# AWS SSO Configuration
{% hint style="info" %}
For a 100% cloud-based integration with AWS, see [Keeper SSO Connect Cloud](https://docs.keeper.io/sso-connect-cloud)
{% endhint %}
### AWS SSO
Log into AWS and select on AWS Single Sign-On.
On the SSO Dashboard, select Configure SSO access to your cloud applications.

On the Applications menu, select **Add a new application**.

Next select **Keeper Security** and select **Add**.\*\*\\

{% hint style="info" %}
**Keeper is working with AWS to develop an Application Connector.**
{% endhint %}
Fill in the Display name and Description (optional) in the application details section.

In the AWS SSO metadata section, select the download button to export the AWS SSO SAML metadata file. This file gets imported in the SSO Connect IdP Metadata section on the configuration screen.

Copy this file to the Keeper SSO Connect server and upload it into the Keeper SSO Connect interface by dragging and dropping the file into the Configuration screen:\
\
Select **Save**.

The remaining step on the Keeper SSO Connect Server is to download the Keeper sso\_connect.xml metadata file and upload it to the AWS application.\
\
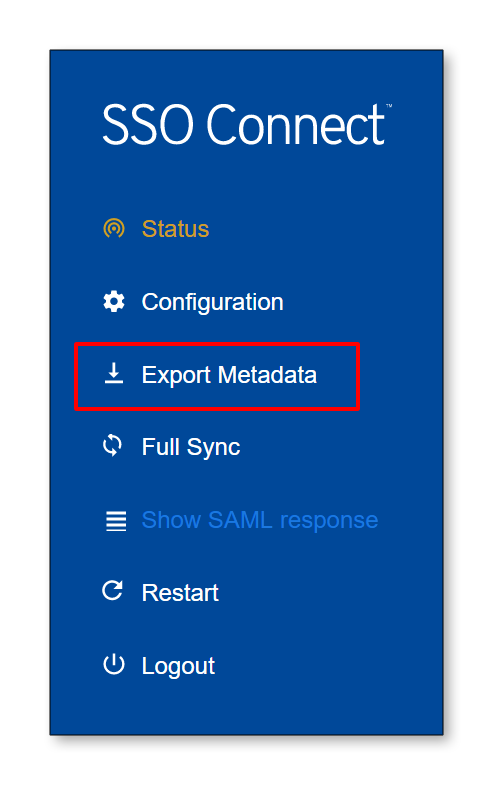
Select **Export Metadata** on the Keeper SSO Connect.
Import the sso\_connect.xml file to the Application metadata section on the application configuration screen.

After saving changes the **Configuration for Keeper Password Manager has been saved** success message will be displayed.

{% hint style="info" %}
**Note: The Keeper SSL certificate cannot be larger than 2048K or the below error will be received.**
{% endhint %}
* Either, generate a smaller SSL certificate, re-export and import the metadata file or manually set the ACS URL and Audience URL in the AWS SSO application configuration.
Next, Ensure the Keeper application attributes that are to be mapped to AWS SSO are correct (These should be set by default. Select the Attribute mappings tab.\
\
The AWS string value to ${user:subject} and format is blank or unspecified.\
\
The Keeper Attributes are set as follows:
| Keeper Attribute | AWS SSO String Value \*\* | Format |
| ---------------- | ------------------------- | ----------- |
| Email | ${user:email} | unspecified |
| First | ${user:givenName} | unspecified |
| Last | ${user:familyName} | unspecified |


{% hint style="info" %}
**Note: If your AWS email is mapped to the AD UPN (which may not be the actual email address of your users) it can be re-mapped to the email address associated in the users AD profile.**
{% endhint %}
To make this change navigate to the **Connect Directory** on the AWS SSO page.
Select on the **Edit attribute mappings** button.
Change the AWS SSO **email** attribute from ${dir:windowsUpn} to ${dir:email} .

Select on the the **Assigned users** tab and then the **Assign users** button to select users or groups to assign the application.

On the Assign Users window:
* Select either Groups or Users
* Type the name of a group or user
* Select on the **Search connect directory** to initiate the search.

The results of the directory search will display under the search window.

Select the users/groups that are desired to have access to the application and then select the **Assign users** button.

**Note: Keeper SSO Connect expects that the SAML response is signed. Ensure that your identity provider is configured to sign SAML responses.**
Your Keeper SSO Connect setup is now complete!
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://docs.keeper.io/sso-connect-on-prem/identity-provider-setup/aws-sso-configuration.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.