| Command | Alias | Purpose |
|---|---|---|
credential-provision | cp | Automate PAM User credential provisioning with AD account creation, automated rotation, and credential delivery via email or direct vault sharing |
| Field | Type | Required | Description |
|---|---|---|---|
first_name | string | Yes | New User's first name |
last_name | string | Yes | Employee's last name |
personal_email | string | Yes | Personal email for credential delivery |
employee_id | string | No | Employee identifier |
department | string | No | Department (used for folder organization) |
| Field | Type | Required | Description |
|---|---|---|---|
username | string | Yes* | Username for target system |
username_template | string | Yes* | Template for deriving username (see Username Templates below) |
pam_config_uid | string | No** | UID of PAM Configuration record (deprecated — use -c flag instead) |
directory_uid | string | Yes | UID of pamDirectory record for AD user creation |
distinguished_name | string | No*** | AD Distinguished Name (supports {username} placeholder) |
ad_groups | list | No | List of AD group DNs to add the user to |
existing_password | string | No | Account's current real password. Stored in the vault; never pushed to a target. Use when onboarding an account that already exists in AD. Validator forbids combining this with a rotation that would fire at provisioning — see Security Constraints. |
| Field | Type | Required | Description | Default |
|---|---|---|---|---|
folder | string | No | Subfolder path relative to gateway application folder, or a folder UID | PAM Users/{department} |

| Field | Type | Required | Description |
|---|---|---|---|
schedule | string | Yes* | 6-field CRON expression |
on_demand | boolean | Yes* | Configures rotation for manual triggering only; no cron schedule is stored. |
password_complexity | string | Yes | Password complexity rules |
rotate_on_provision | boolean | No (default true) | When false, skips the immediate rotation at provisioning time. The configured schedule (or manual Rotate Now) handles all subsequent rotations. |
| Field | Type | Required | Description | Default |
|---|---|---|---|---|
share_to | string | Yes | Keeper vault email of recipient | - |
transfer_ownership | boolean | No | Transfer record ownership to recipient | false |
permissions.can_edit | boolean | No | Allow recipient to edit the record | false |
permissions.can_share | boolean | No | Allow recipient to share the record | false |
| Field | Type | Required | Description | Default |
|---|---|---|---|---|
config_name | string | Yes | Email configuration name from Admin Console | - |
send_to | string | Yes | Recipient email | "example@gmail.com" |
subject | string | No | Email subject line | "Your New Credentials" |
share_url_expiry | string | No | Share URL expiration time | "7d" |
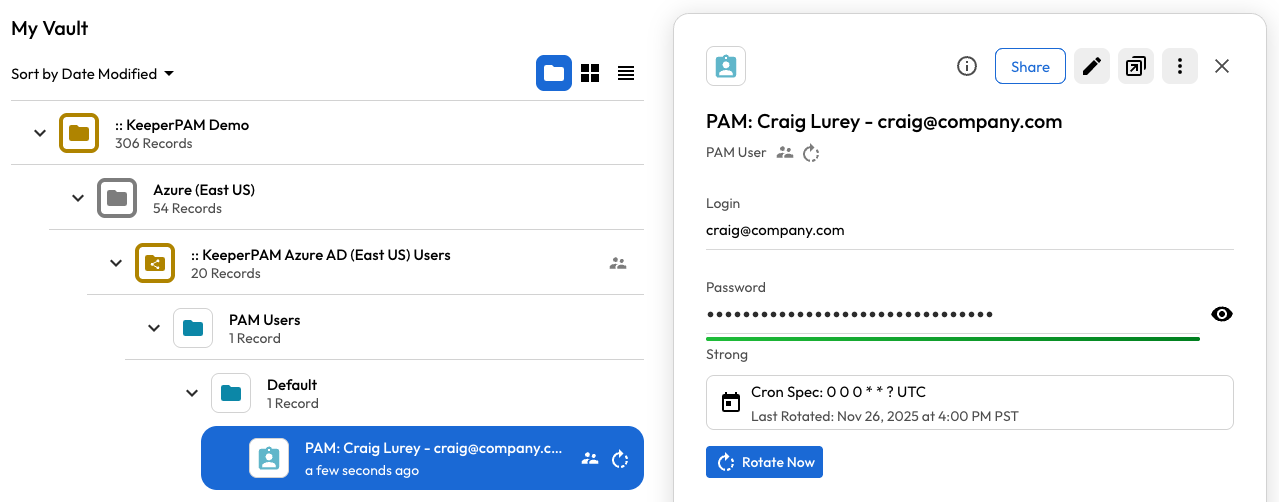
user:
first_name: Craig
last_name: Lurey
personal_email: craig@company.com
account:
username: craig@company.com
rotation:
schedule: "0 0 0 * * ?"
password_complexity: "32,5,5,5,5"
email:
config_name: "SMTP-Gmail"
send_to: "craig@gmail.com"
subject: "Your Microsoft Login"
share_url_expiry: "7d"