

| Field | Description | |
|---|---|---|
| Title | Configuration name, example: Azure AD Configuration | |
| Environment | Select: Azure | |
| Gateway | Select the Gateway that is configured on the Keeper Secrets Manager application and has network access to your Active Directory server from the pre-requisites | |
| Application Folder | Select the Shared folder where the PAM Configuration will be stored. We recommend placing this in a shared folder with the admin accounts. | |
| Azure ID | A unique ID for this instance of Azure. This is for your reference and can be anything, but its recommended to be kept short Ex: Azure-1 | |
| Client ID | The unique Application (client) ID assigned to your app by Azure AD when the application was registered | |
| Client Secret | The client credentials secret for the Azure application. It’s random looking text. | |
| Subscription ID | The UUID that identifies your subscription (i.e. Pay-As-You-GO) to use Azure services. | |
| Tenant ID | The UUID of the Azure Active Directory |
| Field | Description |
|---|---|
| Title | Keeper record title i.e. Azure User1 |
| Login | Case sensitive username of the account being rotated. The username has to be in one of the following formats:domain\username username@domain |
| Password | Providing a password is optional. Performing a rotation will set one if this field is left blank. |

Rotation Settings
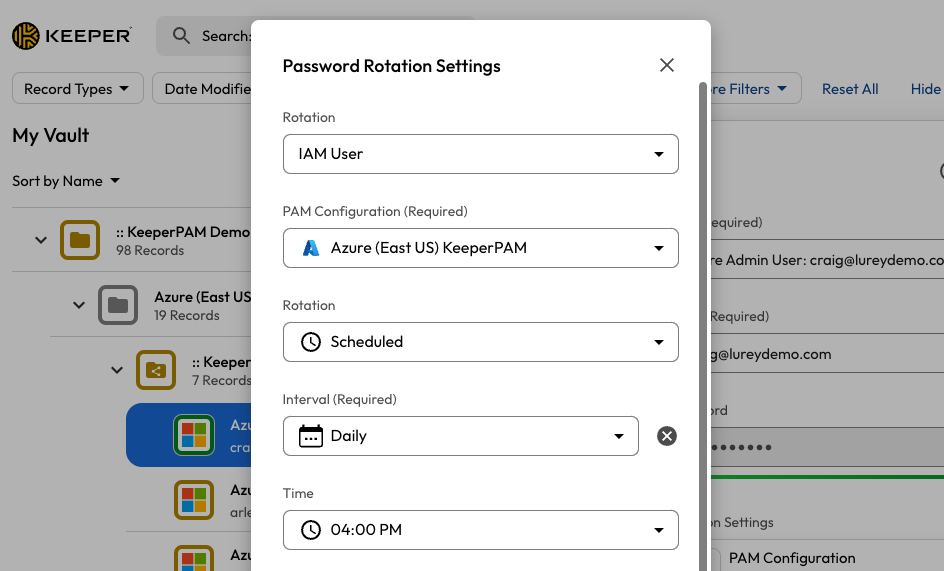
Rotation Settings for Azure AD Users