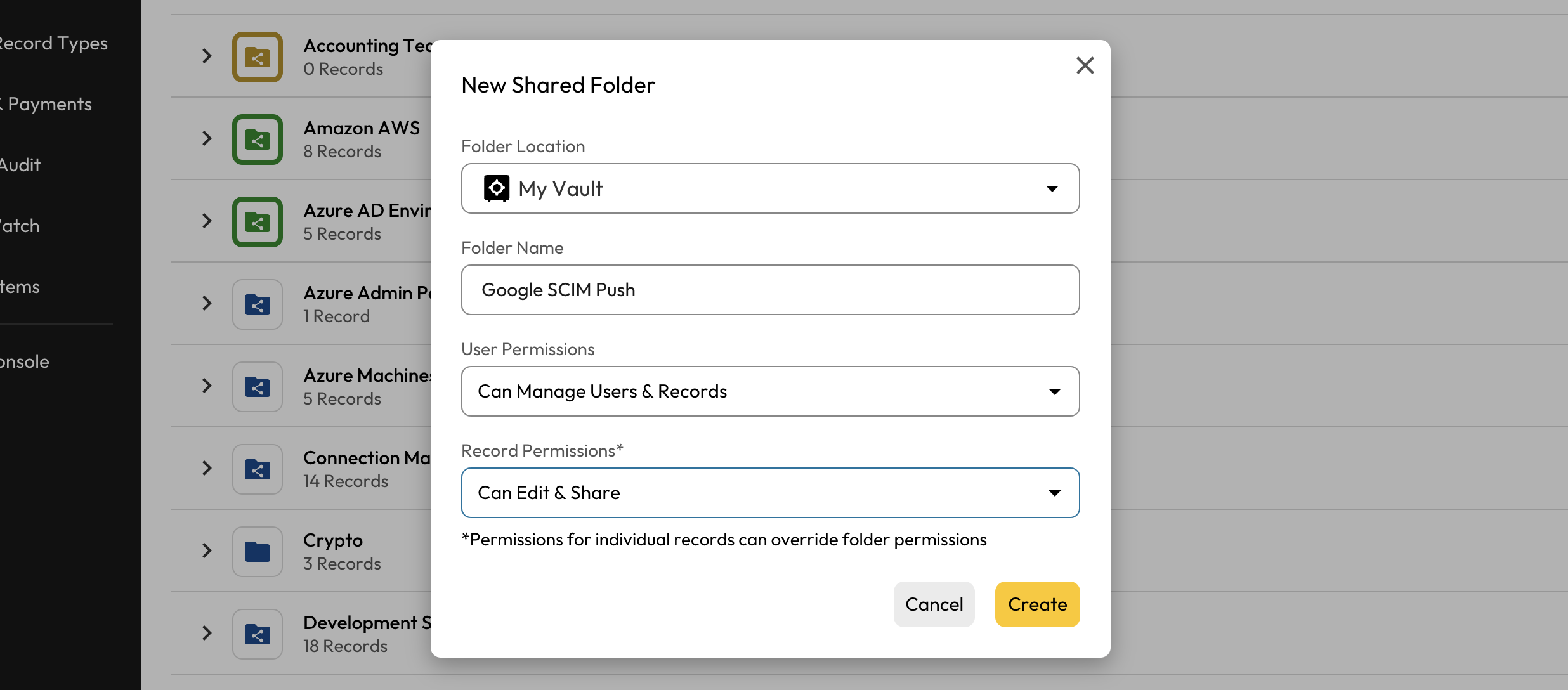
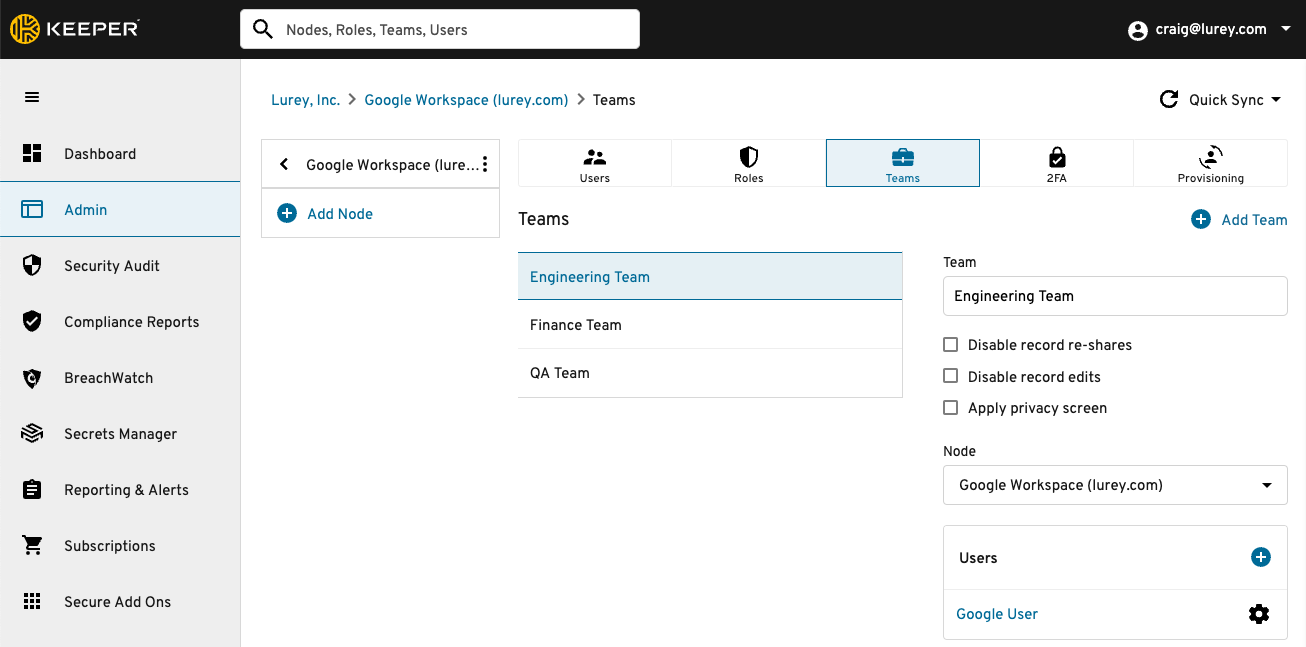
Create New Shared Folder
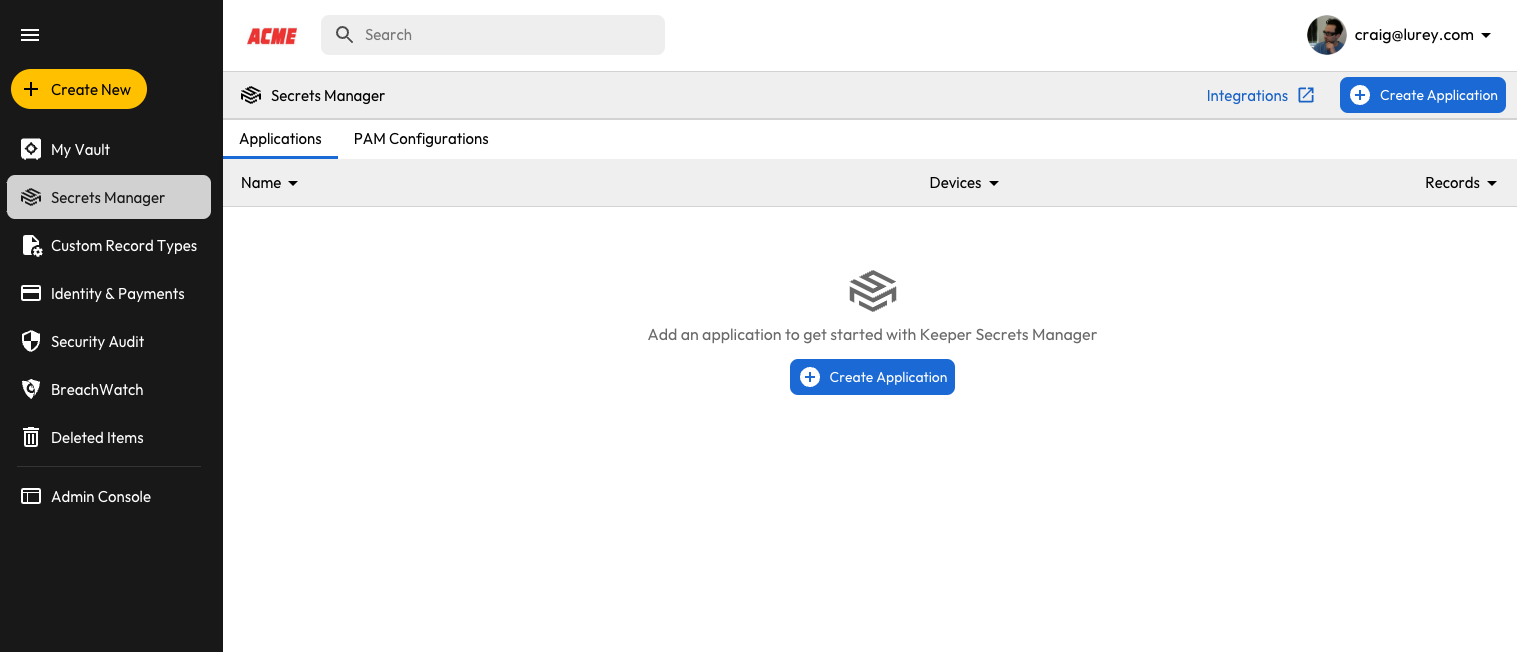
Create Application
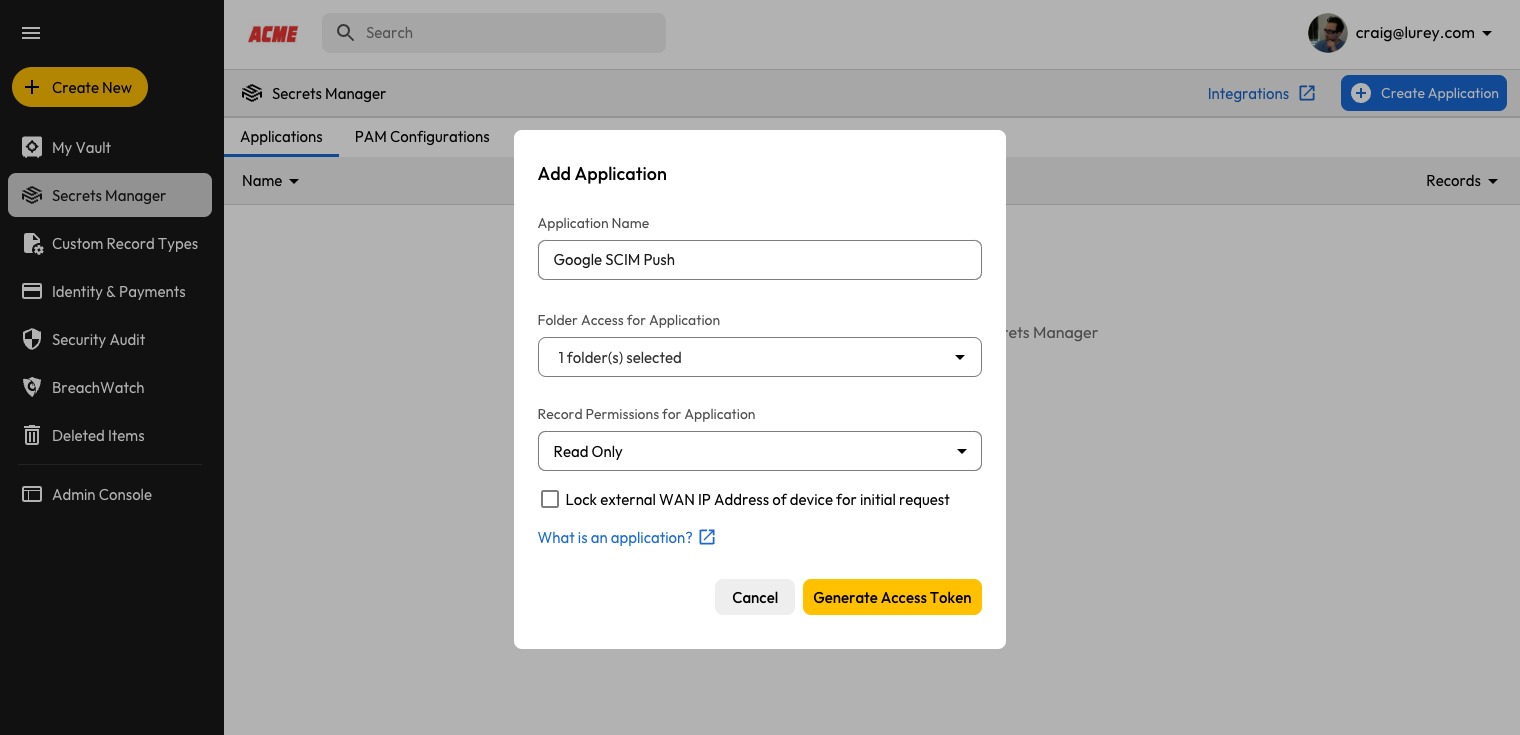
Generate Access Token
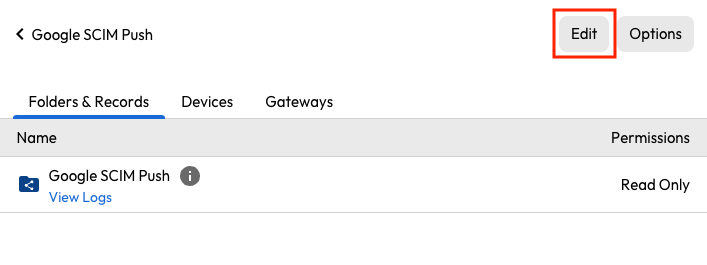
Edit Application
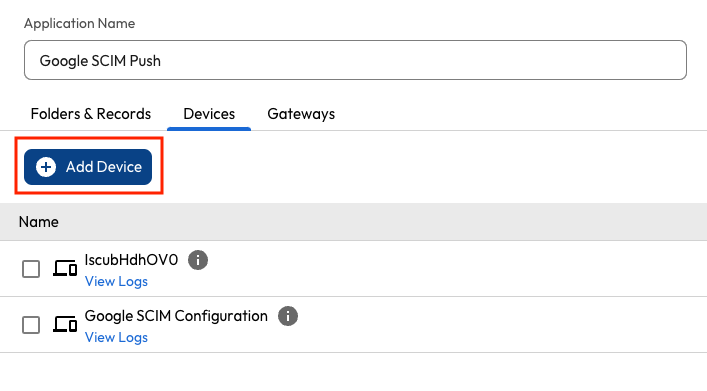
Add Device
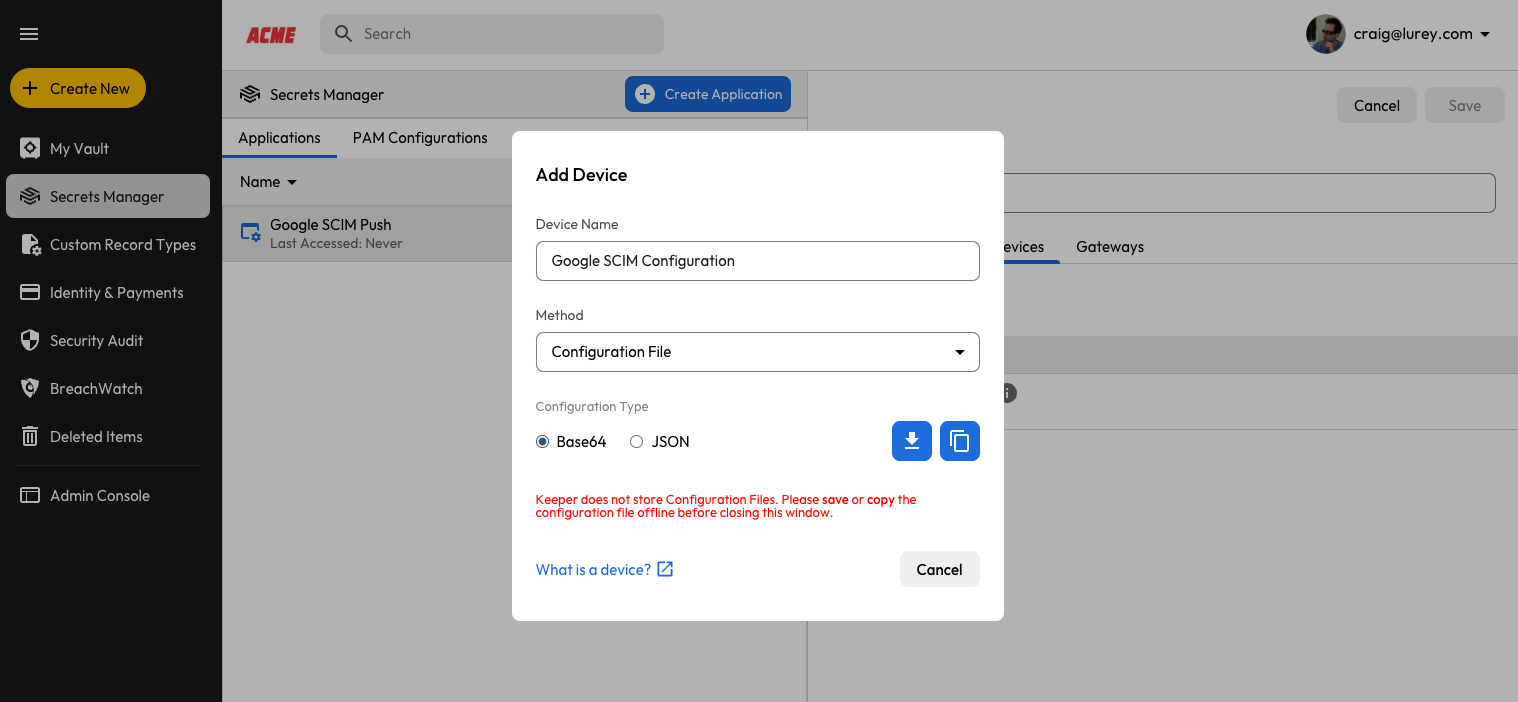
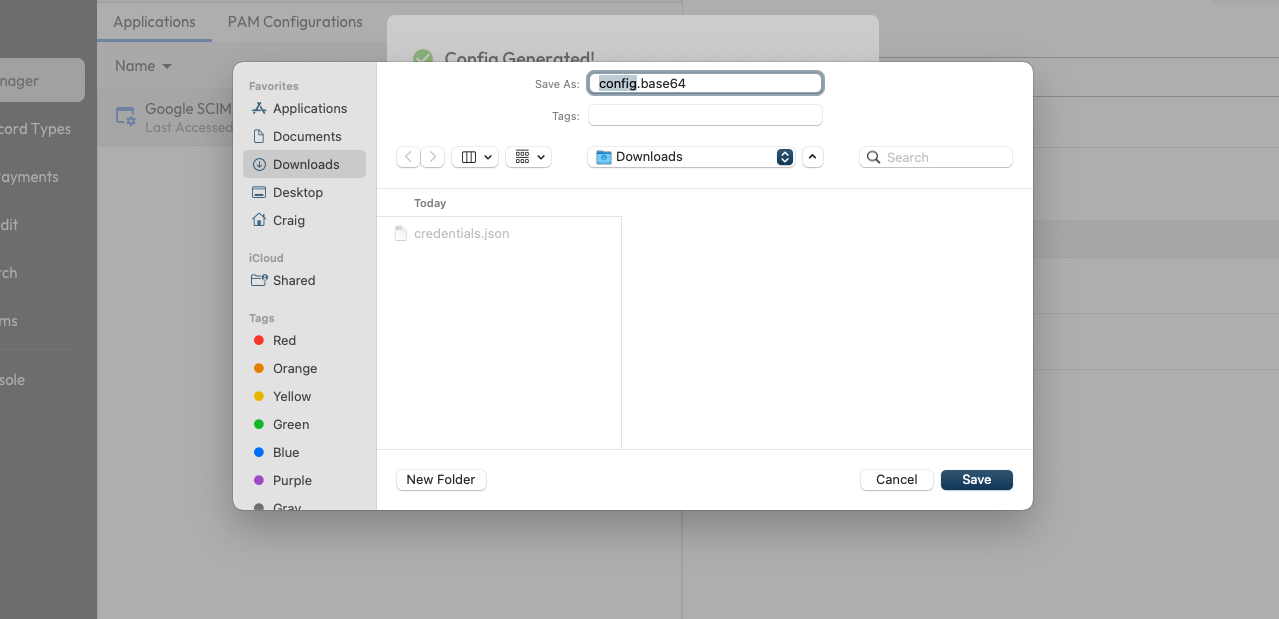
Save config.base64
| Field | Value |
|---|---|
| Login | Google Workspace admin email |
| Password | SCIM Token generated from Step 9 above |
| Website Address | SCIM URL generated from Step 9 above |
| credentials.json | File attachment from Step 3 with Google Service Account credentials |
| SCIM Group | Multi-line custom text field containing a list of all groups to be provisioned. The names can either be Group Email or Group Name. |
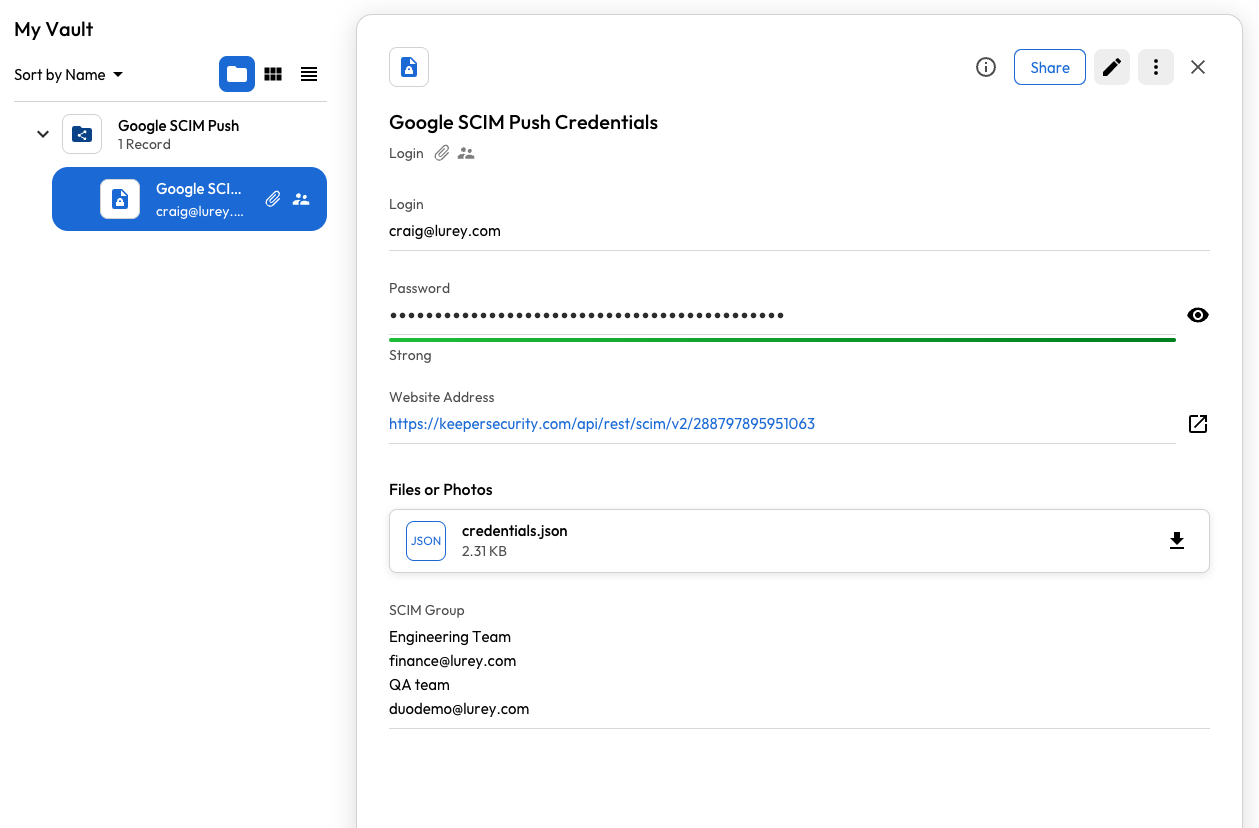
Keeper Vault Record
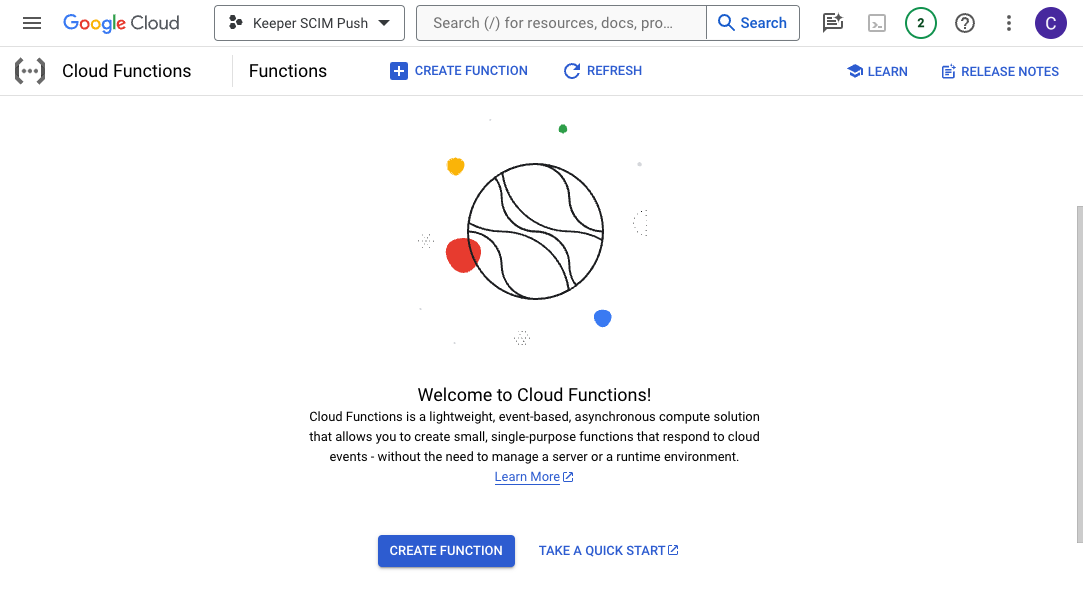
Create Function
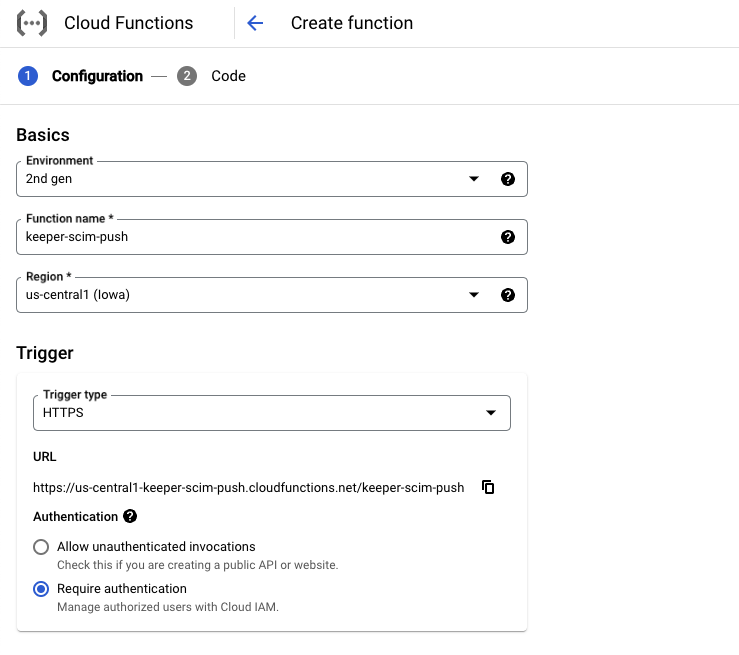
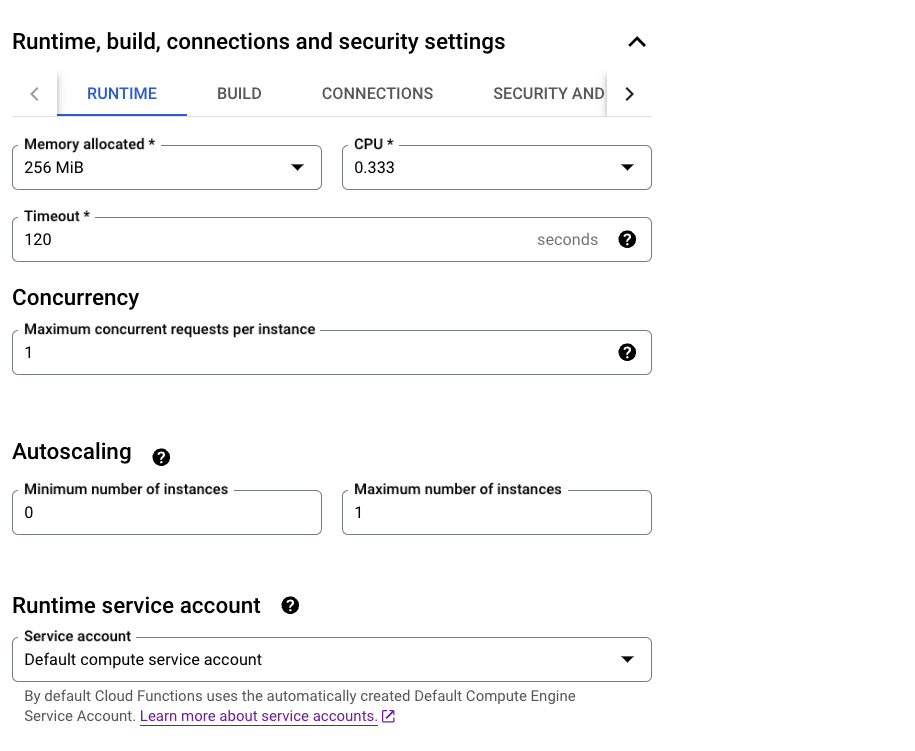
Runtime Settings
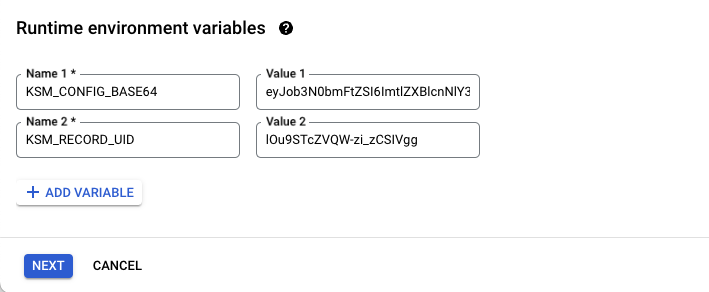
Runtime environment variables
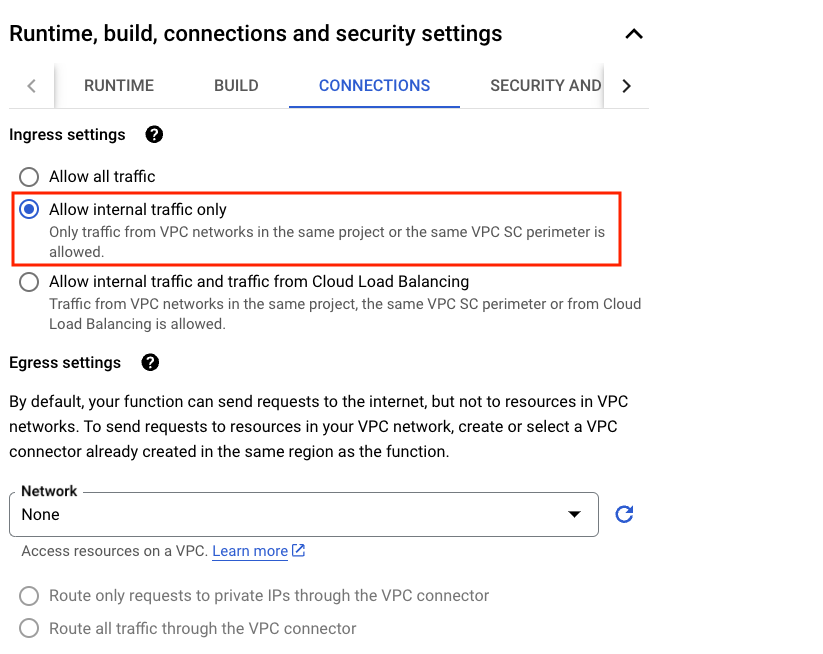
Allow internal traffic only

Click NEXT
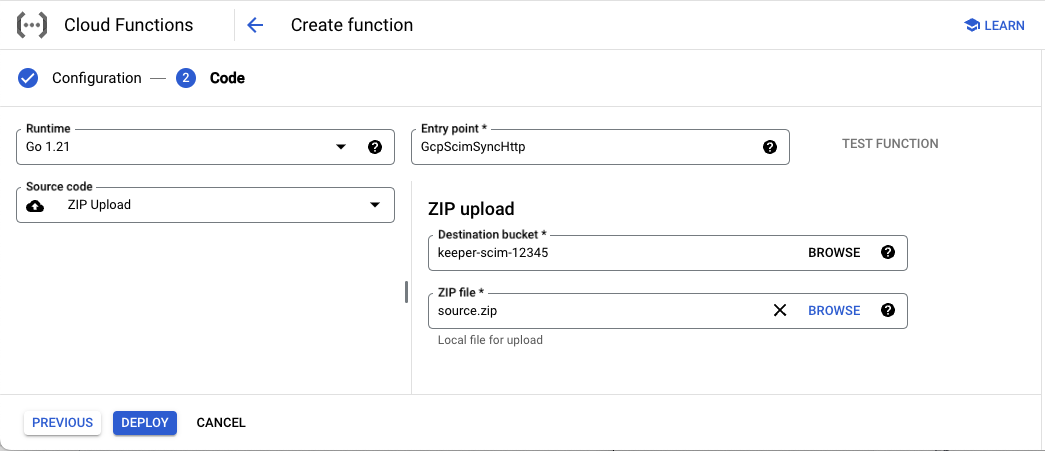
Cloud Function Code Source
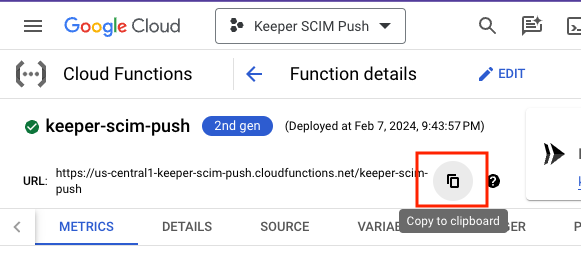
Copy Cloud Function URL
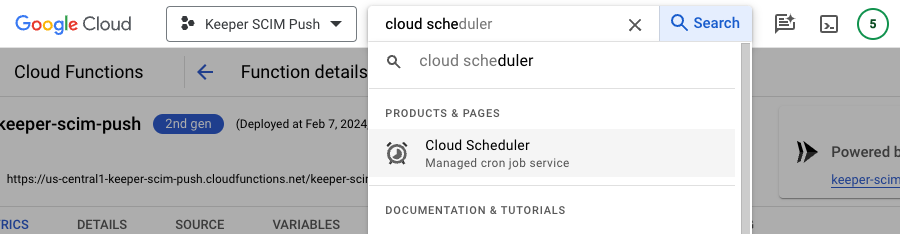
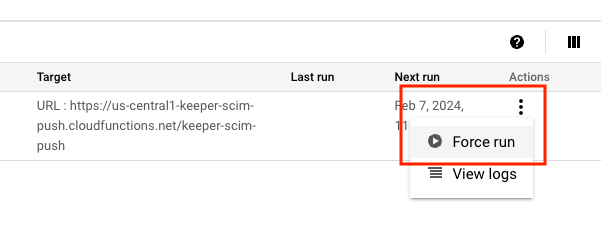
Cloud Scheduler
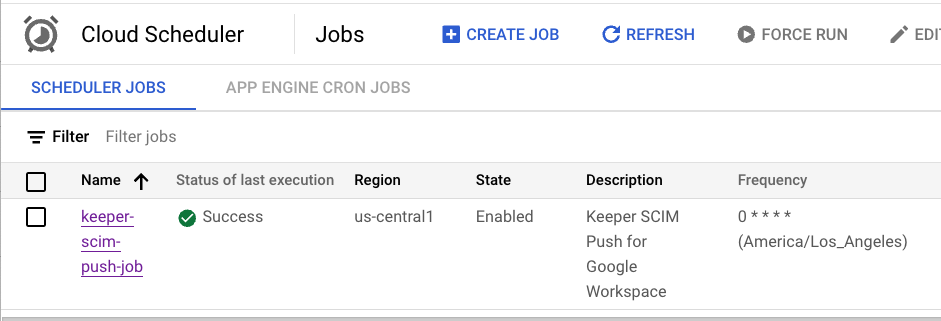
Scheduler Success
| "Destructive" Field Value | Description |
|---|---|
| -1 | Nothing is deleted on the Keeper side during sync |
| 0 (Default) | Only SCIM-controlled Groups and Membership can be deleted during sync. (Default Setting) |
| 1 | Any manually created or SCIM-controlled Groups and Memberships can be deleted during sync. |
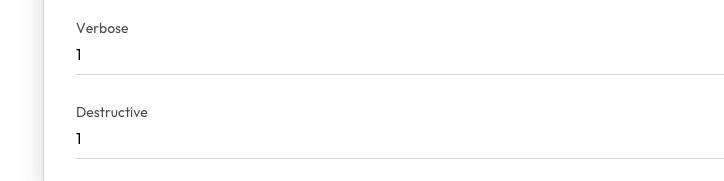
Example of Verbose and Destructive Settings in Keeper Record