# AD FS Configuration
{% hint style="info" %}
For a 100% cloud-based integration with AD FS, see [Keeper SSO Connect Cloud](https://docs.keeper.io/sso-connect-cloud)
{% endhint %}
### Microsoft AD FS
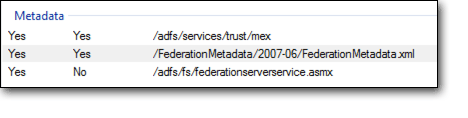
#### Obtain Federation Metadata XML
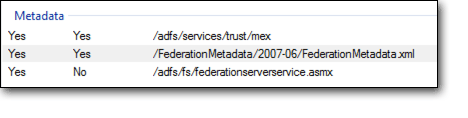
Inside the AD FS Management application, locate the Federation Metadata xml file. This can be found by clicking on AD FS > Service > Endpoints then locate the URL path in the "Metadata" section. The path is typically **/FederationMetadata/2007-06/FederationMetadata.xml** as seen below: