

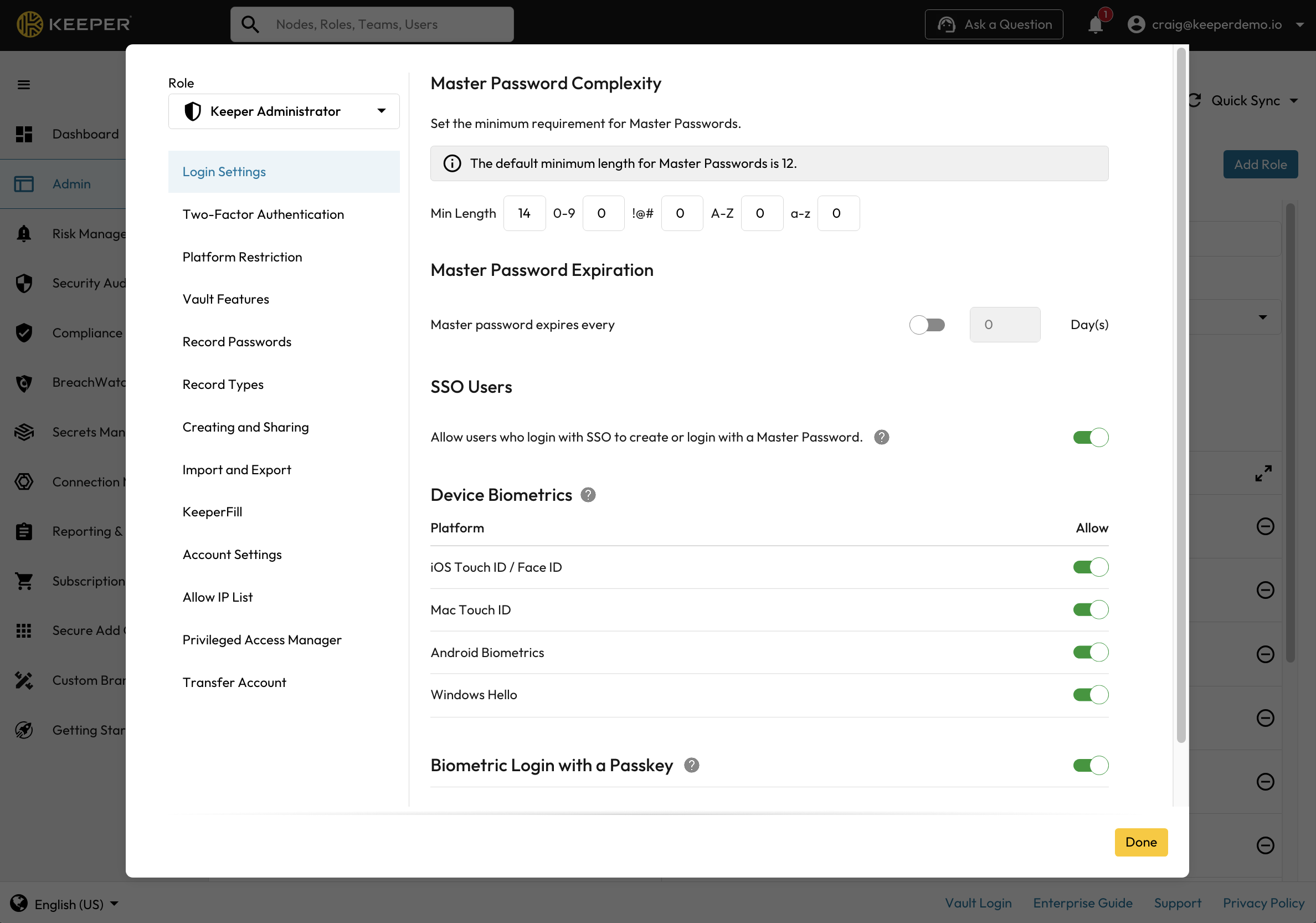
Login Settings
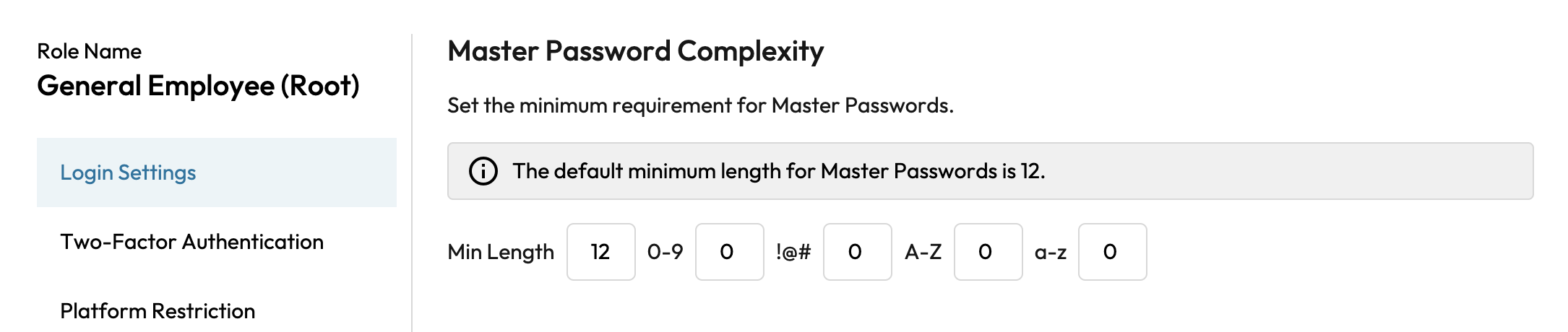
Login Settings > Master Password Complexity
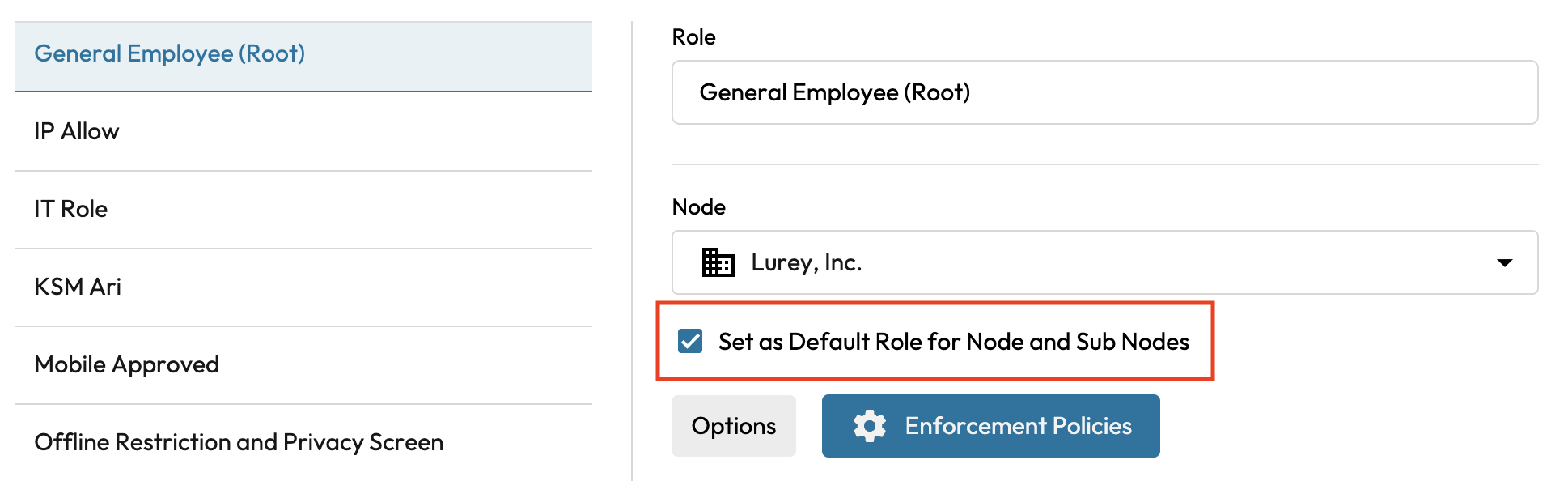
Default Role is used to calculate Master Password Complexity Requirements (new accounts only)

Login Settings > Master Password Expiration
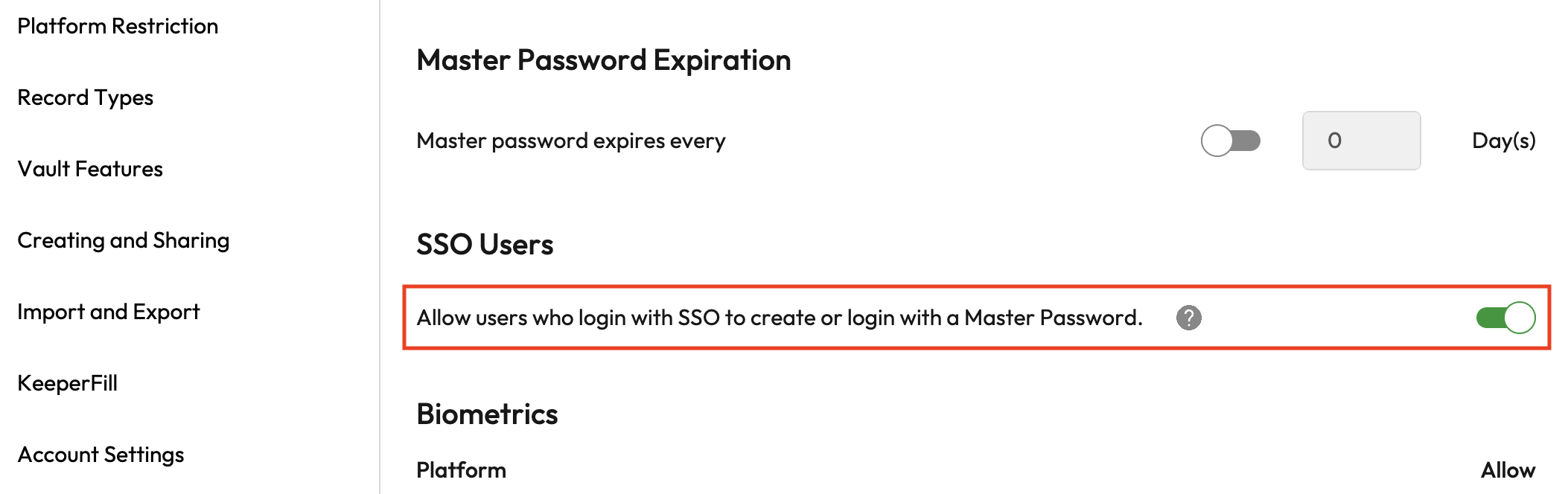
Login Settings > SSO Users Alternate Master Password Policy

Device Biometrics
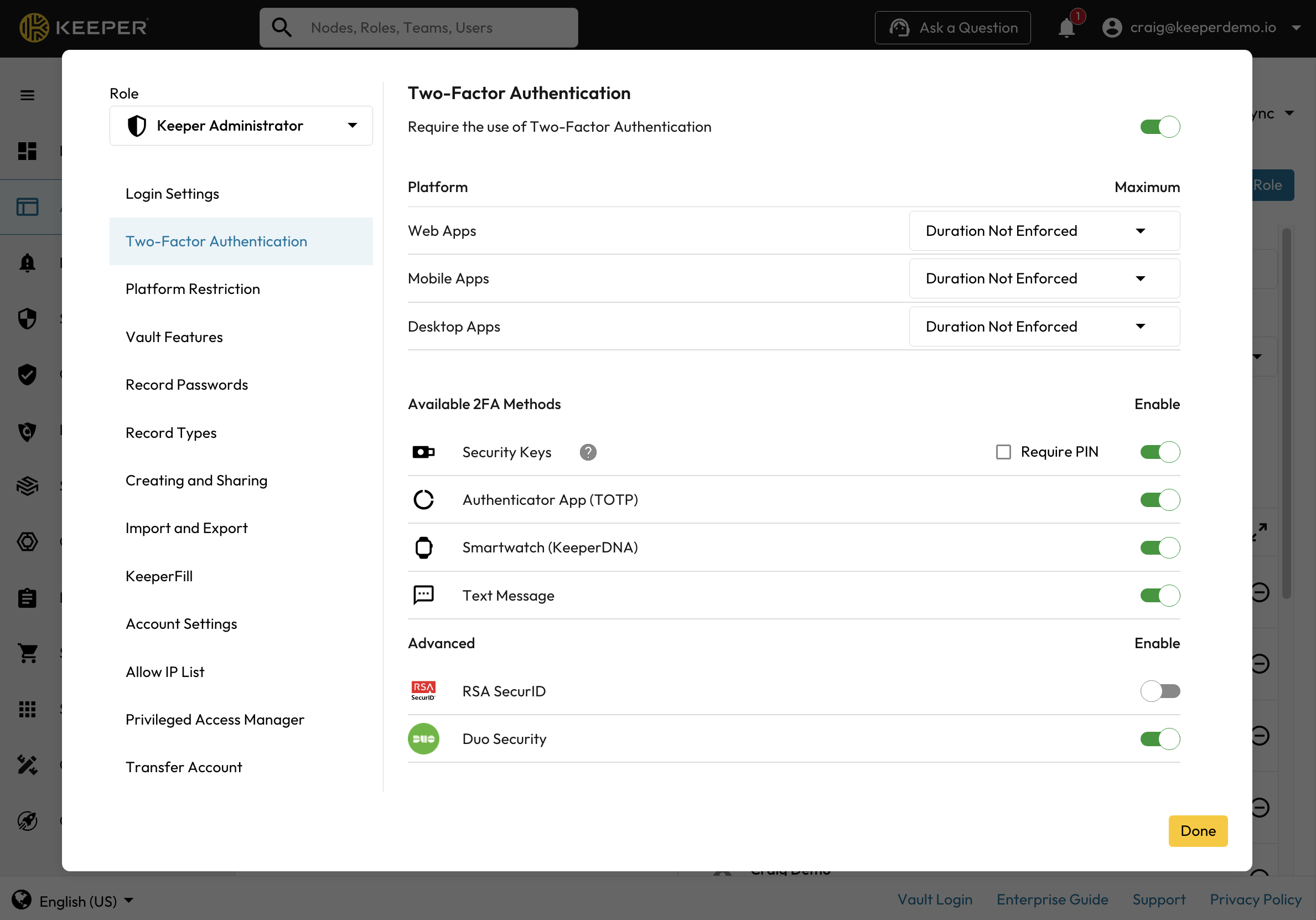
Two-Factor Authentication Enforcements
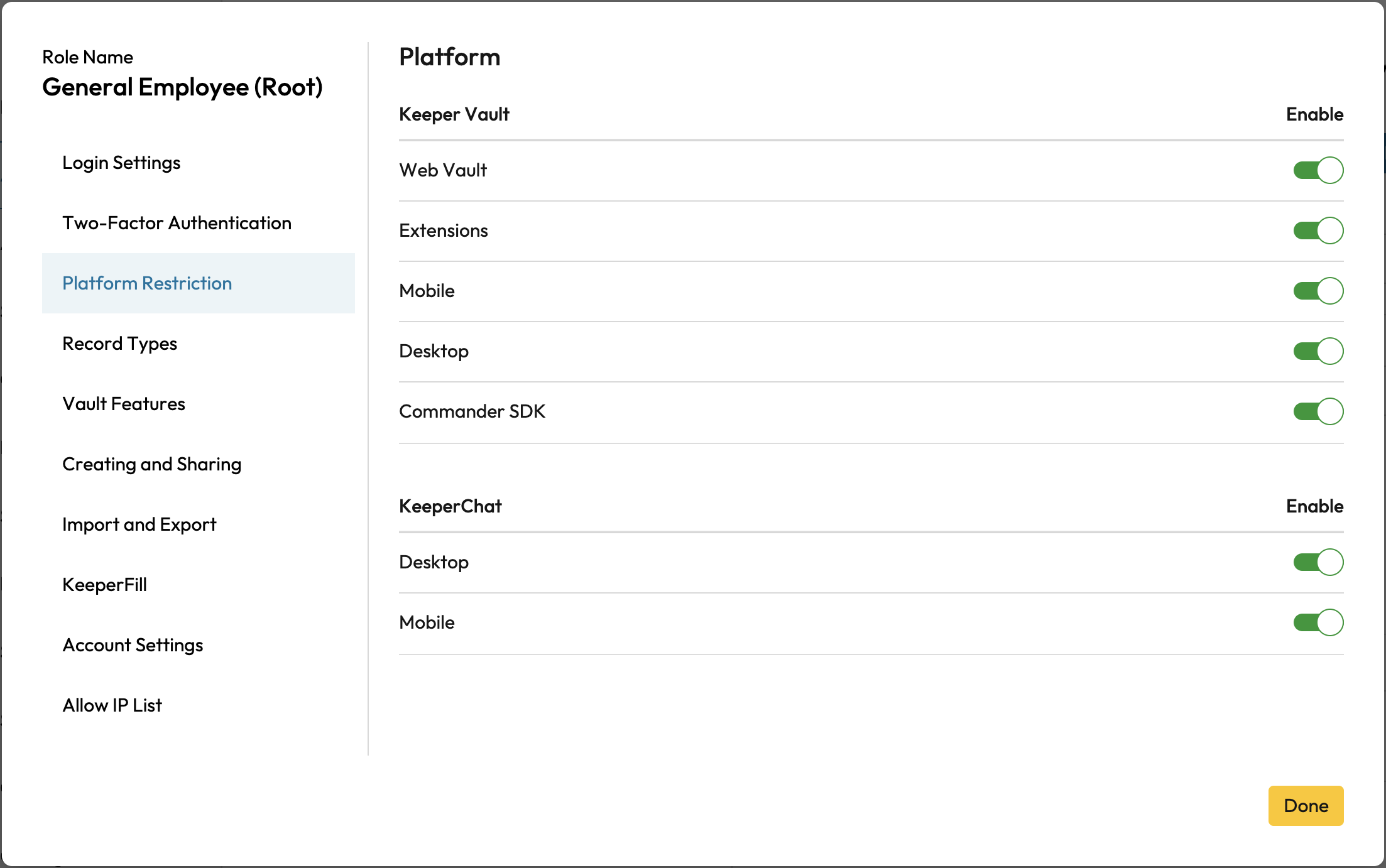
Platform Restriction Enforcements
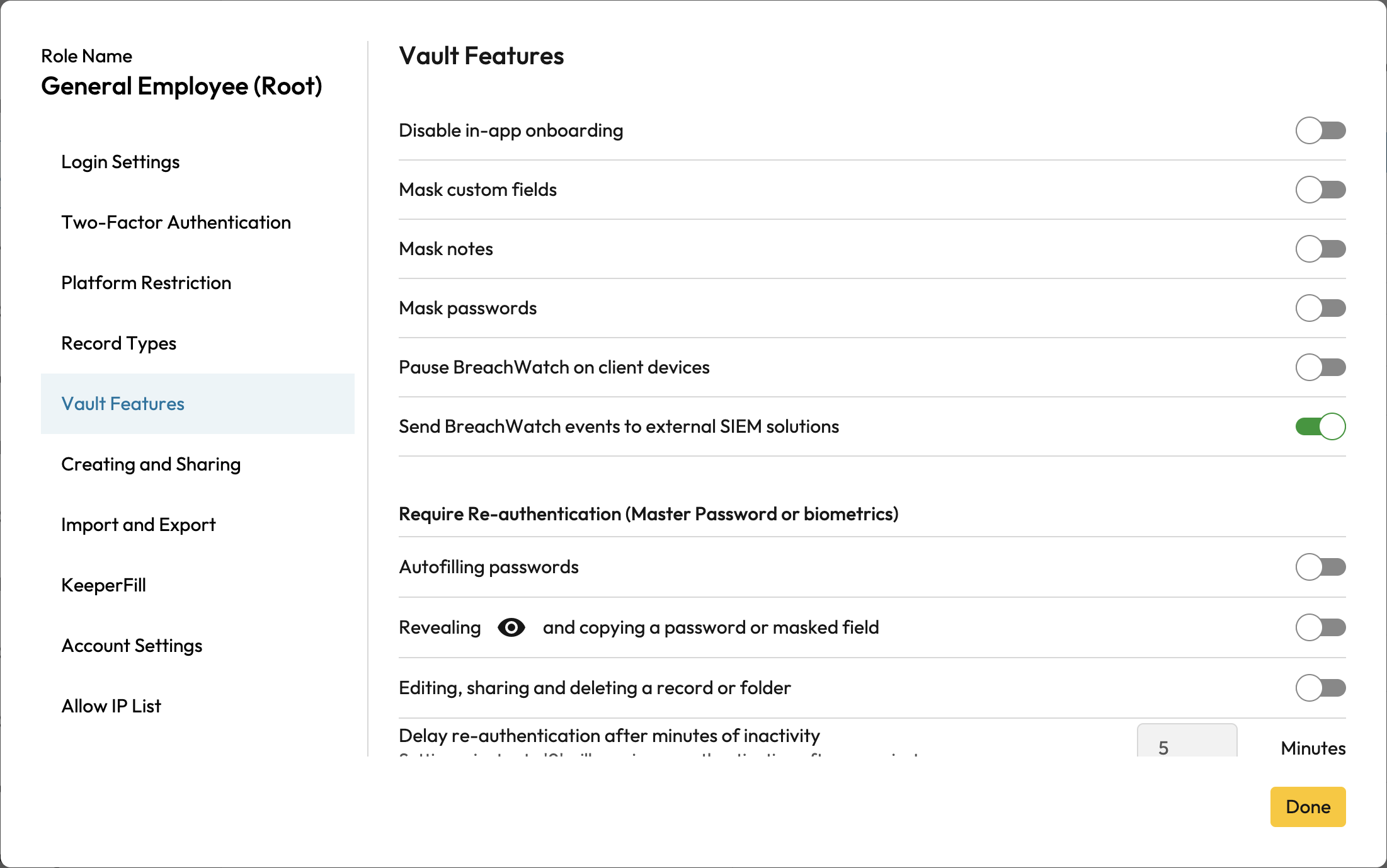
Vault Features Enforcements
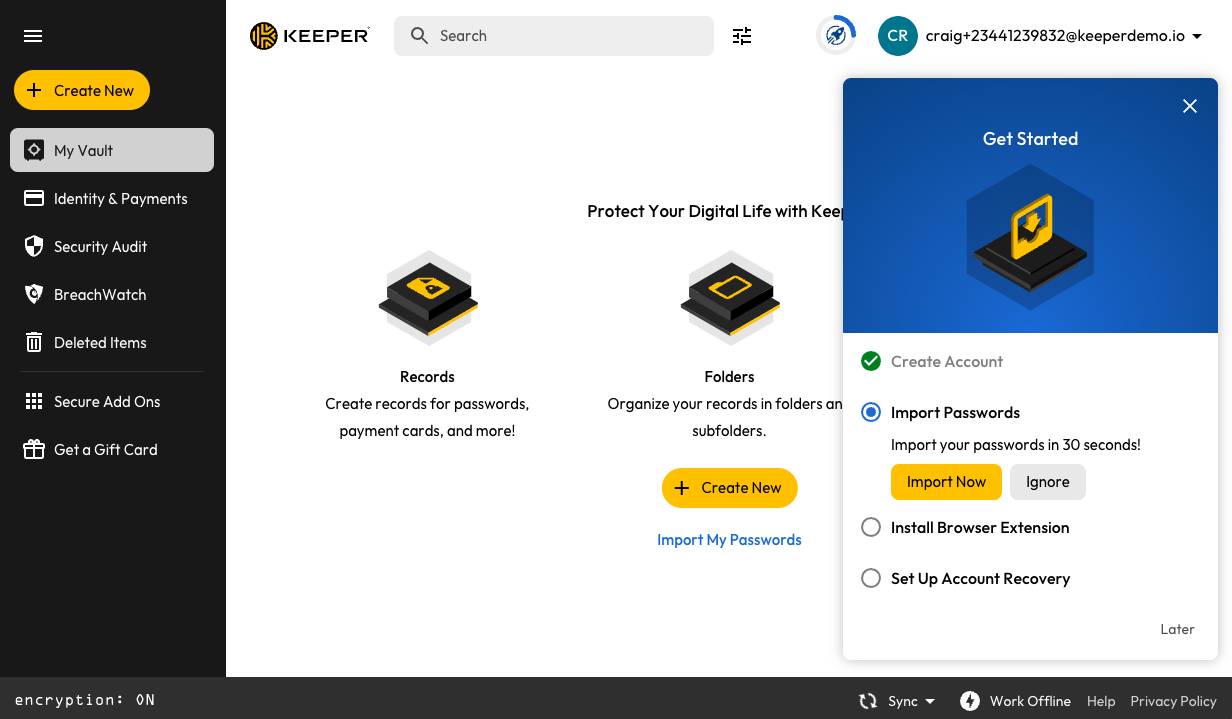
In-App Onboarding Example
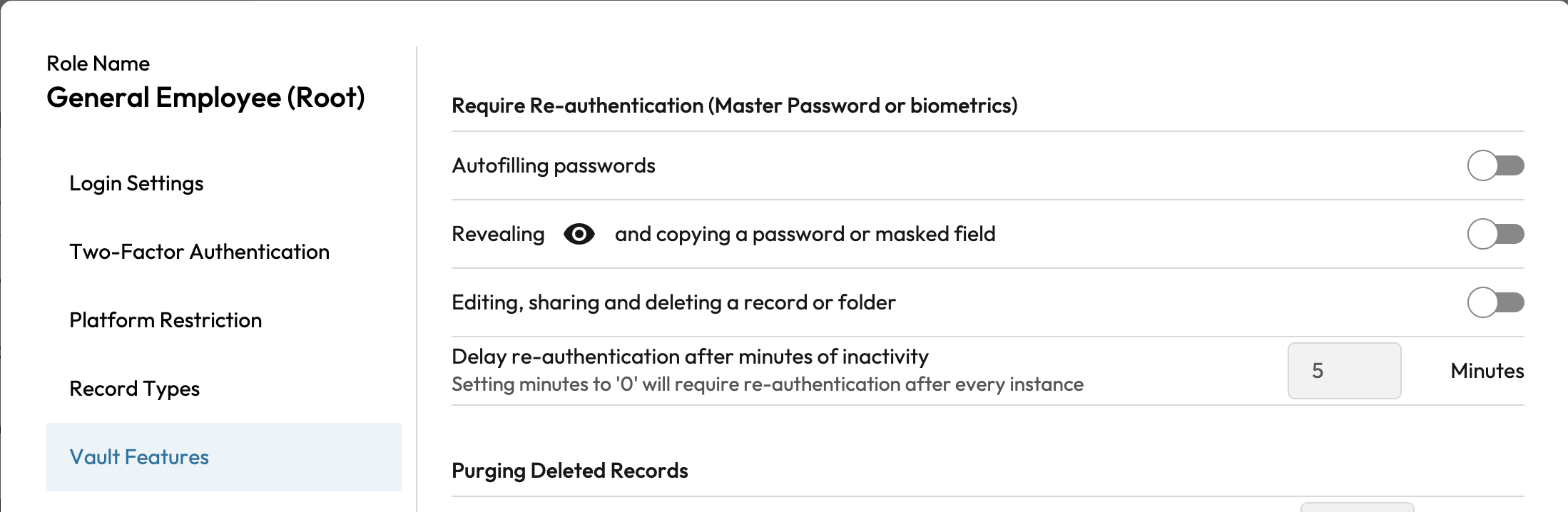
Vault Features > Re-authentication
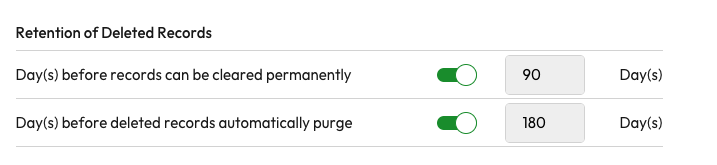
Retention of Deleted Records
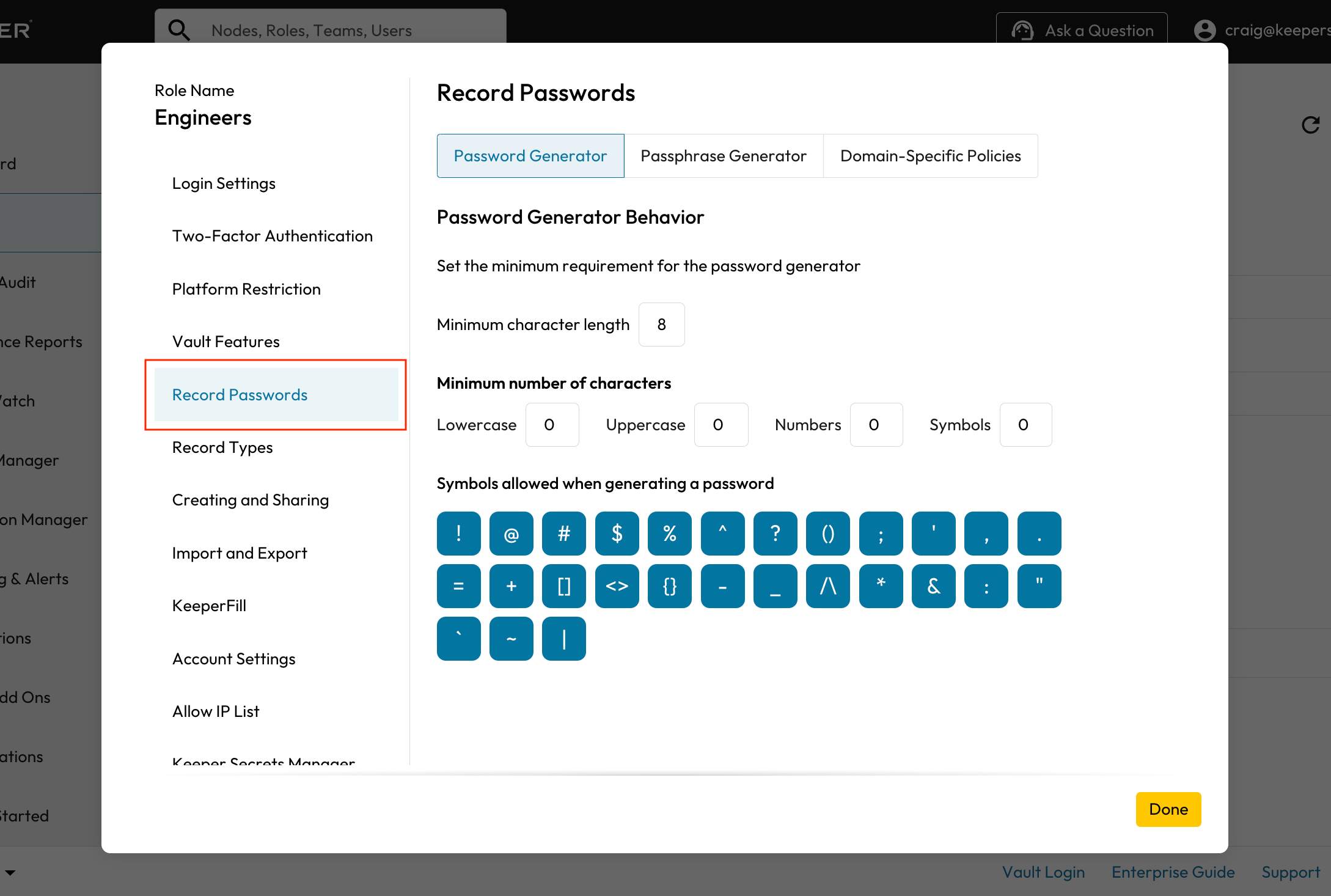
Record Passwords
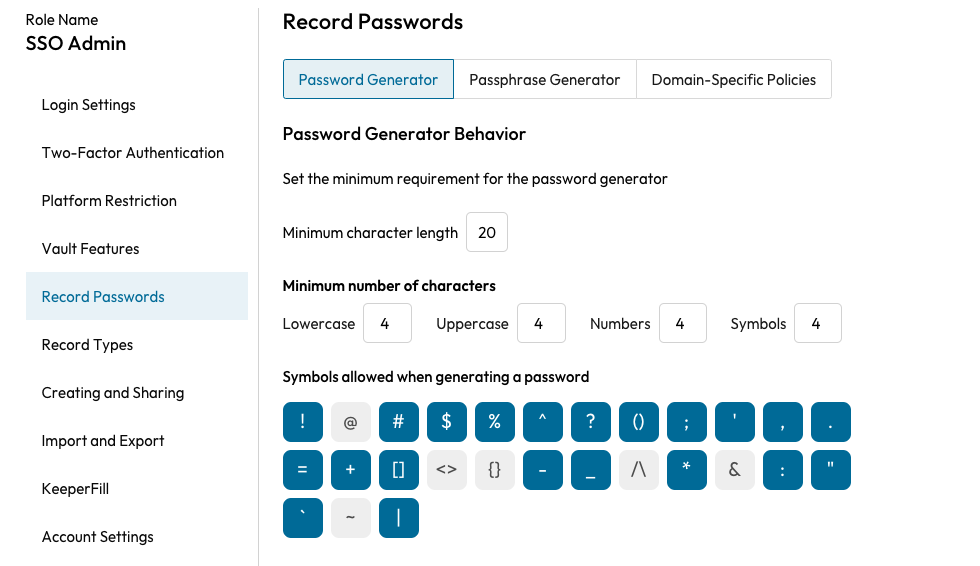
Password Generator Policy

Passphrase Generator Policy

Domain-Specific Policies

Add Domain-Specific Password or Passphrase Policy

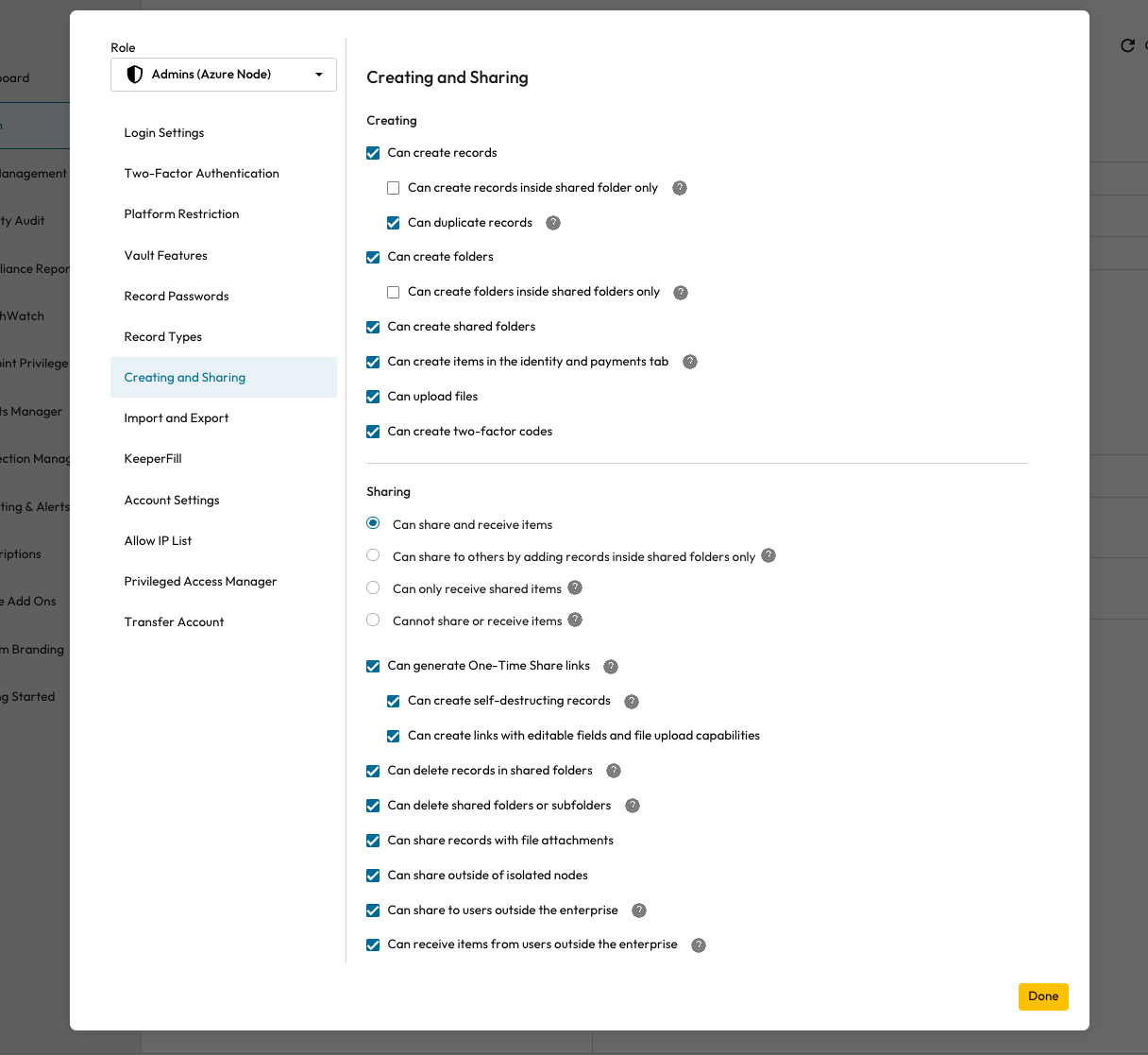
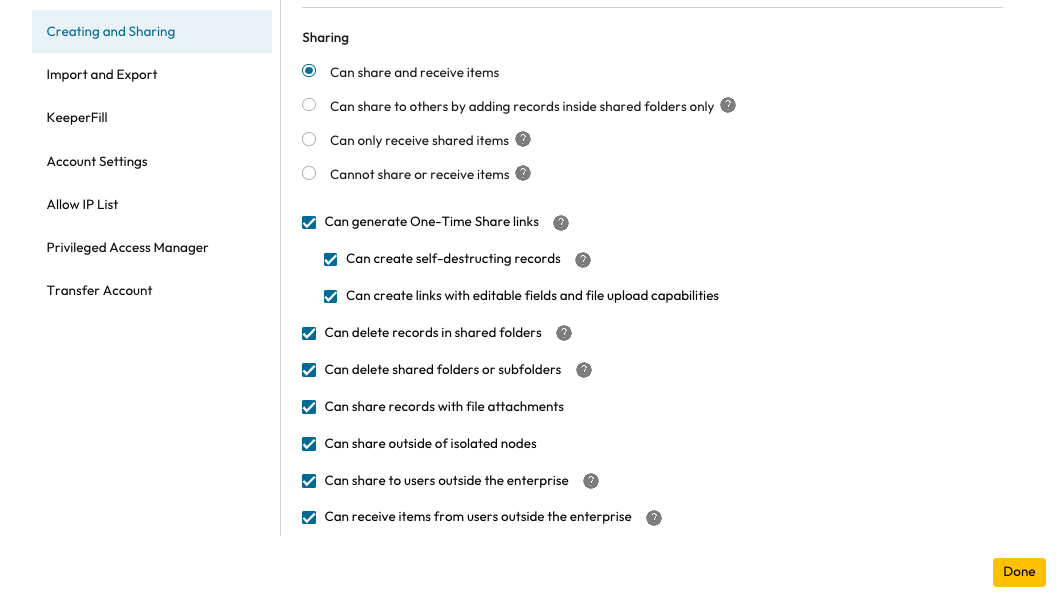
Record Type Enforcements
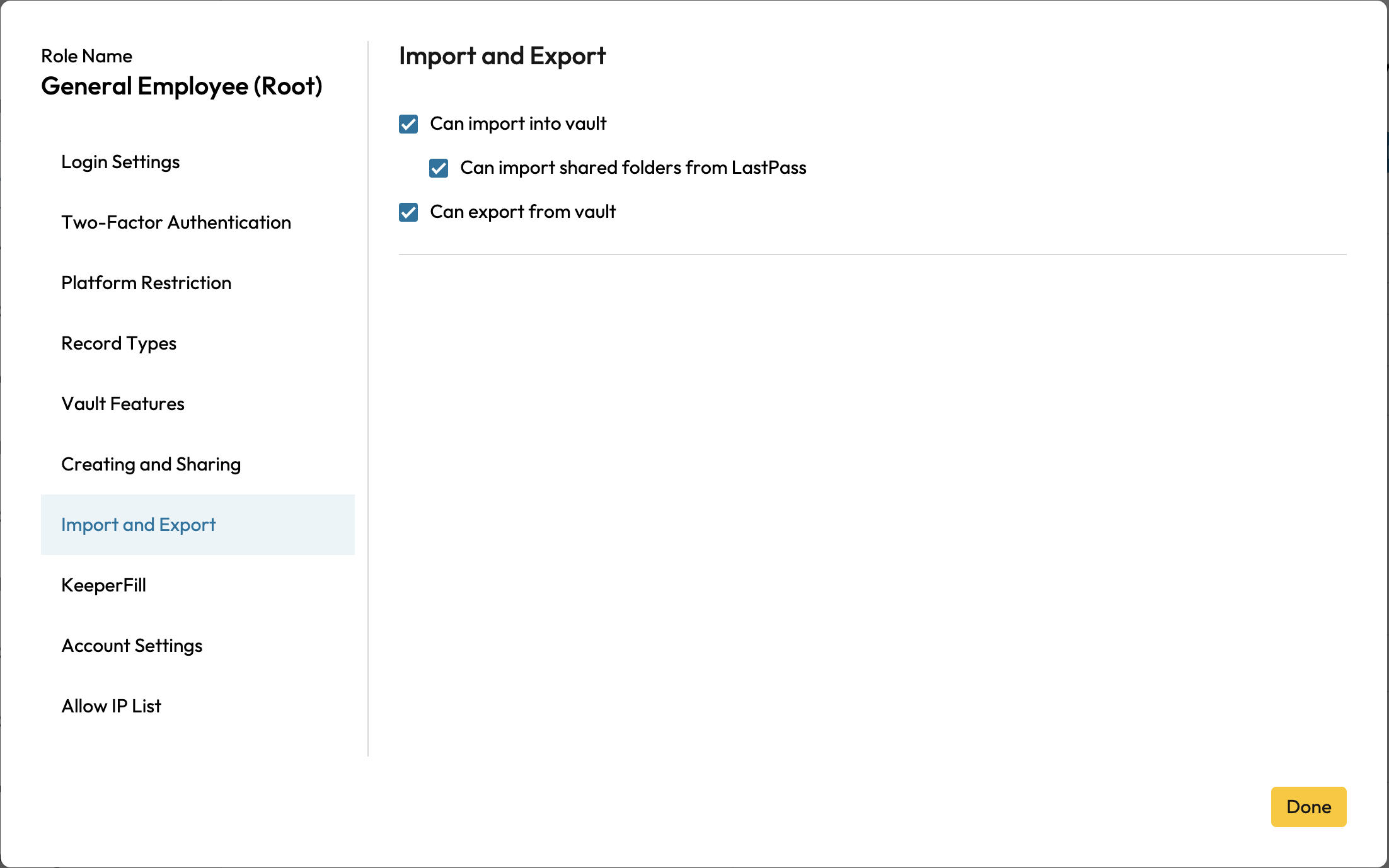
Import and Export Enforcements

KeeperFill Browser Extension
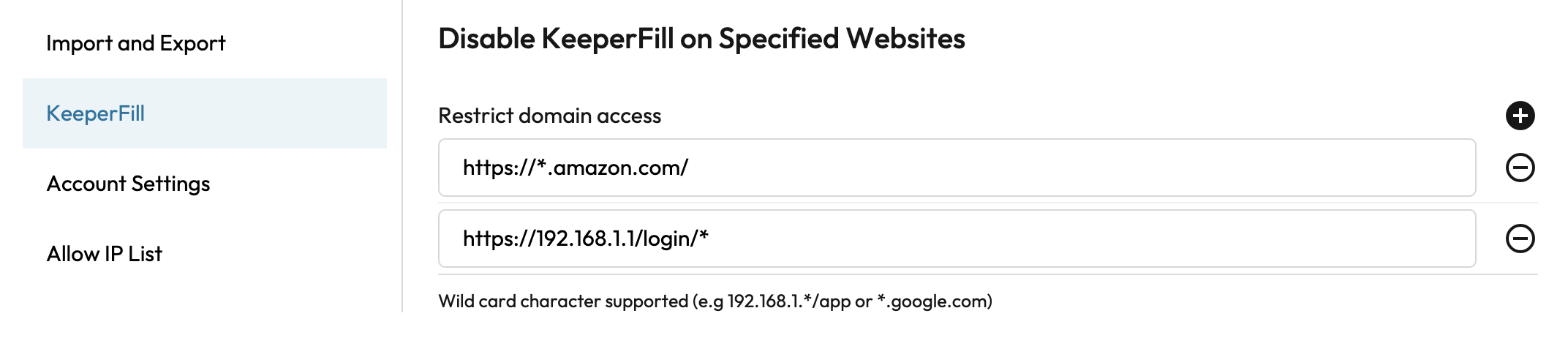
Disable KeeperFill on Specific Websites
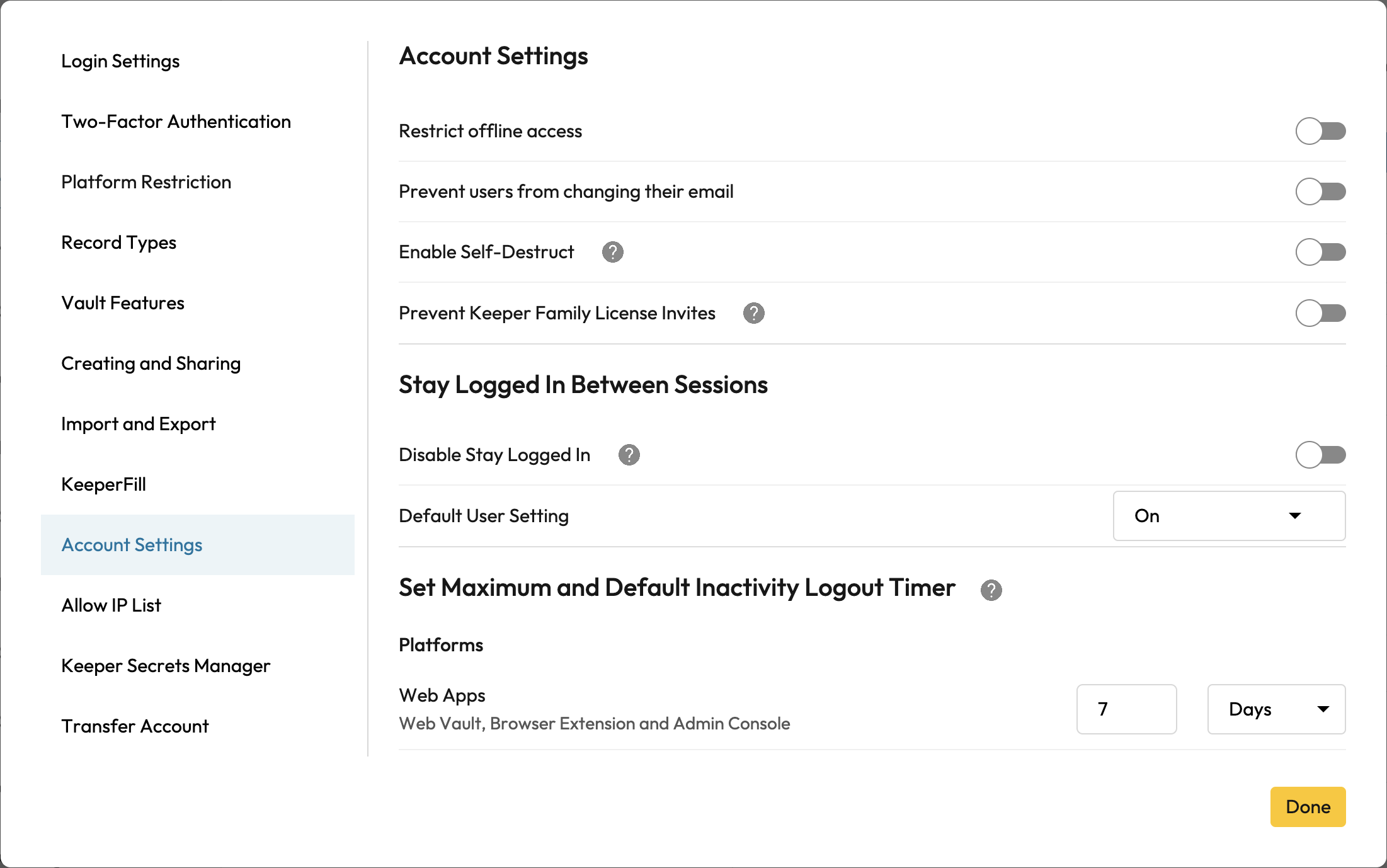
Account Settings Enforcements

Account Settings Enforcements
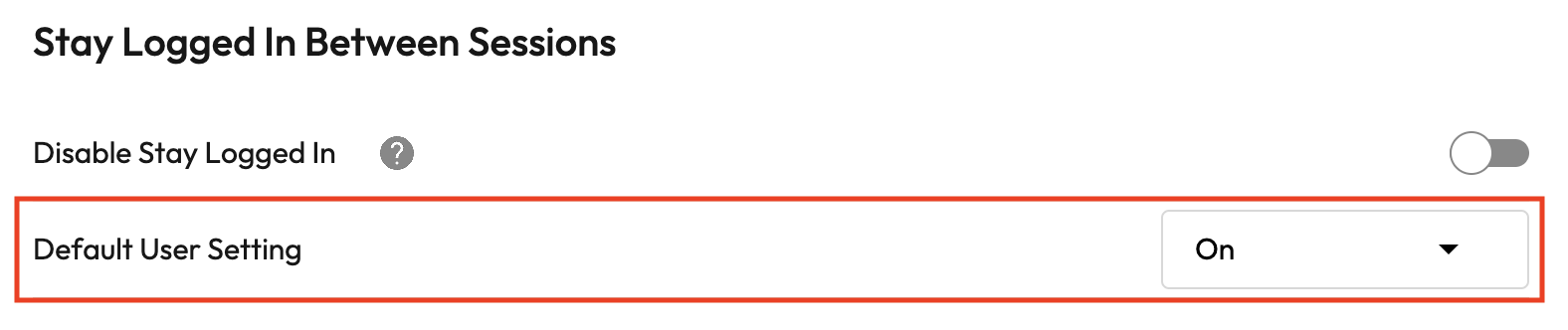
Account Settings > Stay Logged In Between Sessions & Default User Setting

Account Settings > Set Maximum and Default Inactivity Logout Timer
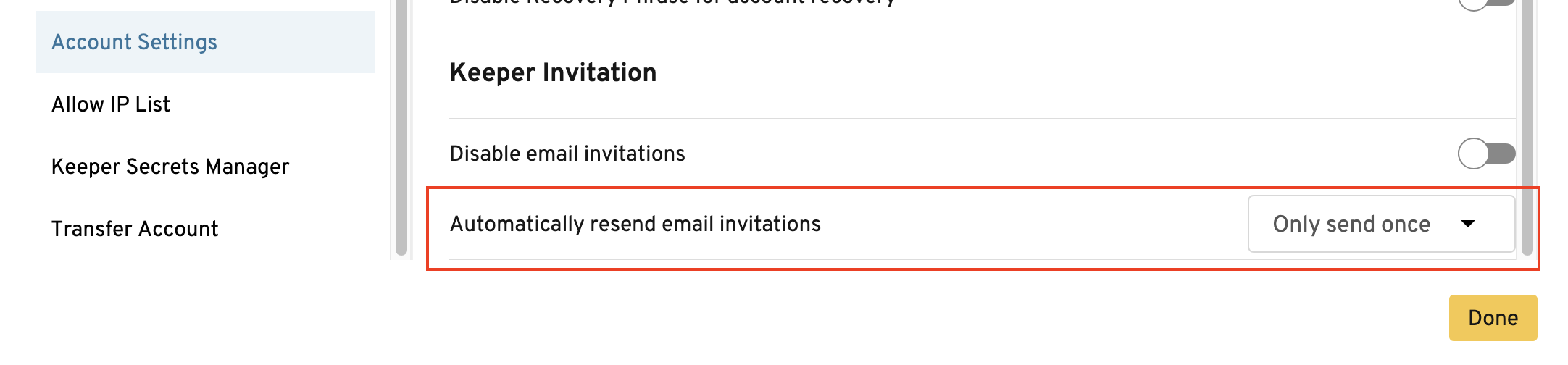
Account Settings > Keeper Invitation & Frequency
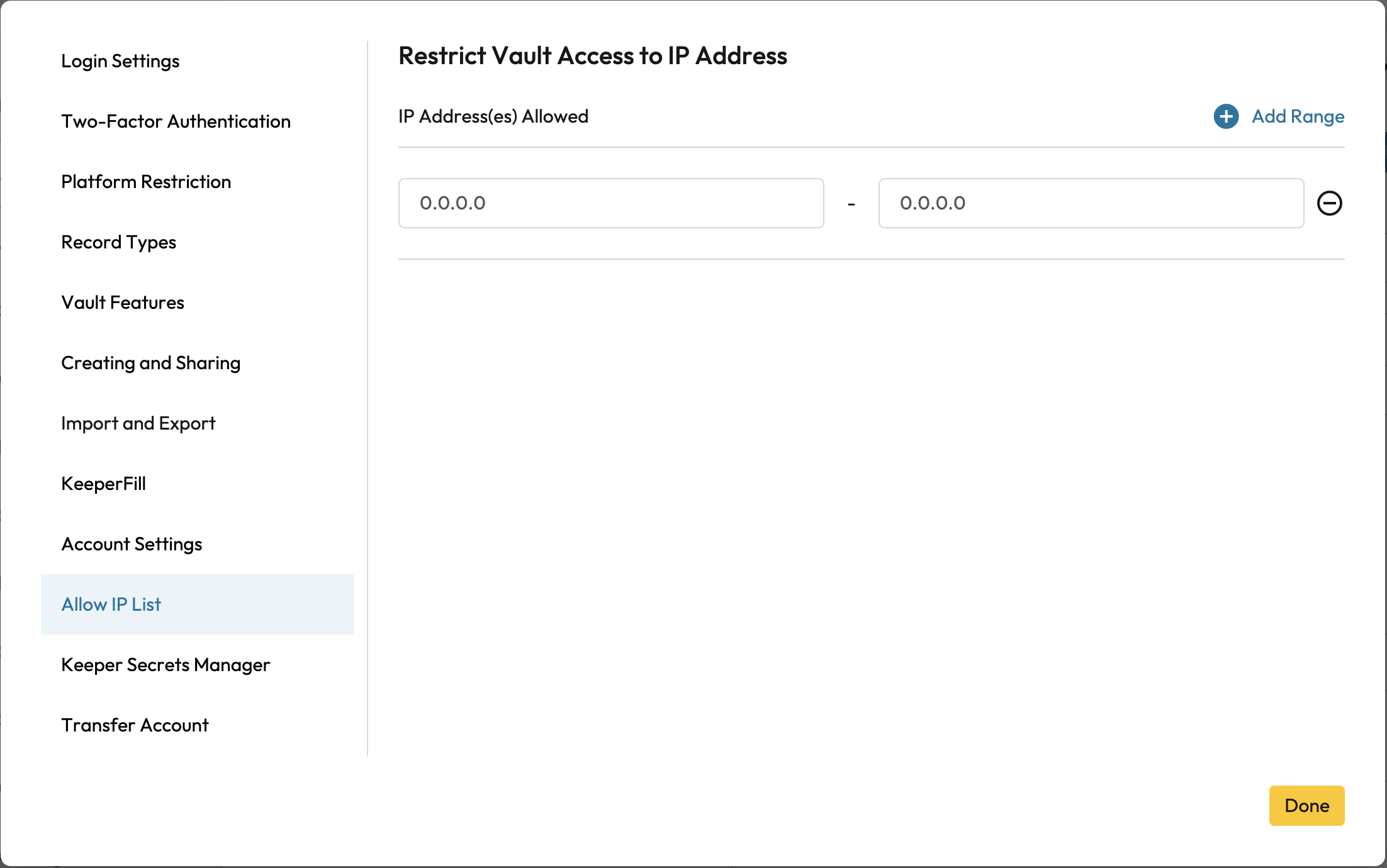
Allow IP List Enforcements

Keeper Secrets Manager Enforcements

Privileged Access Manager
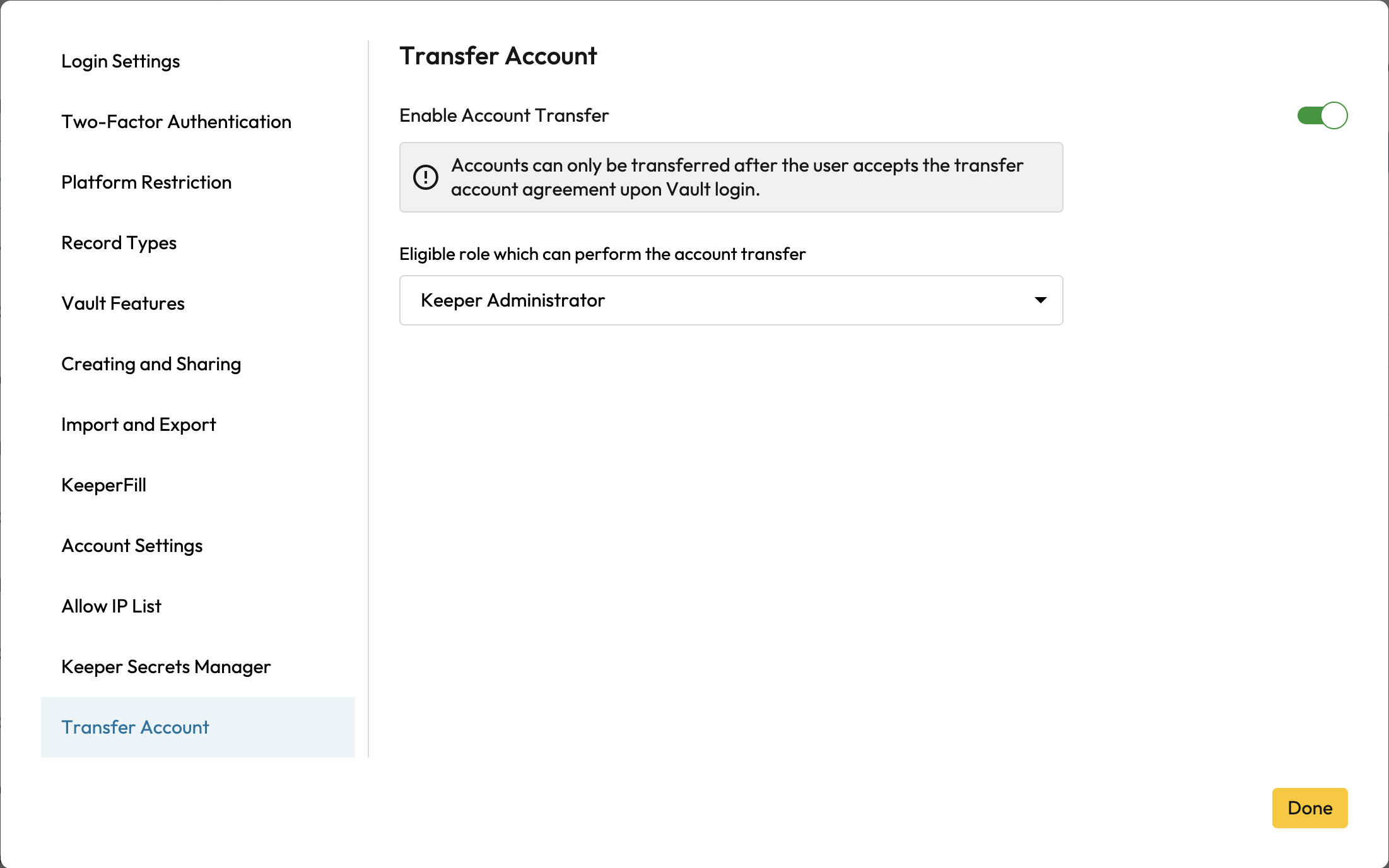
Transfer Account Enforcements