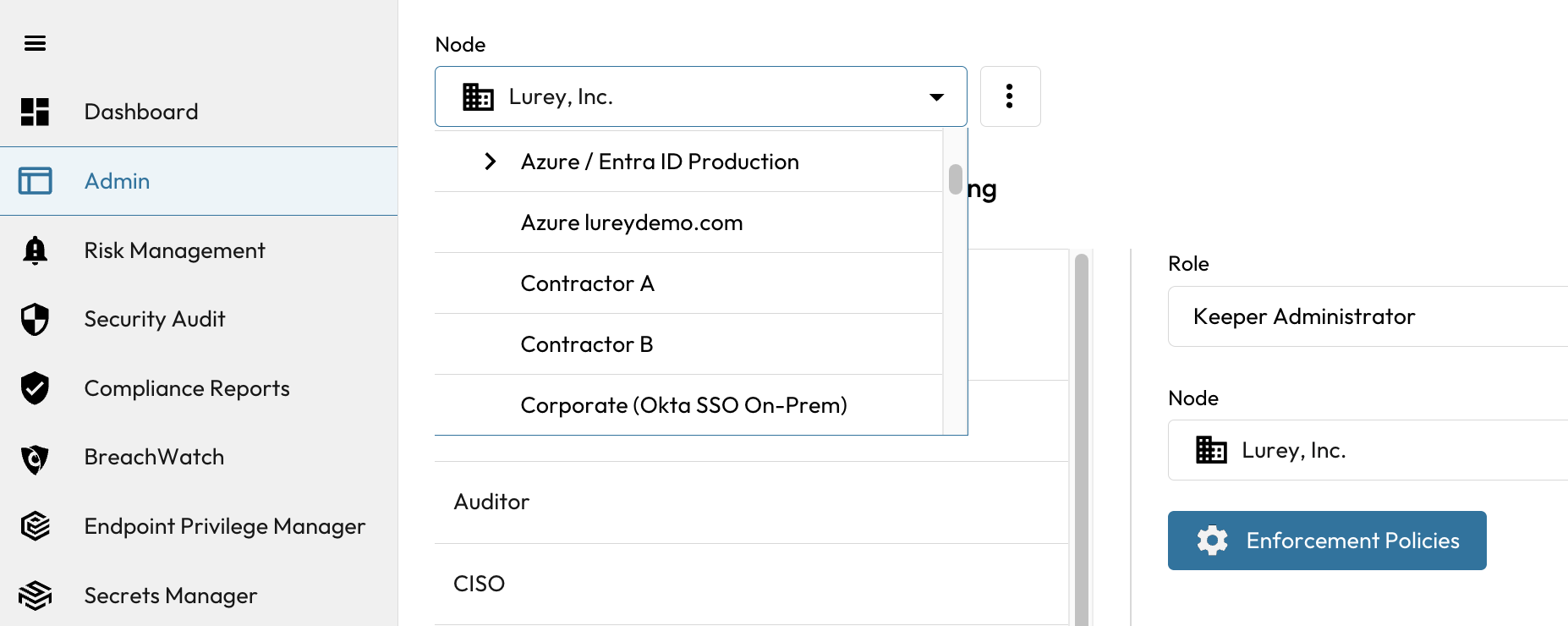
Node Structure
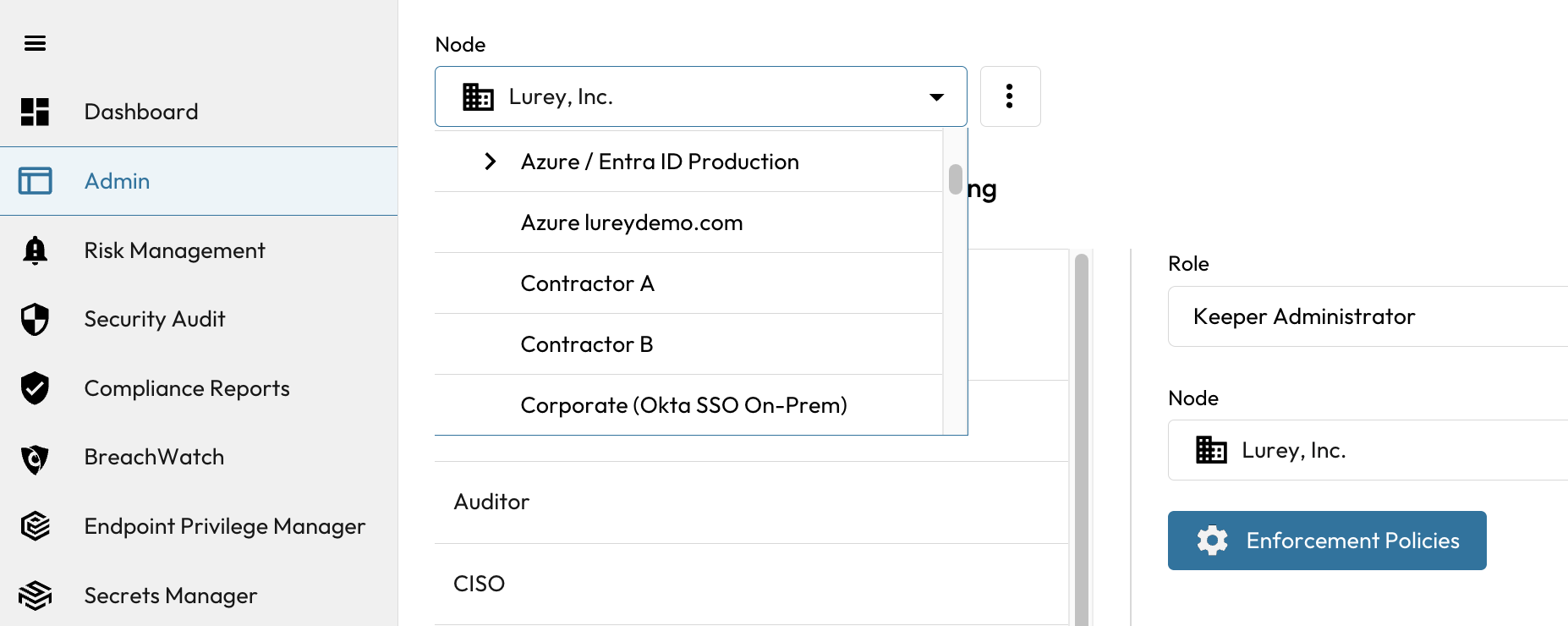
Node Structure
 button and click **Add Node**. The Add Node window will appear. Enter the name of the Node and select the node where you want the new node to be added in the tree structure.
button and click **Add Node**. The Add Node window will appear. Enter the name of the Node and select the node where you want the new node to be added in the tree structure.
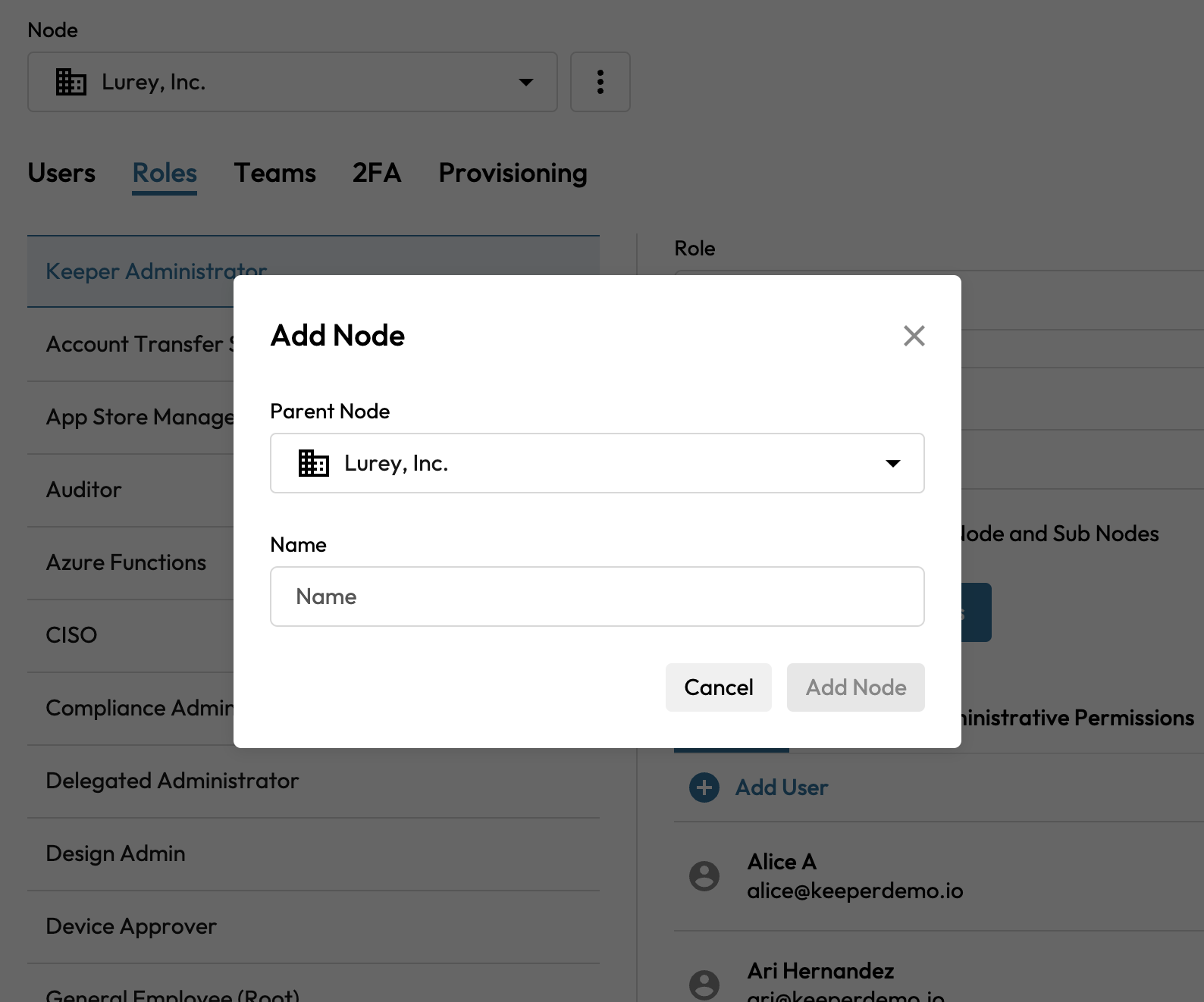
Adding a Node

Navigating Nodes

Sharing Autosuggest
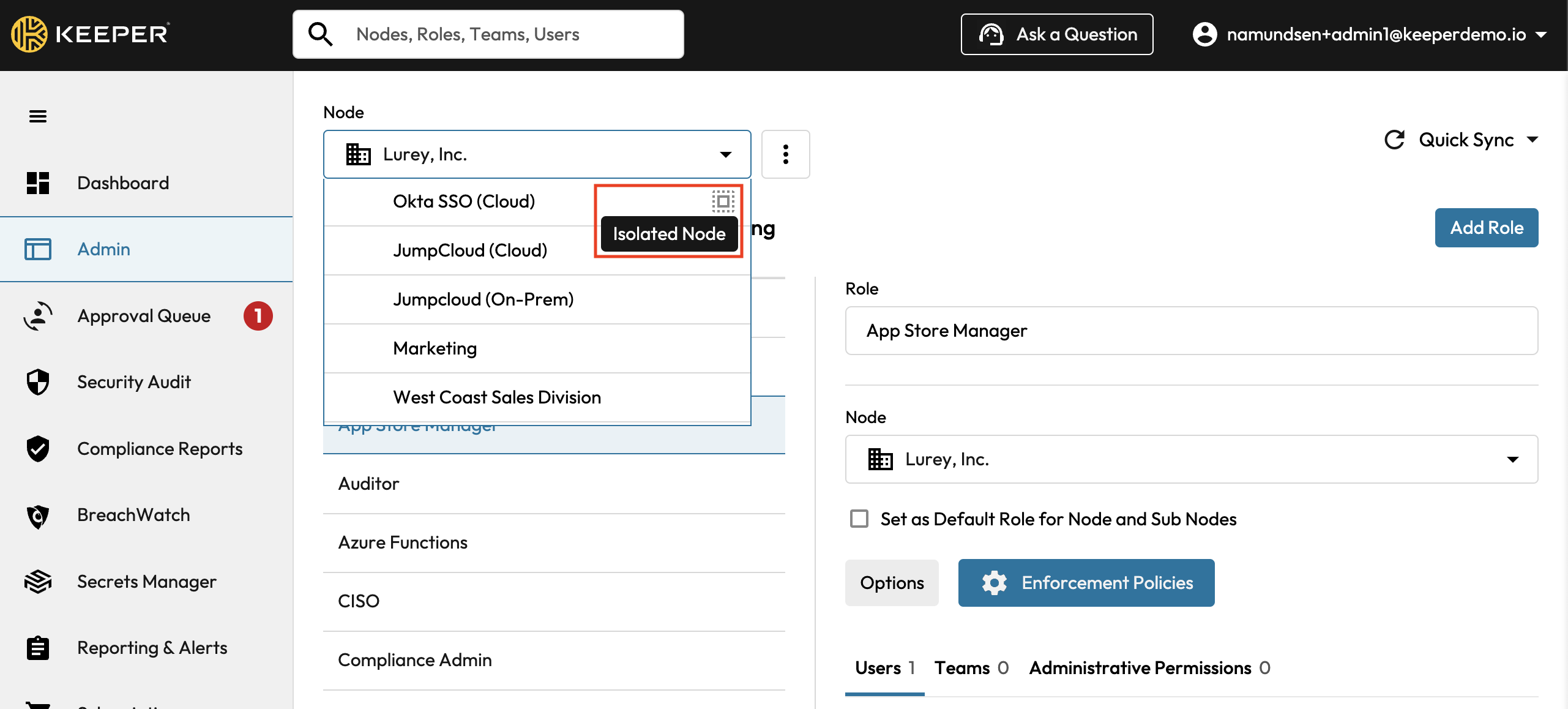
Isolated Node Indicator
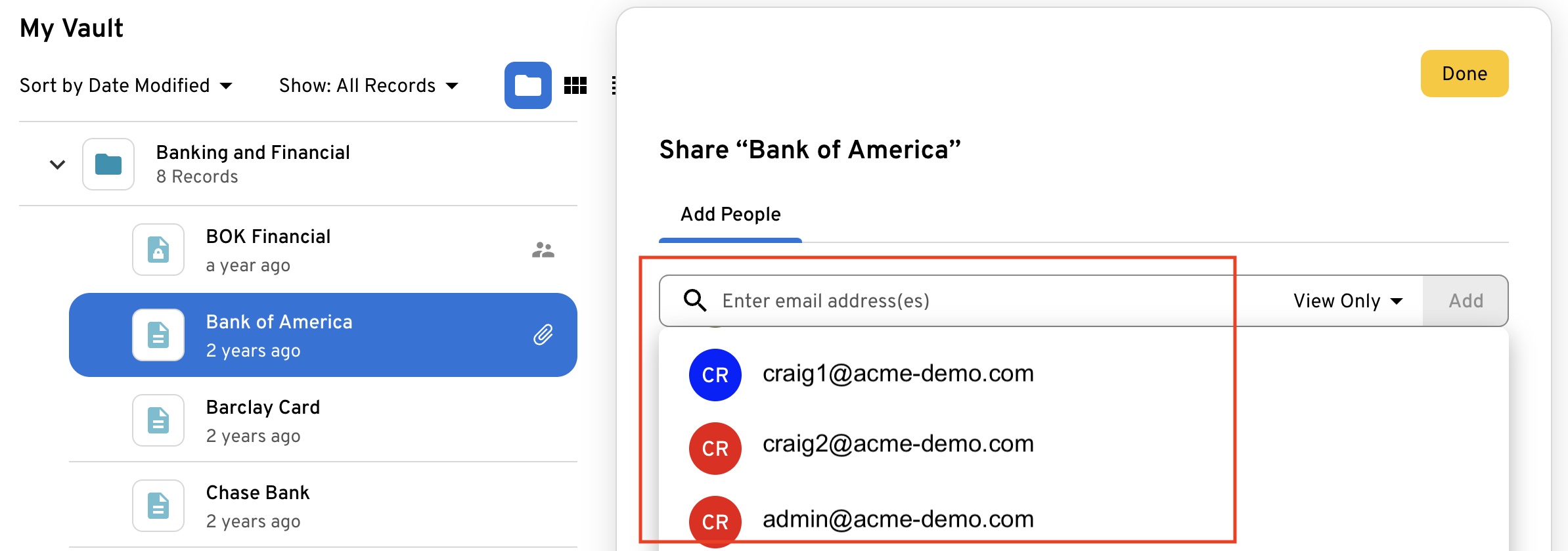
Node Isolation affected in Vault Sharing
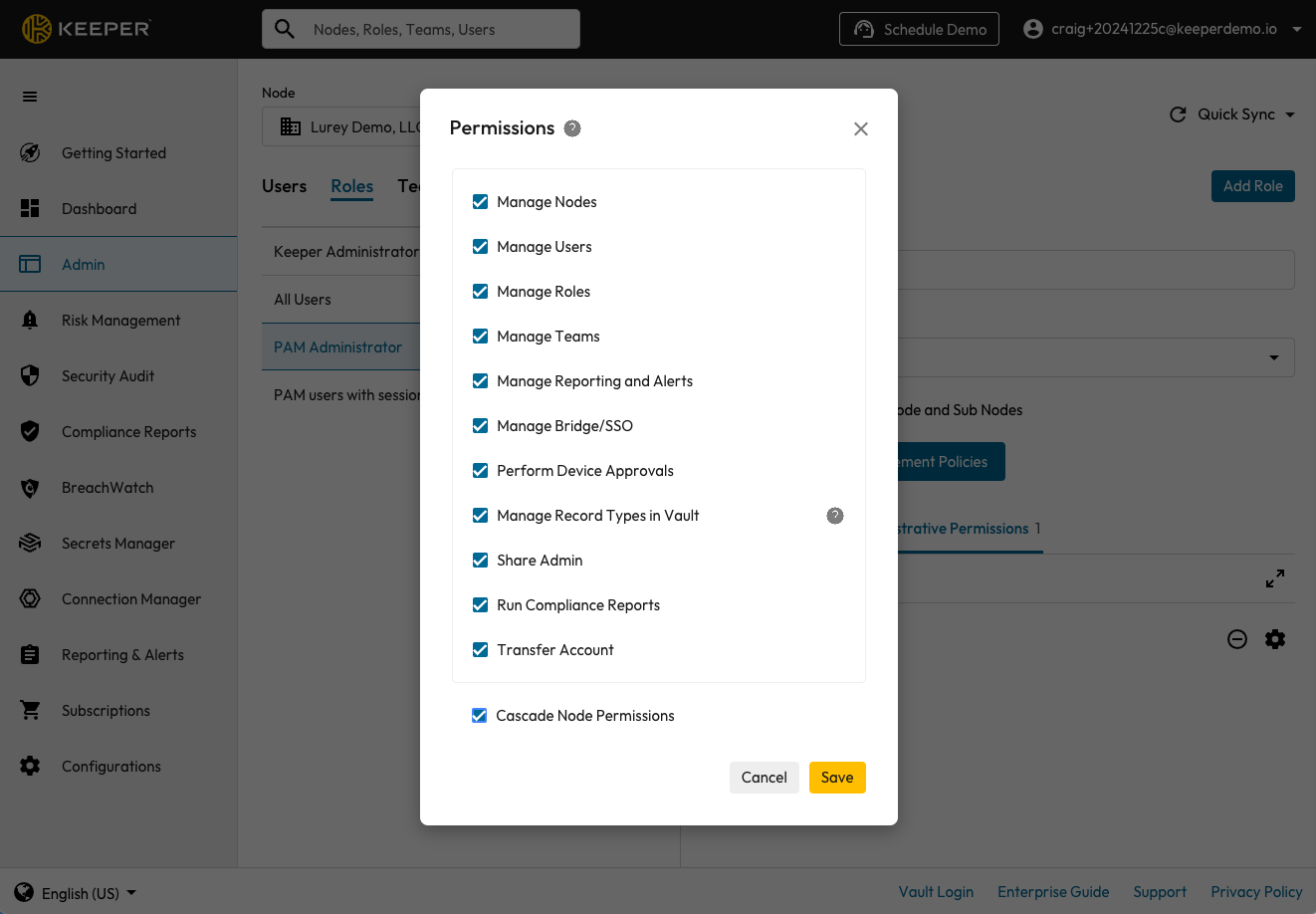
Cascade Node Permissions
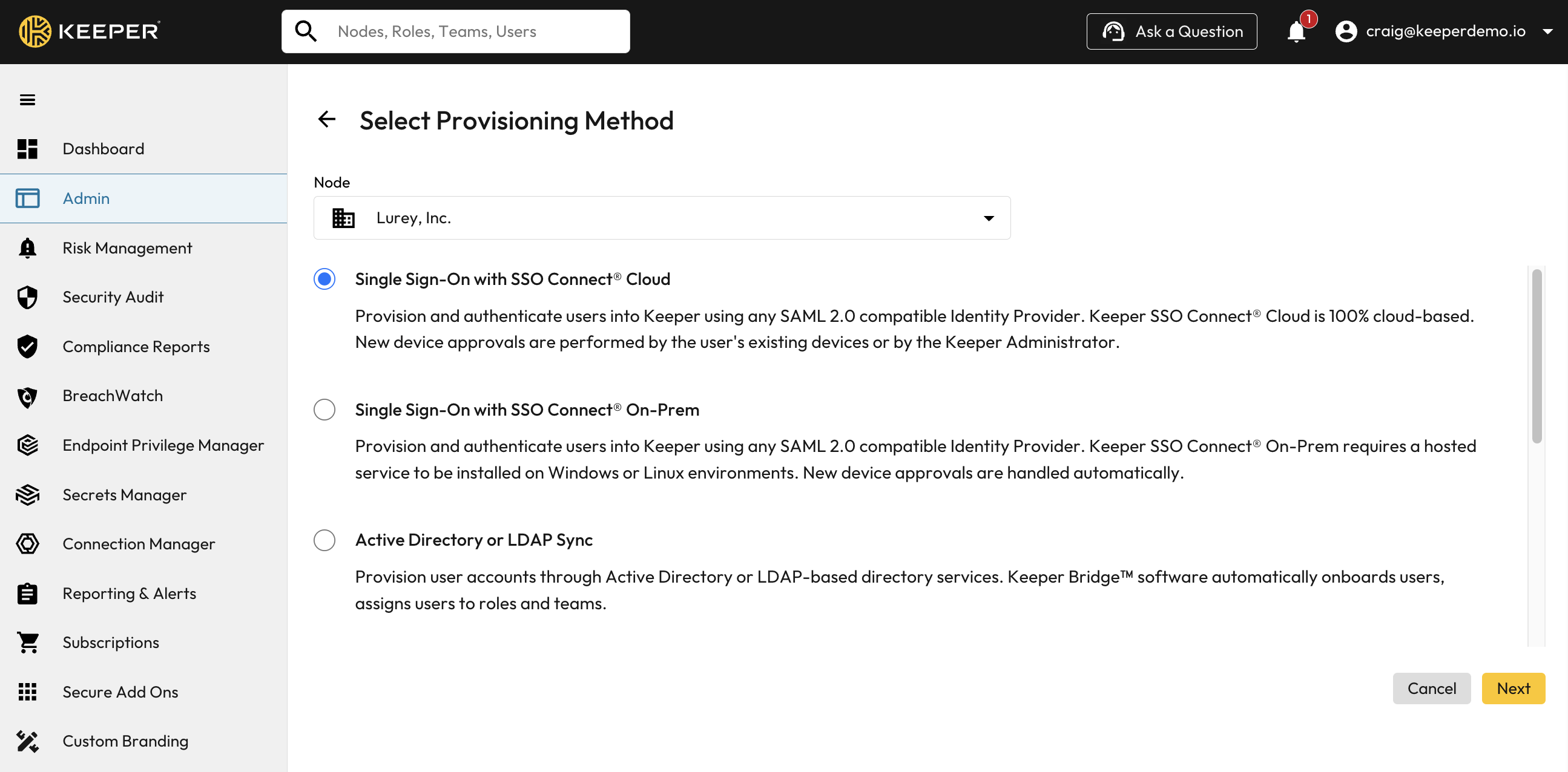
Provisioning Methods